 I need to make this blog personal. Recently I sold my 2015 Dodge Challenge SCAT. A beast of a vehicle with 495 HP stock. I loved the car. It was fast and drove like a full size luxury sedan on the highway – even for a muscle car. My reasons for letting it go are rather simple, but not the point of this blog. The car had the latest UConnect system from Dodge / Chrysler that was hacked in 2015 and promptly recalled. If you remember it allowed a remote attacker to take control of the vehicles brakes and other critical systems. Like a good customer, and a conscious security professional, I downloaded the firmware and flashed the control system in my car. And yes, I could do it myself, bring it into the dealer, or request a USB key from Dodge to apply the security patch to my car.
Now flash forward a few months. I sold the car in November and received a curious email a few days ago from my car’s Uconnect system (click to enlarge):
I need to make this blog personal. Recently I sold my 2015 Dodge Challenge SCAT. A beast of a vehicle with 495 HP stock. I loved the car. It was fast and drove like a full size luxury sedan on the highway – even for a muscle car. My reasons for letting it go are rather simple, but not the point of this blog. The car had the latest UConnect system from Dodge / Chrysler that was hacked in 2015 and promptly recalled. If you remember it allowed a remote attacker to take control of the vehicles brakes and other critical systems. Like a good customer, and a conscious security professional, I downloaded the firmware and flashed the control system in my car. And yes, I could do it myself, bring it into the dealer, or request a USB key from Dodge to apply the security patch to my car.
Now flash forward a few months. I sold the car in November and received a curious email a few days ago from my car’s Uconnect system (click to enlarge):
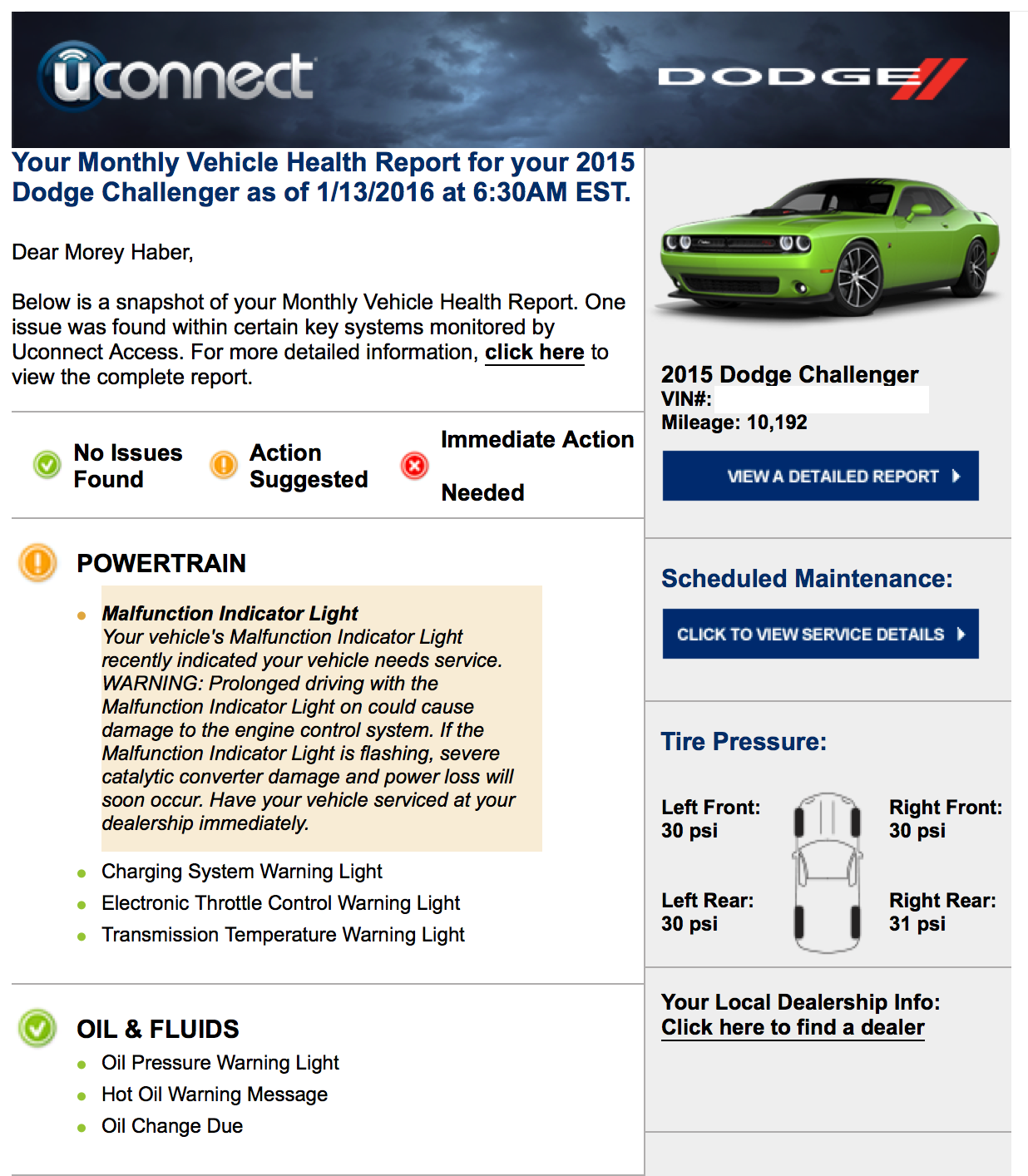 Apparently I have a powertrain issue in a car I know longer own. Unlike a cell phone that you can wipe when you sell it, there is no simple way to dissolve the connection to your old vehicle. In fact if I log into my old account on the website, I can still see quite a few details about my old vehicle and even potentially operate its GPS, doors, locks, and horn remotely. The car was never electronically disconnected from my ownership like turning in an old cell phone. The question becomes who’s responsibility is it ? Curiously, on the bottom of the email is this line (click to enlarge):
