Create and configure the SAML security provider
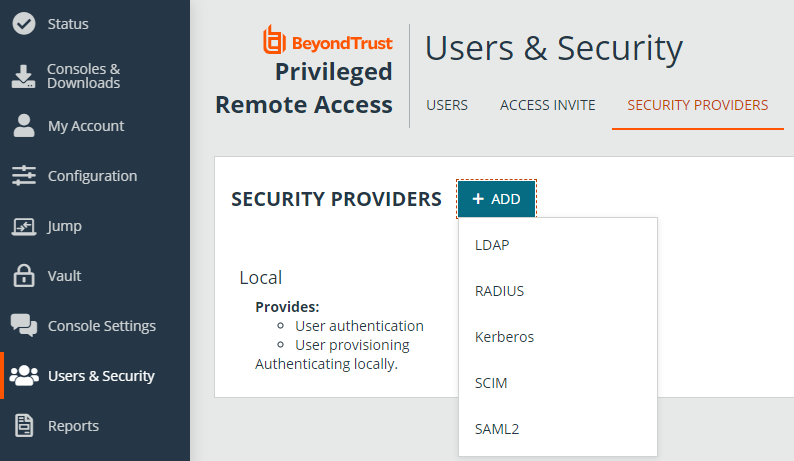
Go to /login > Users & Security > Security Providers.
From the + ADD dropdown, select the type of server you want to configure.
Multiple SAML providers can be configured, but a user who is defined in more than one provider can only be mapped to the first provider.
Add security provider
Name
Enter a unique name to identify the provider.
Enabled
If checked, your B Series Appliance searches this security provider when a user attempts to log in. If unchecked, this provider is not searched.
User Provision
By default, user provisioning occurs on this provider. If you have a SCIM provider set up, you can choose to provision users through that provider instead.
This setting cannot be modified after this security provider is first saved.
Associated Email Domains
This setting only applies if you have more than one active SAML provider and is ignored otherwise.
Add any email domains that should be associated with this SAML provider, one per line. When authenticating, users are asked to enter their email. The domain of their email is matched against this list, and they are redirected to the appropriate identity provider for authentication.
If multiple SAML providers are configured and the user's email does not match any of the associated domain on any provider, then they are not allowed to authenticate.
Identity provider settings
Identity Provider Metadata
The metadata file contains all the information needed for the initial setup of your SAML provider and must be downloaded from your identity provider. Save the XML file, and then click Choose File to select and upload the selected file.
The fields for Entity ID, Single Sign-On Service URL, and Certificate are automatically populated from the identity provider's metadata file. If you cannot get a metadata file from your provider, this information can be entered manually.
Entity ID
This is the unique identifier for the identity provider you are using.
Single Sign-On Service URL
This is the URL where you are automatically redirected to log in to BeyondTrust Privileged Remote Access using SAML.
SSO URL Protocol Binding
This determines whether an HTTP POST occurs or whether the user is redirected to the sign-on URL. Choose HTTP redirect if not specified by the provider.
If request signing is enabled (under Service Provider settings), protocol binding is limited to redirect only.
Server Certificate
This certificate is used to verify the signature of the assertion sent from the identity provider. Click +UPLOAD to open a file browse window, navigate to the certificate, and click Open.
Service provider settings
Service Provider Metadata
Download the BeyondTrust metadata, which you then need to upload to your identity provider.
Entity ID
This is your BeyondTrust URL. It uniquely identifies your site to the identity provider.
Private Key
If necessary, you can decrypt messages sent by the identity provider, if they support and require encryption. Click CHOOSE FILE to upload the private key necessary to decrypt the messages sent from the identity provider.
Signed AuthnRequest
Check to enable request signing. If enabled, SSO URL protocol binding is limited to redirect only. The SSO URL protocol binding field is updated automatically, if necessary.
A private key and signing certificate is required for request signing.
User attribute settings (Visible Only if This Provider is Used for User Provisioning)
User SAML Attributes
These attributes are used to provision users within BeyondTrust. The default values match BeyondTrust-certified applications with various identity providers. If you are creating your own SAML connector, you may need to modify the attributes to match what is being sent by your identity provider.
Authorization settings (Visible Only if This Provider is Used for User Provisioning)
Lookup Groups Using This Provider
Enabling this feature allows faster provisioning by automatically looking up groups for this user, using Group Lookup Attribute Name and Delimiter. We recommend enabling this feature. If not used, SAML users must be manually assigned to group policies after their first successful authentication.
Group Lookup Attribute Name
Enter the name of the SAML attribute that contains the names of groups to which users should belong. If the attribute value contains multiple group names, then specify the Delimiter used to separate their names.
If left blank, SAML users must be manually assigned to group policies after their first successful authentication.
Group Lookup Delimiter
If the Delimiter is left blank, then the attribute value may contain multiple XML nodes with each one containing a different name.
Available Groups
This is an optional list of SAML groups always available to be manually assigned to group policies. If left blank, a given SAML group is made available only after the first successful authentication of a user member of such group. Please enter one group name per line.
Default Group Policy
Each user who authenticates against an external server must be a member of at least one group policy in order to authenticate to your B Series Appliance, logging into either the /login interface or the access console. You can select a default group policy to apply to all users allowed to authenticate against the configured server.
If a default policy is defined, any allowed user who authenticates against this server might have access at the level of this default policy. Therefore, we recommend you set the default to a policy with minimum privileges to prevent users from gaining permissions you do not wish them to have.
If a user is in a default group policy and is then specifically added to another group policy, the settings for the specific policy always take precedence over the settings for the default, even if the specific policy is a lower priority than the default, and even if the default policy's settings are set to disallow override.
Test settings
You can test the SAML configuration from this page. The provider must be saved before it can be tested. Click Save at upper left area of the screen, then scroll down and click Test. The configuration is tested against the identity provider, and a test results page shows the SAML response and a formatted version of the assertion XML. The responses can be copied to other tools if further review is required.