Retina from BeyondTrust performs vulnerability assessment of VMware solutions so incredibly, extremely, amazingly much better than anyone else.... Ok, I'm in product management and maybe marketing isn’t my forte, but let me explain to you in all seriousness why I think we've done something pretty special here. First, let me pose some real world questions every company running virtualization technology should ask themselves so we can all level set;
- How do you perform vulnerability assessment of your virtualized guests and hosts?
- Do you have a scan engine that targets each virtual machine and hypervisor with just like a normal physical asset?
- Do you treat virtual applications the same way as installed programs for assessment ?
- How do you assess offline images ? Do you have to power them all on to scan them ?
- Do you empower virtual server administrators with security tools to assess the risk of guest sessions ?
- Can you manage images uniquely if they are replicate ?
Recently, BeyondTrust did a vulnerability management survey of end users that use virtualization technology and the results where rather surprising. Many organizations are blind to the unique risks virtualized technology can pose to an organization and even more are stymied by the tools they have to manage them. In addition, many end users do not address the unique characteristics of virtualized technology in their security best practices and assessments. When it all comes together, it seems that the security teams within many companies are just not talking to server and virtual server administrators about risk. There is a process gap and islands of operation that need to begin working together to solve the real world problems of virtualization technology.
Based on this enlightenment, BeyondTrust has been building the most complete vulnerability assessment technology for VMware found on the market today. Here is why:
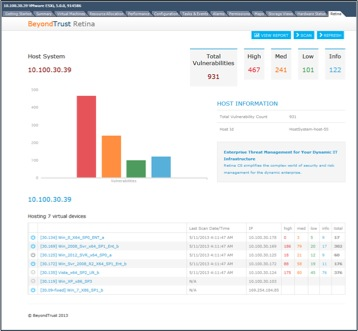
- Retina can perform assessments on virtualized devices and identify if the host is a virtual or physical device.
- Retina can target virtual machines by communicating directly with vCenter to determine which Guests are installed and which ones are powered on.
- Retina can perform vulnerability assessments on VMware ThinApps.
- Retina can assess for vulnerabilities of Windows VMware images even if the image is powered off. In addition, Retina can optionally power on any image, change the network adapter to a private network, perform an assessment, and power the image back off for a complete assessment process fully automated.
- Retina identifies virtual guests with a unique identify so even cloned or images based on the same template can be tracked as separate assets within the solution.
No other vulnerability management vendor can handle the unique challenges of a virtualized environment like BeyondTrust. No one else has tools to address these issues and an enterprise architecture that can manage the most complex virtualized environments. Retina is the best product for vulnerability assessment of VMware and BeyondTrust is the best company to do it. Let us prove it to you.

Morey J. Haber, Chief Security Advisor
Morey J. Haber is the Chief Security Advisor at BeyondTrust. As the Chief Security Advisor, Morey is the lead identity and technical evangelist at BeyondTrust. He has more than 25 years of IT industry experience and has authored four books: Privileged Attack Vectors, Asset Attack Vectors, Identity Attack Vectors, and Cloud Attack Vectors. Morey has previously served as BeyondTrust’s Chief Security Officer, Chief Technology, and Vice President of Product Management during his nearly 12-year tenure. In 2020, Morey was elected to the Identity Defined Security Alliance (IDSA) Executive Advisory Board, assisting the corporate community with identity security best practices. He originally joined BeyondTrust in 2012 as a part of the acquisition of eEye Digital Security, where he served as a Product Owner and Solutions Engineer, since 2004. Prior to eEye, he was Beta Development Manager for Computer Associates, Inc. He began his career as Reliability and Maintainability Engineer for a government contractor building flight and training simulators. Morey earned a Bachelor of Science degree in Electrical Engineering from the State University of New York at Stony Brook.