Apparently I have a powertrain issue in a car I know longer own. Unlike a cell phone that you can wipe when you sell it, there is no simple way to dissolve the connection to your old vehicle. In fact if I log into my old account on the website, I can still see quite a few details about my old vehicle and even potentially operate its GPS, doors, locks, and horn remotely. The car was never electronically disconnected from my ownership like turning in an old cell phone. The question becomes who’s responsibility is it ? Curiously, on the bottom of the email is this line (click to enlarge):
 From this footnote, it appears I am responsible and the new owner has no idea I still have access to the vehicle. I traded this vehicle into a dealer and the car has been resold. It has a lot more mileage on it than when I sold it. The dealer clearly did not contact Dodge and neither did the new owner. In addition, what if this was a private sale, who's responsibility is it to wipe the car’s electronic information clean? This includes everything from saved GPS destinations, programmed garage door openers, and even contacts downloaded via bluetooth to a hands free phone book. Currently, it is up to the end user and not the dealer or buyer. I did erase all the items in the Uconnect head unit when I traded it in but completely missed all the services in the cloud.
As a physical example of this problem, have you seen this article from mid-December? A Texas plumber sold his truck that had branding of his plumbing company on the doors. It was sold to an auctioneer and ended up in the middle east being used by ISIS as gun truck. No one removed the branding and technically no one is responsible for doing so. Electronic information stored in a car is no different nor is it connection electronically to the previous owner. We just do not have the laws and processes in place to handle this information, manage the privacy risks, and ensure that it can not be leveraged (or hacked) by a previous owner, temporary owner, or used car dealer. Unfortunately, I now know my Challenger is not doing so well and I really should not have this information. I feel sorry for the new owner, hope they get it repaired shortly, and unfortunately know where you live.
