 This week marks the premiere of the major motion picture Allegiant, the third installment of the popular sci-fi trilogy The Divergent Series. Those familiar with the movies (or the books) know the underlying theme involves dividing people into factions based on common human traits - Dauntless (brave), Amity (peaceful), Erudite (intelligent), Abnegation (selfless), and Candor (honest). And while almost everyone falls into one of these groups, there are a rare few that don’t fit in – these are the divergents.
Within the context of cyber security, organizations are continually on the lookout for better ways to identify when and where an attack may occur, and by whom. Do you have a way to predict security threats in your environment? Would you like to be able to group your assets, users and events together in order to spot your security divergents?
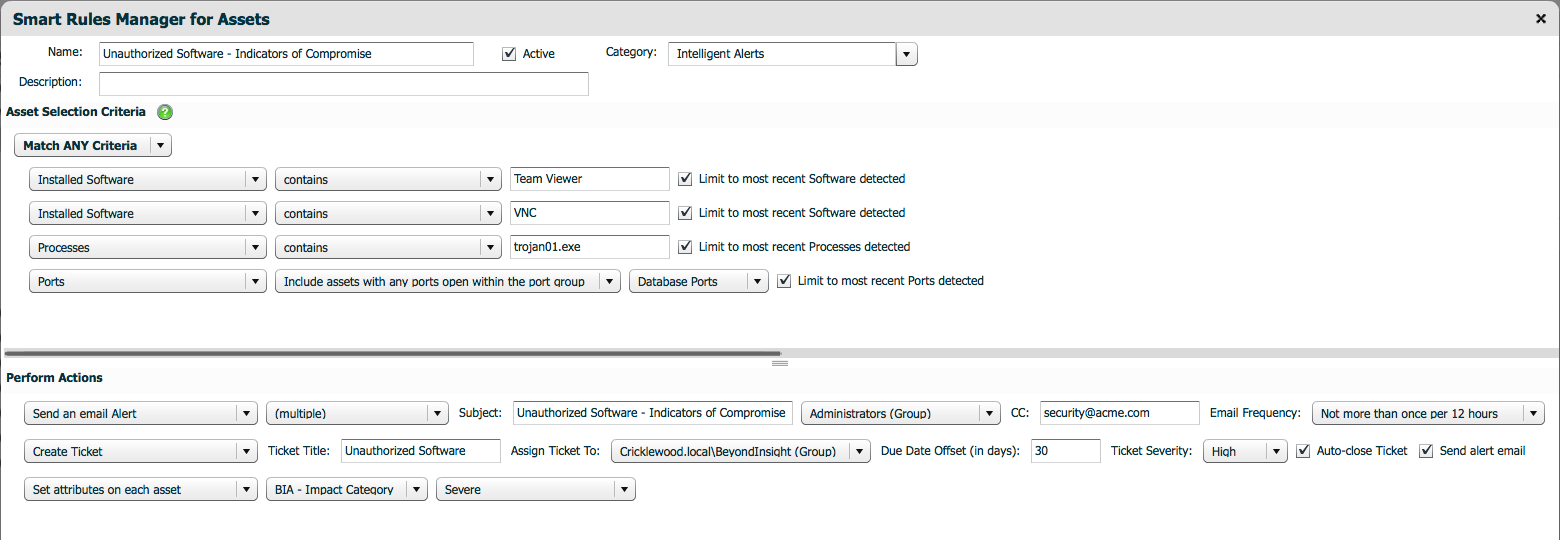
Retina CS provides Smart Rules that allow organizations to automatically create groups of like assets, based on their pre-defined criteria such as an IP range, operating systems, open ports and critical vulnerabilities. By looking at these assets within groups, you can more easily flag unknown applications, detect known threats and identify high risk assets, so that they can be brought up to code or quarantined as quickly as possible.
Need help in identifying who’s not playing by your rules? Try Retina CS for free!
This week marks the premiere of the major motion picture Allegiant, the third installment of the popular sci-fi trilogy The Divergent Series. Those familiar with the movies (or the books) know the underlying theme involves dividing people into factions based on common human traits - Dauntless (brave), Amity (peaceful), Erudite (intelligent), Abnegation (selfless), and Candor (honest). And while almost everyone falls into one of these groups, there are a rare few that don’t fit in – these are the divergents.
