Security in BeyondTrust Remote Support (On-Premises)
The purpose of this document is to help technically-oriented professionals understand the security-related value BeyondTrust Remote Support can bring to your organization. Remote Support can help your support organization stay secure and compliant, while improving the efficiency and success of your organization with a better end-user support experience.
BeyondTrust Remote Support Overview
BeyondTrust connects and protects people and technology with leading secure access solutions that strengthen security while increasing productivity. The BeyondTrust Appliance B Series gives support technicians secure remote control of computers, over the internet or on local networks. This specialized B Series Appliance provides exceptional performance, reliability, ease-of-use, and scalability through a solution that is optimized for remote support. With BeyondTrust Remote-Support, a support technician can see the supported screen and control the supported system remotely, as if physically present.
Using multiple features designed to ensure the security of remote support sessions, Remote-Support integrates with external user directories, such as LDAP, for secure user management; prevents sensitive data from being routed outside the organization; and supports extensive auditing and recording of support sessions. Logging is performed by the B Series Appliance, which allows for the review of all customer and support representative interactions, including video playback of all desktop screen interactions. Remote-Support also integrates with leading systems management and identity management solutions and includes an API for deeper integration. With Remote-Support, support managers can create support teams, customize queues, and report on all support activity.
Remote-Support enables remote access to multiple operating systems, including Windows, Mac, various Linux distributions, and mobile operating systems. Remote-Support also enables remote control of various kinds of systems, including laptops, desktops, servers, kiosks, point-of-sale systems, smartphones, and network devices.
Architecture of Remote Support (On-Premises)
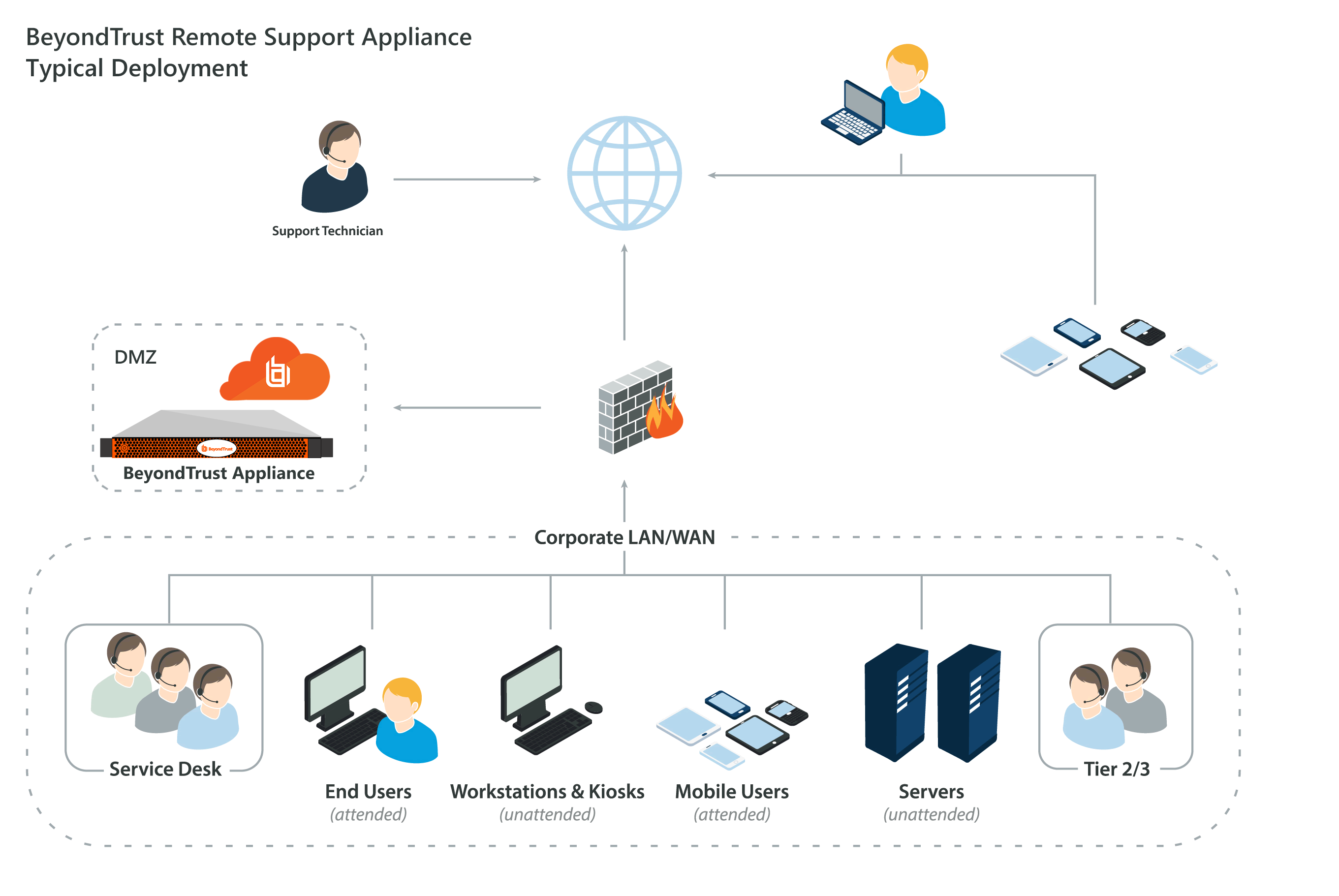
To make secure remote support possible, the BeyondTrust Remote-Support architecture places the BeyondTrust Appliance B Series as the focal point of all communications. The B Series Appliance provides a platform to build a support portal, a site through which an organization funnels all remote support requests. The support portal offers a web site interface using Hypertext Transfer Protocol (HTTP) for unauthenticated services, Secure HTTP (HTTPS) for authenticated services, and direct client connections accepted over a proprietary, BeyondTrust-defined protocol.
The B Series Appliance is comprised of two main components. The first, called Base, is made up of the firmware that provides system-level configuration of a B Series Appliance. Settings such as IP addresses and security certificate configurations are all configured via the Base firmware, which is accessed via the /appliance web interface.
The software used for site-level configuration, accessed via the /login web interface, makes up the second functional component. The user configuration and session options take place behind the /login page, and you can download the representative console, endpoint client, Jump Clients, Jumpoints, and security provider connection agents from there. Sessions always occur through the B Series Appliance, and since the connections are outbound from the clients to the B Series Appliance using well known ports, the application can communicate without local firewall changes.
Validation
To ensure the security and value of our product, BeyondTrust incorporates vulnerability scanning in our software testing process. We track the results of vulnerability scans performed prior to a software release and prioritize resolution based on severity and criticality of any issues uncovered. Should a critical or high-risk vulnerability surface after a software release, a subsequent maintenance release addresses the vulnerability. Updated maintenance versions are distributed to our customers via the update manager interface within the Remote Support administrative interface. When necessary, BeyondTrust Support contacts customers directly, describing special procedures to follow to obtain an updated maintenance version.
In addition to internal scanning procedures, BeyondTrust contracts with third-parties for a source code level review as well as penetration testing. The source code review conducted essentially provides validation from a third party that coding best practices are followed and that proper controls are in place to protect against known vulnerabilities. A penetration test is conducted to confirm the findings.