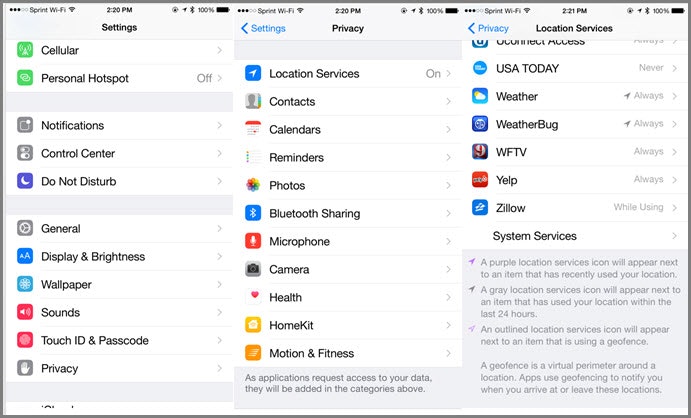
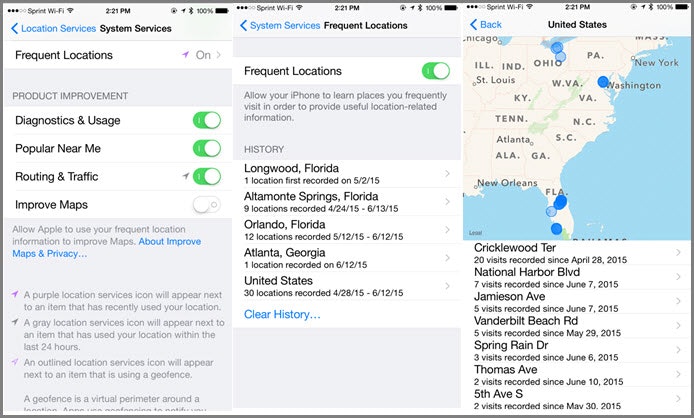
 Layered 6 menus deep, Apple iOS 8 is tracking all of your locations, and even displays on a map, the most recent locations you have visited. Seems kind of scary, huh? Did you know these settings are on by default, and as an end user, you accepted them as a part of the large license agreement when you powered on your phone for the first time? I certainly did not. Luckily, these can easily be turned off flipping the switch for “Frequent Locations” to off.
Now here is the problem. We all (for the most part) want to maintain our data privacy. But, how can we possibly when data like this is being collected, oh so cleverly nested pages down in the device that the average user has no idea what they are, how to turn them off, or that they are even present in the first place? Hence the hypocrisy, or possibly, the ignorance. I think most people are just unaware that companies and technology are tracking this much information. When they find out, they will turn it off.
Personally, I am hypocrite. I am fearful of all the personal information that is out there and believe in strict data privacy. But, I really do love having this technology and the benefits it provides. For example, after the Rolling Stones concert in Orlando last weekend, it took only 9 minutes for an Uber driver to find all 5 of us and get us home after midnight. For that convenience, I will leave my Location Services on. I am not fearful someone will find me in the wrong place, I have done nothing wrong, so why do I have to worry if all this information is collected. Right?
Unfortunately, there are some very distorted individuals in the world. There are a dozen ways to the moon that this information could be harmful if collected in bulk or in targeting a single individual or family. Everything from robbing my house when a thief knows I am out of town to potentially kidnapping high valued targets. The data may be convenient when used the correct way, but could be disastrous if abused. This is why at least I live in a world with hypocrisy for data privacy. If nothing else, we should all be aware that this type of problem is really out there.
I can only hope that devices like these learn the value of role based access and least privilege technology to properly safe guard personal information. Right now, outside of parental controls, everyone is admin and the data is just hanging out there for any hacker to get a hold of. Luckily traditional computing devices like workstations and servers due have these controls and can protect the data, application, asset, and user at multiple levels. BeyondTrust has a full offering of Privileged Account Management solutions that can help any organization with managing least privilege.
Layered 6 menus deep, Apple iOS 8 is tracking all of your locations, and even displays on a map, the most recent locations you have visited. Seems kind of scary, huh? Did you know these settings are on by default, and as an end user, you accepted them as a part of the large license agreement when you powered on your phone for the first time? I certainly did not. Luckily, these can easily be turned off flipping the switch for “Frequent Locations” to off.
Now here is the problem. We all (for the most part) want to maintain our data privacy. But, how can we possibly when data like this is being collected, oh so cleverly nested pages down in the device that the average user has no idea what they are, how to turn them off, or that they are even present in the first place? Hence the hypocrisy, or possibly, the ignorance. I think most people are just unaware that companies and technology are tracking this much information. When they find out, they will turn it off.
Personally, I am hypocrite. I am fearful of all the personal information that is out there and believe in strict data privacy. But, I really do love having this technology and the benefits it provides. For example, after the Rolling Stones concert in Orlando last weekend, it took only 9 minutes for an Uber driver to find all 5 of us and get us home after midnight. For that convenience, I will leave my Location Services on. I am not fearful someone will find me in the wrong place, I have done nothing wrong, so why do I have to worry if all this information is collected. Right?
Unfortunately, there are some very distorted individuals in the world. There are a dozen ways to the moon that this information could be harmful if collected in bulk or in targeting a single individual or family. Everything from robbing my house when a thief knows I am out of town to potentially kidnapping high valued targets. The data may be convenient when used the correct way, but could be disastrous if abused. This is why at least I live in a world with hypocrisy for data privacy. If nothing else, we should all be aware that this type of problem is really out there.
I can only hope that devices like these learn the value of role based access and least privilege technology to properly safe guard personal information. Right now, outside of parental controls, everyone is admin and the data is just hanging out there for any hacker to get a hold of. Luckily traditional computing devices like workstations and servers due have these controls and can protect the data, application, asset, and user at multiple levels. BeyondTrust has a full offering of Privileged Account Management solutions that can help any organization with managing least privilege.

Morey J. Haber, Chief Security Advisor
Morey J. Haber is the Chief Security Advisor at BeyondTrust. As the Chief Security Advisor, Morey is the lead identity and technical evangelist at BeyondTrust. He has more than 25 years of IT industry experience and has authored four books: Privileged Attack Vectors, Asset Attack Vectors, Identity Attack Vectors, and Cloud Attack Vectors. Morey has previously served as BeyondTrust’s Chief Security Officer, Chief Technology, and Vice President of Product Management during his nearly 12-year tenure. In 2020, Morey was elected to the Identity Defined Security Alliance (IDSA) Executive Advisory Board, assisting the corporate community with identity security best practices. He originally joined BeyondTrust in 2012 as a part of the acquisition of eEye Digital Security, where he served as a Product Owner and Solutions Engineer, since 2004. Prior to eEye, he was Beta Development Manager for Computer Associates, Inc. He began his career as Reliability and Maintainability Engineer for a government contractor building flight and training simulators. Morey earned a Bachelor of Science degree in Electrical Engineering from the State University of New York at Stony Brook.








