Use Shell Jump to Access a Remote Network Device
With Shell Jump, quickly connect to an SSH-enabled or Telnet-enabled network device to use the command line feature on that remote system. For example, run a standardized script across multiple systems to install a needed patch or troubleshoot a network issue. Administrators can enable command filtering to help prevent users from inadvertently using harmful commands on SSH-connected endpoints.
You can use your own SSH tool for the SSH protocol. For more information, please see Change settings and preferences in the Access Console.
In order to use your own tool, you must enable Protocol Tunnel Jump in /login > Users & Security > Users > Access Permissions > Jump Technology > Protocol Tunnel Jump. This may need to be enabled by a group policy.
Create a Shell Jump Shortcut
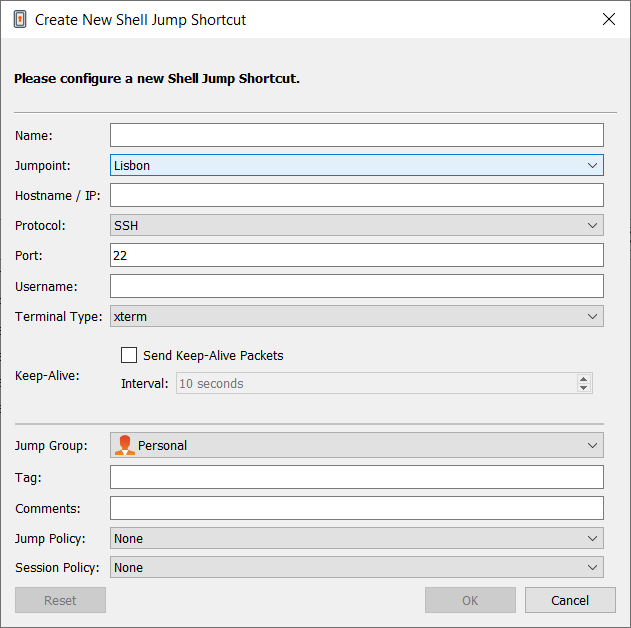
To create a Shell Jump shortcut, click the Create button in the Jump interface. From the dropdown, select Shell Jump. Shell Jump shortcuts appear in the Jump interface, as well as Jump Clients and other types of Jump Item shortcuts.
Shell Jump shortcuts are enabled only if their Jumpoint is configured for open or limited Shell Jump access.
Enter a Name for the Jump Item. This name identifies the item in the session tabs. This string has a maximum of 128 characters.
From the Jumpoint dropdown, select the network that hosts the computer you wish to access. The access console remembers your Jumpoint choice the next time you create this type of Jump Item.
Enter the Hostname / IP of the system you wish to access.
Choose the Protocol to use, either SSH or Telnet.
Port automatically switches to the default port for the selected protocol but can be modified to fit your network settings.
Enter the Username to sign in as.
Select the Terminal Type, either xterm or VT100.
You can also select to Send Keep-Alive Packets to keep idle sessions from ending. Enter the number of seconds to wait between each packet send.
Move Jump Items from one Jump Group to another using the Jump Group dropdown. The ability to move Jump Items to or from different Jump Groups depends upon your account permissions.
Further organize Jump Items by entering the name of a new or existing Tag. Even though the selected Jump Items are grouped together under the tag, they are still listed under the Jump Group in which each Jump Item is pinned. To move a Jump Item back into its top-level Jump Group, leave this field blank.
Jump Items include a Comments field for a name or description, which makes sorting, searching, and identifying Jump Items faster and easier.
To set when users are allowed to access this Jump Item, if a notification of access should be sent, or if permission or a ticket ID from your external ticketing system is required to use this Jump Item, choose a Jump Policy. These policies are configured by your administrator in the /login interface.
Choose a Session Policy to assign to this Jump Item. The session policy assigned to this Jump Item has the highest priority when setting session permissions. The ability to set a session policy depends on your account permissions.
Use a Shell Jump Shortcut
To use a Shell Jump shortcut to start a session, select the shortcut from the Jump interface and click the Jump button.
