Copy the SSL Certificate to Failover and Atlas B Series Appliances
BeyondTrust allows you to use additional B Series Appliances for failover or for load balancing. If you intend to use additional B Series Appliances in your setup, it is important that each additional B Series Appliance is properly secured by an SSL certificate.
In a failover setup, the primary and backup B Series Appliances must have identical SSL certificates for the backup B Series Appliance to connect to the main BeyondTrust site hostname. The CA-signed certificate should support each B Series Appliance's unique hostname as well as the main BeyondTrust site hostname. This certificate can then be replicated on both the primary and the backup B Series Appliances.
If using an Atlas setup, it is recommended that you use a wildcard certificate that covers both your BeyondTrust site name and each traffic node hostname. If you do not use a wildcard certificate, then adding traffic nodes that use different certificates may require a rebuild of the BeyondTrust software. Therefore, you should create a CA-signed wildcard certificate that supports all of the hostnames used in your Atlas setup. Replicate this certificate on each of your Atlas clustered B Series Appliances.
Export the Certificate
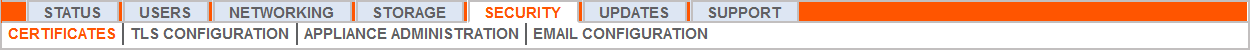
- On the primary B Series Appliance, log into the /appliance interface. Go to Security > Certificates.
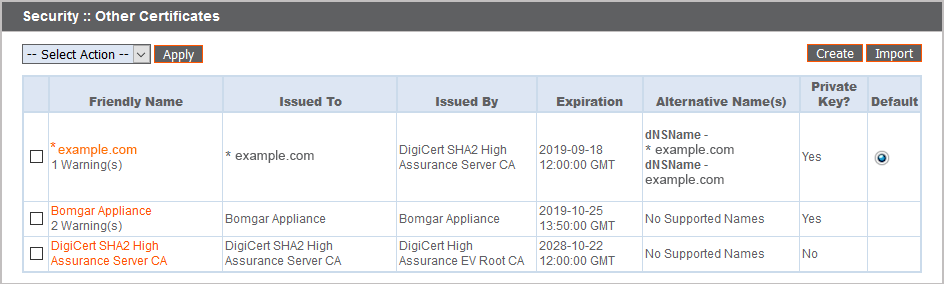
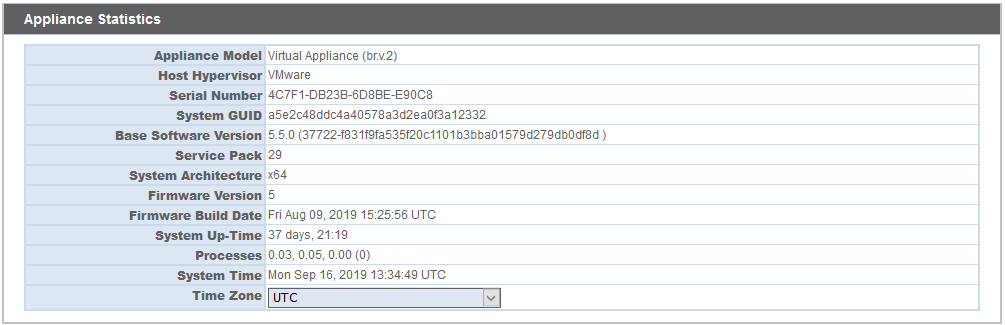
- In the Security :: Other Certificates section, check the box beside the certificate that is assigned to the active IP address. Then, from the dropdown menu at the top of this section, select Export.
Exporting certificates does not remove them from the B Series Appliance.
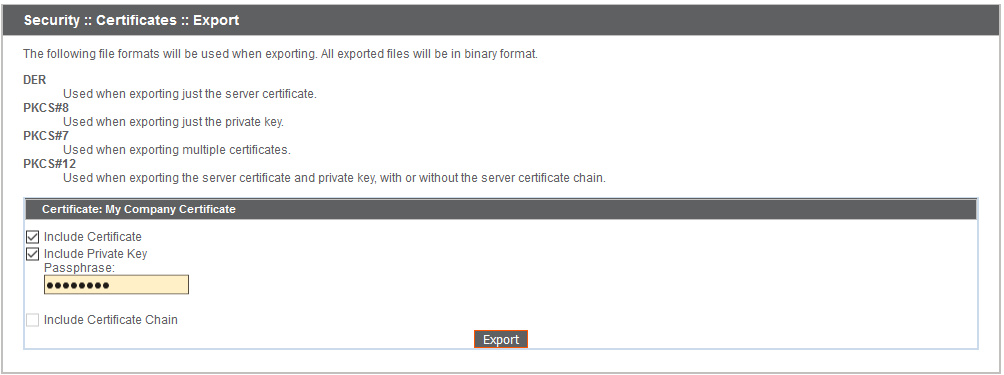
- On the Security :: Certificates :: Export page, check the options to include the certificate, the private key, and the certificate chain. It is strongly recommended that you set a passphrase for the private key.
