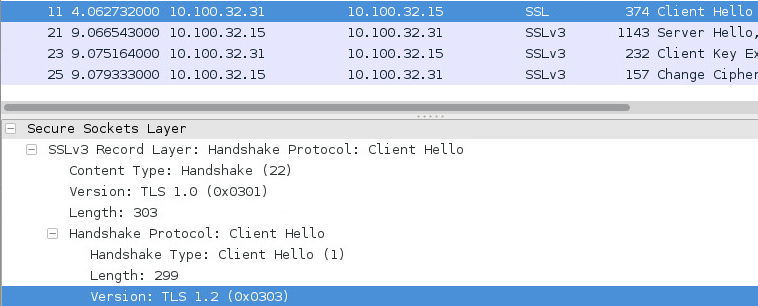
 The server may respond with a lower version, such as SSL 3.0:
The server may respond with a lower version, such as SSL 3.0:
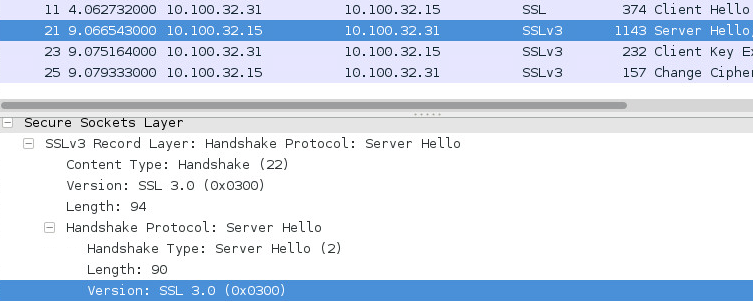 If the client supports SSL 3.0, the handshake will continue and a session is established. A Man-In-The-Middle (MITM) attacker can simulate this process by intercepting a TLS handshake, manipulating the packets, and forwarding them so that SSLv3 is used.
Once an SSL 3.0 session has been established, the encryption schemes can be exploited. The vulnerability with SSL 3.0 is that it uses the RC4 stream cipher or a block cipher in CBC mode. The problem with RC4 streams is that they contain biases, so that if the same data is sent repeatedly, more and more information is leaked. A good candidate for this would be HTTP session cookies, which hold potentially sensitive information and are sent with virtually every HTTP request during an established session.
The issue with CBC encryption is that the integrity of its block cipher padding cannot be validated upon decryption. Because a MITM attacker can intercept and manipulate the request sent to the server, they can essentially brute force the requests until the server accepts, gaining a byte of information at a time. It was shown that, on average, the server will accept the modified record once every 256 requests.
Currently, the only real solution to protect against this attack is to disable SSL 3.0 support entirely. However, this may prove to be impractical because many systems still utilize it. Therefore, an alternative solution is to update TLS clients to include TLS_FALLBACK_SCSV value into the client hello cipher suites, which will ensure a downgrade attack cannot occur. However, be aware that this will not protect servers/clients that only support SSL 3.0.
Retina Network Security Scanner (RNSS) Audit Release version 2825 contains two relevant audits:
35467 - SSLv3 Fallback Vulnerability (POODLE)
35468 - Microsoft SSLv3 Information Disclosure (3009008)
If the client supports SSL 3.0, the handshake will continue and a session is established. A Man-In-The-Middle (MITM) attacker can simulate this process by intercepting a TLS handshake, manipulating the packets, and forwarding them so that SSLv3 is used.
Once an SSL 3.0 session has been established, the encryption schemes can be exploited. The vulnerability with SSL 3.0 is that it uses the RC4 stream cipher or a block cipher in CBC mode. The problem with RC4 streams is that they contain biases, so that if the same data is sent repeatedly, more and more information is leaked. A good candidate for this would be HTTP session cookies, which hold potentially sensitive information and are sent with virtually every HTTP request during an established session.
The issue with CBC encryption is that the integrity of its block cipher padding cannot be validated upon decryption. Because a MITM attacker can intercept and manipulate the request sent to the server, they can essentially brute force the requests until the server accepts, gaining a byte of information at a time. It was shown that, on average, the server will accept the modified record once every 256 requests.
Currently, the only real solution to protect against this attack is to disable SSL 3.0 support entirely. However, this may prove to be impractical because many systems still utilize it. Therefore, an alternative solution is to update TLS clients to include TLS_FALLBACK_SCSV value into the client hello cipher suites, which will ensure a downgrade attack cannot occur. However, be aware that this will not protect servers/clients that only support SSL 3.0.
Retina Network Security Scanner (RNSS) Audit Release version 2825 contains two relevant audits:
35467 - SSLv3 Fallback Vulnerability (POODLE)
35468 - Microsoft SSLv3 Information Disclosure (3009008)

Scott Lang, Sr. Director, Product Marketing at BeyondTrust
Scott Lang has nearly 20 years of experience in technology product marketing, currently guiding the product marketing strategy for BeyondTrust’s privileged account management solutions and vulnerability management solutions. Prior to joining BeyondTrust, Scott was director of security solution marketing at Dell, formerly Quest Software, where he was responsible for global security campaigns, product marketing for identity and access management and Windows server management.








