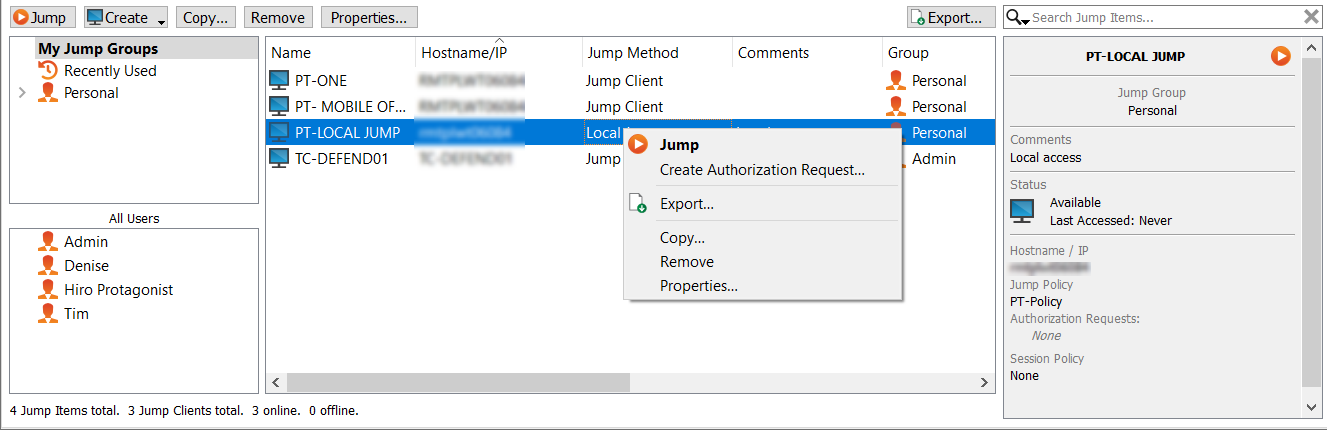
Jump interface: use Jump items to access remote systems
The Jump interface appears in the bottom half of the access console, listing the Jump Items available to you. The list may contain Jump Clients, as well as Jump shortcuts for Remote Jumps, Local Jumps, RDP sessions, VNC sessions, Protocol Tunnel Jumps, Shell Jumps, and Web Jumps. Jump Item availability, including whether or not the Jump Item is in use, is listed in the Status column.
Jump Items are listed in Jump Groups. If you are assigned to one or more Jump Groups, you can access the Jump Items in those groups, with the permissions assigned by your admin. Selecting a Jump Group and then clicking Create auto-selects that Jump Group in the Jump Item configuration window.
Your personal list of Jump Items is primarily for your individual use, although your team leads, team managers, and users with permission to see all Jump Items may have access to your personal list of Jump Items. Similarly, if you are a team manager or lead with appropriate permissions, you may see team members' personal lists of Jump Items. Additionally, you may have permission to access Jump Items in Jump Groups you do not belong to and personal Jump Items for non-team members.
Copy Jump items
Jump Items can be copied and can belong to multiple Jump Groups. This includes Jump Client items, providing administrators with the ability to set separate policies and group permissions without requiring an additional Jump Client installation on the target endpoint. Users with the appropriate permissions see the option to Copy Jump Items in the Access Console by right-clicking the item. Users can perform this function on multiple Jump Items as well.
This feature enables admins and users to effectively manage different policies for Jump Items and Jump Clients without the need to create a new Jump Item. This functionality enables users to limit the number of clients necessary to enable Jump Client sessions, and limits manual administrative tasks when defining access pathways for users.
Jump to a Jump item
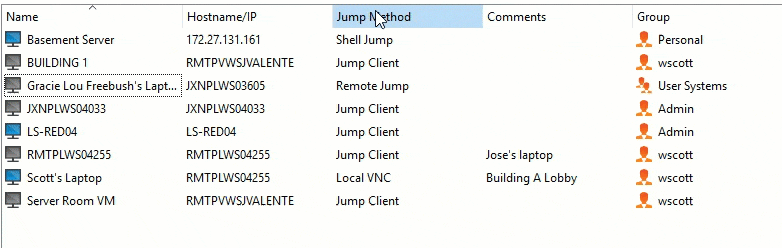
Browse through groups for the computer you wish to access. To facilitate browsing the Jump Items list, you may drag the columns into any order you wish, and then sort a column by clicking the column header. The access console remembers the column order and the sort order the next time the access console is launched.