Within the context of cyber security, organizations are continually on the lookout for better ways to identify when and where an attack may occur, and by whom. Do you have a way to predict security threats in your environment? Would you like to be able to group your assets, users and events together in order to spot your security divergents?
Retina CS provides Smart Rules that allow organizations to automatically create groups of like assets, based on their pre-defined criteria such as an IP range, operating systems, open ports and critical vulnerabilities. By looking at these assets within groups, you can more easily flag unknown applications, detect known threats and identify high risk assets, so that they can be brought up to code or quarantined as quickly as possible.
Need help in identifying who’s not playing by your rules? Try Retina CS for free!
- Recognize systems with open ports including 1521 or 1433 that can then be categorized as “database servers.”
- Alert security staff and assign tickets to high-risk vulnerabilities, unknown ports in production systems, unauthorized software like Team Viewer, VNC, P2P clients, and more.
- Create risk indicators that generate alerts if detected, including systems with unauthorized software installed, open exploitable ports like 6667 and active processes such as conficker.exe or malware01.exe.
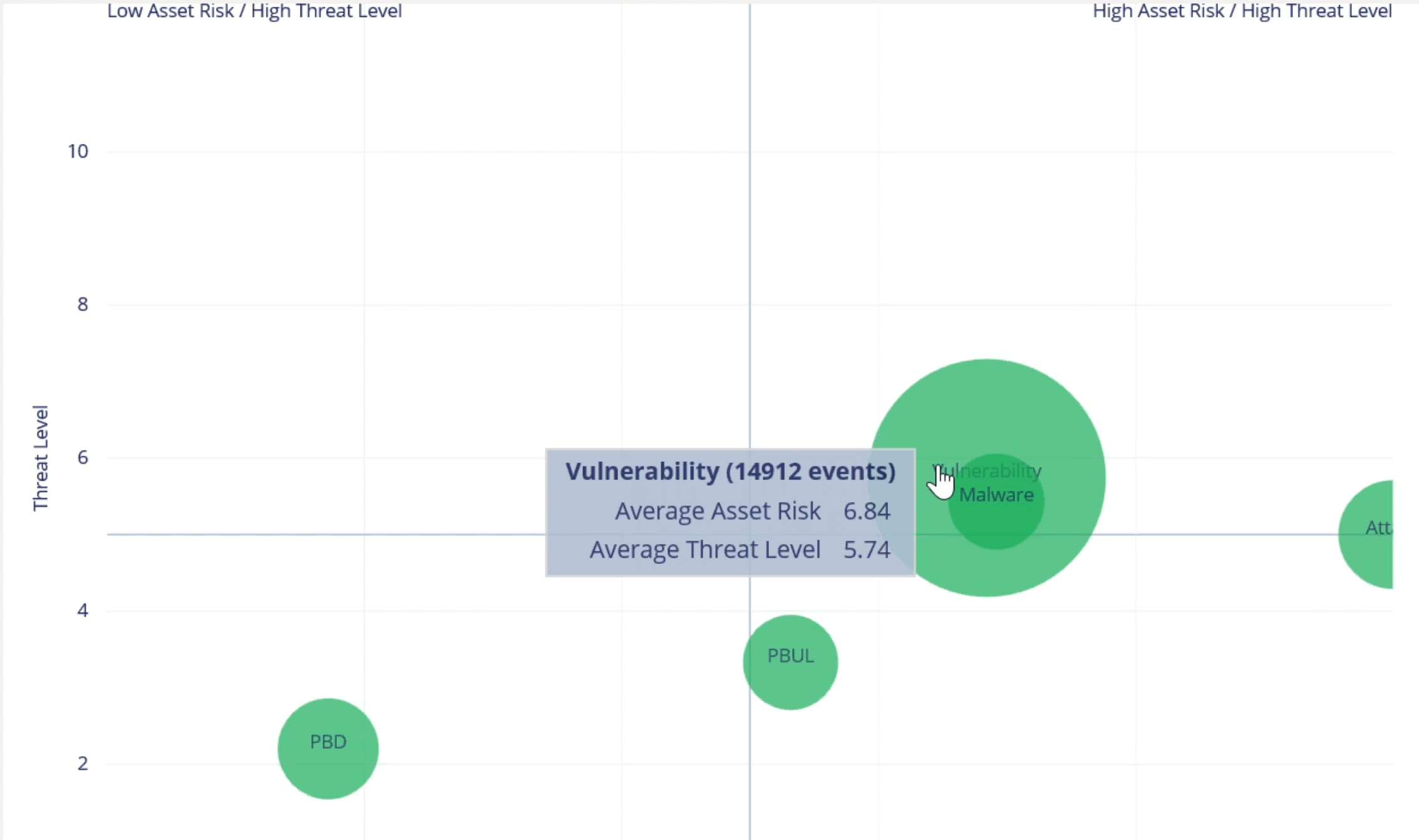
 While putting assets and users into like groups helps you quickly identify known risks, it does little to inform you about unknown and emerging threats. To do that, you must be able to link isolated events together, set baselines for normal behavior, and observe changes over time.