If attempting to Shell Jump to an SSH device without a cached host key, you receive an alert that the server's host key is not cached and that there is no guarantee that the server is the computer you think it is.
If you choose Save Key and Connect, then the key is cached on the Jumpoint's host system so that future attempts to Shell Jump to this system do not result in this prompt. Connect Only starts the session without caching the key, and Abort ends the Shell Jump session.
When you Shell Jump to a remote device, a command shell session immediately starts with that device. If you Shell Jump to a provisioned SSH device with an unencrypted key or with an encrypted key whose password has been cached, you are not prompted for a password. Otherwise, you are required to enter a password. You can then send commands to the remote system.
If you Shell Jump to an SSH device with keyboard interactive MFA enabled, there is a secondary prompt for input.
Administrators can configure command filtering on Shell Jump items to block some commands and allow others in an effort to prevent the user from inadvertently using a command that may cause undesireable results. In the event a user attempts to use a command that matches an expression that is not allowed, they receive a prompt and are not allowed to execute the command.
BeyondTrust's command filter uses extended regular expressions, which are not to be confused with egrep. For more information, please see Regular expressions (C++).
Configure Shell Prompt Filtering:
- Log into the /login interface as a user with permissions to configure Jump Items and session policies.
- Browse to Jump > Jump Items and scroll down to the Shell Jump Filtering section.
- In the Recognized Shell Prompts text box, enter regexes to match the command shell prompts found on your endpoint systems, one per line.
Line breaks, or newlines, are not allowed within the command prompt patterns entered. If an endpoint system uses a multi-line prompt, enter an expression that matches only the final line of the prompt in the text box.
- Click Save.
Once you have entered the regexes you wish to use, you can test a shell prompt to determine if it matches any of the regexes in the list. This allows you to test your regexes without starting a session. Enter the expression in the Shell Prompt text box and click the Check button. A notice displays whether or not the shell prompt you entered matches one of the regexes in the list.
Configure Command Filtering:
- Browse to Users & Security > Session Policies and either create a new policy or edit an existing one.
You can also configure this for users and/or group policies.
- Locate the Command Shell settings in the Permissions section.
- Because you will use command filtering with Shell Jump items, select the Allow radio button to allow the use of the command shell.
- Choose from Allow all commands, Allow the command patterns below, or Deny the command patterns below and specify in the text box which regex patterns you wish to allow or block.
Once you have entered the command patterns you wish to allow or block, you can test commands in the Command Tester text box. A notice displays whether or not the command entered would be allowed to run on the remote system based on the regexes specified in the list.
The two possible messages are:
- "The entered command shall be allowed based on your selections."
- "The entered command shall not be allowed based on your selections."
Use Credential Injection with SUDO on a Linux Endpoint
To use credential injection with SUDO, an administrator must configure one or more functional accounts on each Linux endpoint to be accessed via Shell Jump. As the process for configuring the sudoers file is complex and varies by platform, please refer to your platform's documentation for details on completing this process. Each functional account must:
- Allow authenticating via SSH (password or SSH key).
- Have the account credentials stored in the Endpoint Credential Manager (ECM).
- Have one or more entries in /etc/sudoers granting the functional account access to one or more commands to be executed as root without requiring a password (NOPASSWD).
An administrator must create a Shell Jump Item for the endpoint.
Next, an administrator must configure the ECM and/or password vault to grant users access to the appropriate functional accounts for that Jump Item.
When a user Jumps to the Shell Jump Item, they can choose from the list of functional accounts available for that endpoint. Each functional account has its own set of commands that can be executed using SUDO, as configured by the administrator on the endpoint. The credentials for the account are passed from the ECM to the endpoint.
Jump Items can be set to allow multiple users to simultaneously access the same Jump Item. If set to Join Existing Session, other users are able to join a session already underway. The original owner of the session receives a note indicating another user has joined the session, but is not allowed to deny them access. For more information on simultaneous Jumps, please see Jump Item Settings.