In addition to browsing for Jump Items, you can search based on multiple fields. Enter a string in the search field and then press Enter. To change the fields you are searching, click on the magnifying glass and check or uncheck any of the available fields. Searchable fields include Comments, Console User, Domain, FQDN, Group, Hostname/IP, Jump Method, Last Accessed, Name, Private IP, Public IP, Status, Tag, and Workgroup.
Once you have found the computer you wish to access, double-click the entry, or select the entry and click the Jump button. This attempts to start a session with the remote computer.
You may programmatically connect to a Jump Item directly from your systems management or ticketing tool. If your search results in only one Jump Item, the session starts immediately. If multiple Jump Items are returned, select one of the Jump Items listed in the selection window and click OK.
For details about scripting, see Access Console Scripting and Client Scripting API at www.beyondtrust.com/docs/privileged-remote-access/how-to/integrations/api/client-script.
Default Credentials for Jump Items
When starting a Jump session that requires credentials, after selecting the credentials, you can check Remember as my default. Once a credential is selected as a default, it displays with other Jump item details, and subsequent sessions start without requesting credentials.
When a default credential is set, the Jump item details (accessed by right-clicking the Jump Item) include a button for Jump (Change Credentials). This opens the credential selection window, and you can either change default credential, select a different credential for this session, or clear the saved default credential.
If a default credential is no longer available to the user for that Jump item, the next time they start a session with that Jump item there is a warning that the requested credentials for starting the session were not found, and the option to continue. If you continue, the credential selection window opens and you can select a credential as usual.
Start multiple Jump sessions
You can select up to ten Jump items and start them with a single click. The jump items must either have saved default credentials, or not require credentials. Any Jump items that require credentials and do not have default credentials do not start.
Schedule
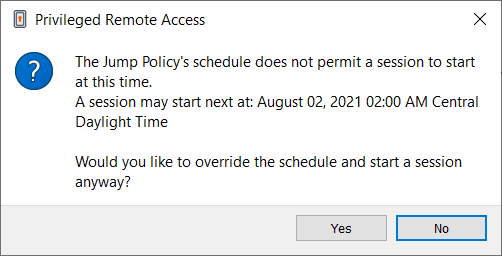
If a Jump Policy is applied to the Jump Item, that policy affects how and/or when a Jump Item may be accessed.
If a Jump Policy enforces a schedule for this Jump Item, an attempt to access the Jump Item outside of its permitted schedule prevents the Jump from occurring. A prompt informs you of the policy restrictions and provides the date and time when this Jump Item is next available for access.
Notification
If a Jump Policy is configured to send a notification on session start or end, then an attempt to access a Jump Item alerts you that an email will be sent. You can choose to proceed with the Jump and send a notification, or you can cancel the Jump.
Ticket ID
If a Jump Policy requires entry of a ticket ID from your external ITSM or ticket ID system before the Jump can be performed, a dialog opens. In the dialog, enter the ticket ID you need, authorizing access to this Jump Item.
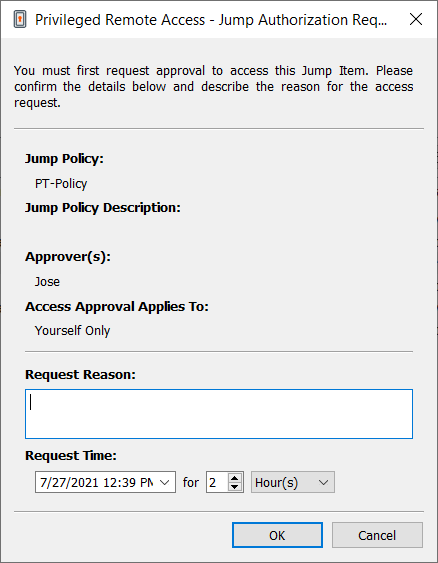
Authorization
If a Jump Policy requires authorization before the Jump can be performed, a dialog opens. In the dialog, enter the reason you need to access this Jump Item. Then enter the date and time at which you wish authorization to begin, as well as how long you require access to the Jump Item. Both the request reason and the request time are visible to the approver and help them decide whether to approve or deny access.
When you click OK, an email is sent to the addresses defined as approvers for this policy. This email contains a URL where an approver can see the request, add comments, and either approve or deny the request.
