Create and Configure the Kerberos Security Provider
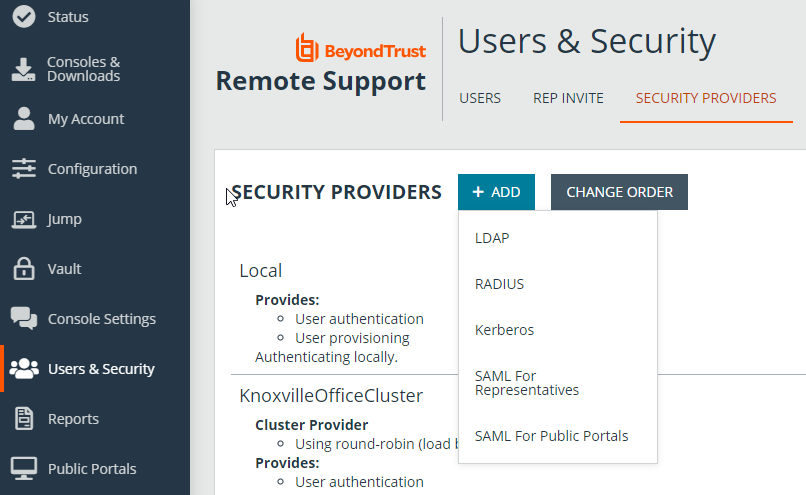
Go to /login > Users & Security > Security Providers.
Click Add. From the dropdown, select the type of server you want to configure.
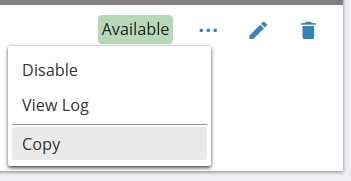
Alternatively, you can copy an existing provider configuration by clicking the ellipse on a listed provider and then selecting Copy.
Enter the settings for this security provider configuration as detailed below.
Name
Create a unique name to help identify this provider.
Enabled
If checked, your BeyondTrust Appliance B Series can search this security provider when a user attempts to log in to the representative console or /login. If unchecked, this provider will not be searched.
Keep display name synchronized with remote system
These values determine which fields should be used as the user's private and public display names.
Strip realm from principal names
Select this option to remove the REALM portion from the User Principal Name when constructing the BeyondTrust username.
Authorization Settings
User Handling Mode
Select which users can authenticate to your BeyondTrust Appliance B Series. Allow all users allows anyone who currently authenticates via your Key Distribution Center (KDC). Allow only user principals specified in the list allows only user principles explicitly designated. Allow only user principals that match the regex allows only users principals who match a Perl-compatible regular expression (PCRE).
Default Group Policy
Each user who authenticates against an external server must be a member of at least one group policy in order to authenticate to your B Series Appliance, logging into either the /login interface or the representative console. You can select a default group policy to apply to all users allowed to authenticate against the configured server.
SPN Handling Mode
Allow only SPNs specified in the list
If unchecked, all configured service principal names (SPNs) for this security provider are allowed. If checked, select specific SPNs from a list of currently configured SPNs.
LDAP Group Lookup
If you want users on this security provider to be associated with their groups on a separate LDAP server, choose one or more LDAP group servers to use for group lookup.
If a default policy is defined, then any allowed user who authenticates against this server will potentially have access at the level of this default policy. Therefore, it is recommended that you set the default to a policy with minimum privileges to prevent users from gaining permissions that you do not wish them to have.
If a user is in a default group policy and is then specifically added to another group policy, the settings for the specific policy will always take precedence over the settings for the default, even if the specific policy is a lower priority than the default, and even if the default policy's settings are set to disallow override.
Save Changes
Click Save to save this security provider configuration.