BeyondInsight Clarity, the advanced analytics engine behind Retina CS, does exactly that - empowering IT and security professionals to identify data breach threats typically missed.
An application is launched for the first time. An administrator logs in at 2am. A server has unpatched vulnerabilities. Seen individually, these events may be written off as low-risk occurrences. However, when looked at together, these seemingly innocuous incidents can spell big trouble.
How does it work? Clarity taps into and correlates low-level privilege, vulnerability and threat data from a variety of BeyondTrust and third-party solutions to pinpoint high-risk users and assets and identify anomalies that signal critical risks, by clustering like assets with similar threat levels. Assets with like qualities will appear in high-density clusters, while outliers will appear alone, or with only a few assets.
Want to see Clarity in action? Request a demo!
While putting assets and users into like groups helps you quickly identify known risks, it does little to inform you about unknown and emerging threats. To do that, you must be able to link isolated events together, set baselines for normal behavior, and observe changes over time.
BeyondInsight Clarity, the advanced analytics engine behind Retina CS, does exactly that - empowering IT and security professionals to identify data breach threats typically missed.
An application is launched for the first time. An administrator logs in at 2am. A server has unpatched vulnerabilities. Seen individually, these events may be written off as low-risk occurrences. However, when looked at together, these seemingly innocuous incidents can spell big trouble.
How does it work? Clarity taps into and correlates low-level privilege, vulnerability and threat data from a variety of BeyondTrust and third-party solutions to pinpoint high-risk users and assets and identify anomalies that signal critical risks, by clustering like assets with similar threat levels. Assets with like qualities will appear in high-density clusters, while outliers will appear alone, or with only a few assets.
Want to see Clarity in action? Request a demo!
- Aggregate users and asset data to centrally baseline and track behavior
- Correlate diverse asset, user and threat activity to reveal critical risks
- Measure the velocity of asset changes to flag in-progress threats
- Isolate users and assets exhibiting deviant behavior
 Don’t let your adversaries hide among the masses. Assign threat levels to your events, group like assets and users into clusters, monitor how they change, communicate outliers and find the security divergent among you.
Need more information? Download our latest white paper, 10 Reasons to Rethink Your Vulnerability Management, and see how Retina’s cutting-edge capabilities can keep you steps ahead of the bad guys.
For more, contact us today!
Don’t let your adversaries hide among the masses. Assign threat levels to your events, group like assets and users into clusters, monitor how they change, communicate outliers and find the security divergent among you.
Need more information? Download our latest white paper, 10 Reasons to Rethink Your Vulnerability Management, and see how Retina’s cutting-edge capabilities can keep you steps ahead of the bad guys.
For more, contact us today!

Scott Lang, Sr. Director, Product Marketing at BeyondTrust
Scott Lang has nearly 20 years of experience in technology product marketing, currently guiding the product marketing strategy for BeyondTrust’s privileged account management solutions and vulnerability management solutions. Prior to joining BeyondTrust, Scott was director of security solution marketing at Dell, formerly Quest Software, where he was responsible for global security campaigns, product marketing for identity and access management and Windows server management.