Import the Certificate
- On the backup B Series Appliance, log into the /appliance interface. Go to Security > Certificates.
- In the Security :: Other Certificates section, click the Import button.
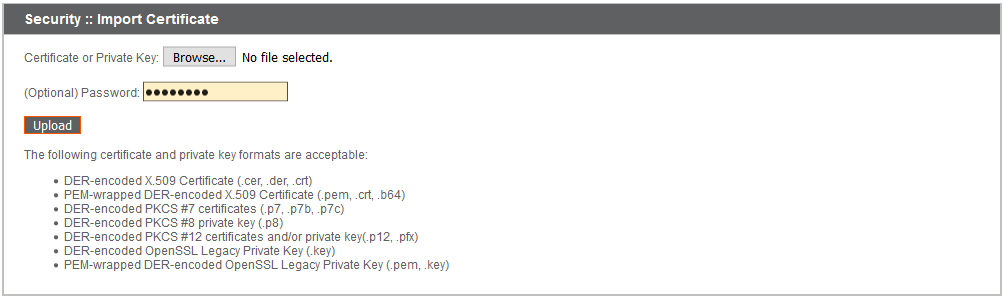
- Browse to the certificate file you just exported from the primary B Series Appliance. If a passphrase was assigned to the file, enter it in the Password field. Then click Upload.
- The imported certificate chain should now appear in the Security :: Other Certificates section.
- Repeat the import process for each additional clustered B Series Appliance.
Update the BeyondTrust Appliance B Series
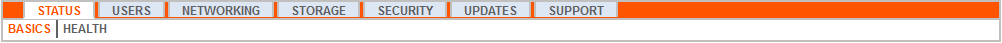
BeyondTrust software automatically trusts certificates issued by certificate authorities in your operating system's native CA trust store. If you obtain a self-signed certificate, or a certificate issued by an authority not trusted on all platforms, BeyondTrust Technical Support must build a copy of your certificate into your software. To update your appliance, send BeyondTrust Technical Support a copy of the new SSL certificate, as well as a screenshot of your Status > Basics page to identify the B Series Appliance being updated.
Do NOT send your private key file (which ends in .p12) to BeyondTrust Technical Support. This key is private because it allows the owner to authenticate your B Series Appliance's identity. Ensure that the private key and its passphrase are kept in a secure, well-documented location on your private network. If this key is ever exposed to the public (via email, for instance), the security of your B Series Appliance is compromised.
- Go to /appliance > Status > Basics and take a screenshot of the page.
- Add the saved screenshot and the all of the SSL certificates files for your certificate chain to a .zip archive. Do NOT include any private key files (e.g., .p12, .pfx, or .key files).
- Compose an email to BeyondTrust Technical Support requesting a software update. Attach the .zip archive containing the certificate files and screenshot. If you have an open incident with Support, include your incident number in the email. Send the email.
- Once BeyondTrust Technical Support has built your new software package, they will email you instructions for how to install it. Update your software following the emailed instructions.
- Repeat the update process for each additional clustered B Series Appliance.
After these steps are complete, it is advisable to wait 24-48 hours before proceeding further. This allows time for your BeyondTrust client software (especially Jump Clients) to update themselves with the new certificate which BeyondTrust Technical Support included in your recent software update.
SSL Certificate Auto-Selection
BeyondTrust uses Server Name Indication (SNI), an extension to the TLS networking protocol, to allow any SSL certificate stored on the B Series Appliance to be served to any client. Because most TLS clients send SNI information at the start of the handshaking process, this enables the B Series Appliance to determine which SSL certificate to send back to a client that requests a connection.
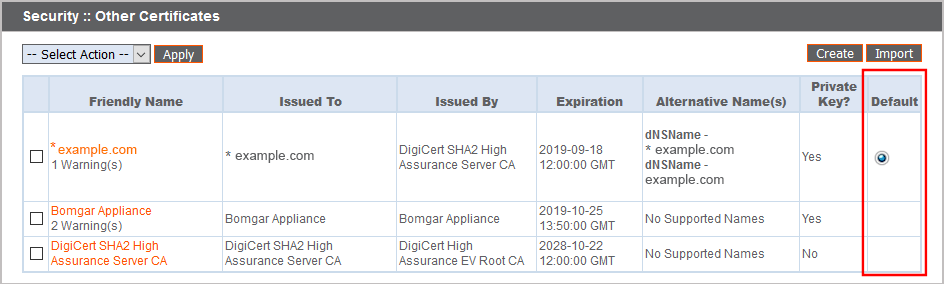
You may choose a default certificate to serve to clients who do not send SNI information with their request, or to clients who do send SNI information, but which does not match anything in the B Series Appliance database.
- Go to /appliance > Security > Certificates.
- In the Default column, select the radio button for the certificate you wish to make default.