So a quick word about privacy. It is up to all of us to secure our information. Not only make sure it is protected, but also when we part a device, a technology, or even a service, make sure all information is deleted and wiped. We have been doing this for years with old hard drives and when we turn in old cell phones and tablets. We now have to wipe our cars. Not only manually deleting information from the on board computers that make driving easier, but also any accounts and cloud services that support the vehicles. Ownership of these types of privacy problems and personally identifiable information has not fallen on the automotive industry to solve yet – I can only hope that it does soon. As a consumer customizing a car with my preferences, the last thing I want to worry about leaking my information once I sell it.
Unfortunately BeyondTrust has absolutely no technology that can help with this problem. In fact, I am not aware of any technology that can. As an officer in BeyondTrust however, I feel I must follow the best advice given todays state of affairs, “If you see something, say something”, and I definitely am.
From this footnote, it appears I am responsible and the new owner has no idea I still have access to the vehicle. I traded this vehicle into a dealer and the car has been resold. It has a lot more mileage on it than when I sold it. The dealer clearly did not contact Dodge and neither did the new owner. In addition, what if this was a private sale, who's responsibility is it to wipe the car’s electronic information clean? This includes everything from saved GPS destinations, programmed garage door openers, and even contacts downloaded via bluetooth to a hands free phone book. Currently, it is up to the end user and not the dealer or buyer. I did erase all the items in the Uconnect head unit when I traded it in but completely missed all the services in the cloud.
As a physical example of this problem, have you seen this article from mid-December? A Texas plumber sold his truck that had branding of his plumbing company on the doors. It was sold to an auctioneer and ended up in the middle east being used by ISIS as gun truck. No one removed the branding and technically no one is responsible for doing so. Electronic information stored in a car is no different nor is it connection electronically to the previous owner. We just do not have the laws and processes in place to handle this information, manage the privacy risks, and ensure that it can not be leveraged (or hacked) by a previous owner, temporary owner, or used car dealer. Unfortunately, I now know my Challenger is not doing so well and I really should not have this information. I feel sorry for the new owner, hope they get it repaired shortly, and unfortunately know where you live.
So a quick word about privacy. It is up to all of us to secure our information. Not only make sure it is protected, but also when we part a device, a technology, or even a service, make sure all information is deleted and wiped. We have been doing this for years with old hard drives and when we turn in old cell phones and tablets. We now have to wipe our cars. Not only manually deleting information from the on board computers that make driving easier, but also any accounts and cloud services that support the vehicles. Ownership of these types of privacy problems and personally identifiable information has not fallen on the automotive industry to solve yet – I can only hope that it does soon. As a consumer customizing a car with my preferences, the last thing I want to worry about leaking my information once I sell it.
Unfortunately BeyondTrust has absolutely no technology that can help with this problem. In fact, I am not aware of any technology that can. As an officer in BeyondTrust however, I feel I must follow the best advice given todays state of affairs, “If you see something, say something”, and I definitely am.

Morey J. Haber, Chief Security Advisor
Morey J. Haber is the Chief Security Advisor at BeyondTrust. As the Chief Security Advisor, Morey is the lead identity and technical evangelist at BeyondTrust. He has more than 25 years of IT industry experience and has authored four books: Privileged Attack Vectors, Asset Attack Vectors, Identity Attack Vectors, and Cloud Attack Vectors. Morey has previously served as BeyondTrust’s Chief Security Officer, Chief Technology, and Vice President of Product Management during his nearly 12-year tenure. In 2020, Morey was elected to the Identity Defined Security Alliance (IDSA) Executive Advisory Board, assisting the corporate community with identity security best practices. He originally joined BeyondTrust in 2012 as a part of the acquisition of eEye Digital Security, where he served as a Product Owner and Solutions Engineer, since 2004. Prior to eEye, he was Beta Development Manager for Computer Associates, Inc. He began his career as Reliability and Maintainability Engineer for a government contractor building flight and training simulators. Morey earned a Bachelor of Science degree in Electrical Engineering from the State University of New York at Stony Brook.