If a request was approved by one person, a second can access the URL to override approval and deny the request. If a request was denied, then any other approvers accessing the site can see the details but cannot override the denied status. If a user has already joined an approved session, that access cannot be denied. Although other approvers can see the email address of the person who approved or denied the request, the requestor cannot.Based on the Jump Policy settings, an approved request grants access either to any user who can see and request access to that Jump Client or only to the user who requested access.
In the Jump interface, the Jump Item's details pane displays the status of any authorization requests as either pending, approved, approved only for a different user, or denied. When an approver responds to a request, a pop-up notification appears on the requestor's screen alerting them that access has been either approved or denied. If the requestor has a configured email address, an email notification is also sent to the requestor.
When a user Jumps to a Jump Item which has been approved for access, a notification alerts the user to any comments left by the approver.
When approval has been granted to a Jump Item, that Jump Item becomes available either to any user who can see and request access to that Jump Item or only to the user who requested access. This is determined by the Jump Policy.
Multiple requests may be sent for different times. The requested access times can overlap if the Jump approval request is for the Requestor Only. Access time cannot overlap if the approval is for Anyone Permitted to Request. If a request is denied, then a second request may be sent for the same time.
Revoke an Access Approval Request
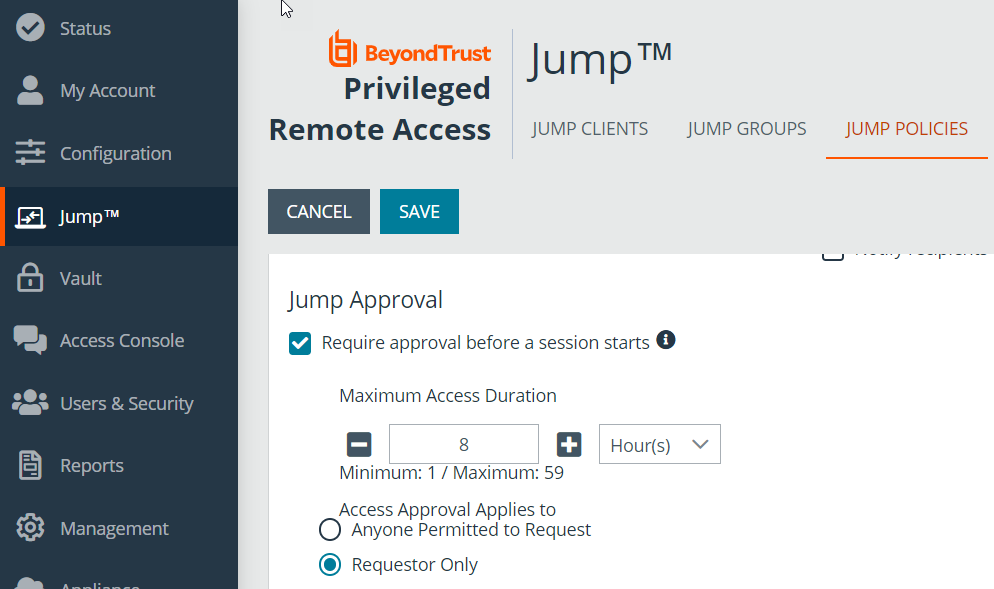
Permission to revoke approved access requests is controlled by Jump Policy. Any user who can approve requests on the Jump Policy can cancel requests, subject to the approval type. In the /login web management interface, go to Jump > Jump Policies. Under Jump Approval you have two options:
- Anyone Permitted to Request
- Requestor Only
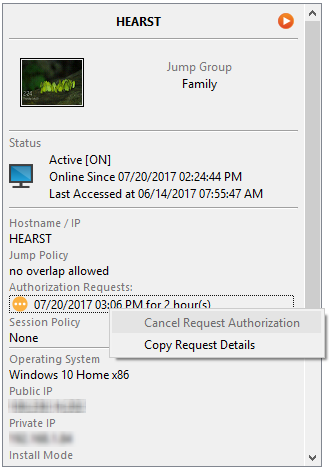
If the Jump Policy is set to requestor Only, and an Access Request is presently approved for User A, User B is asked to create a new Access Request if they attempt to Jump to the Jump Item, since that request does not apply to them. Additionally, if User B attempts to cancel the Access Approval Request, the option is grayed out. The only user who can cancel the approved request is User A, because they are the approved user for the request.
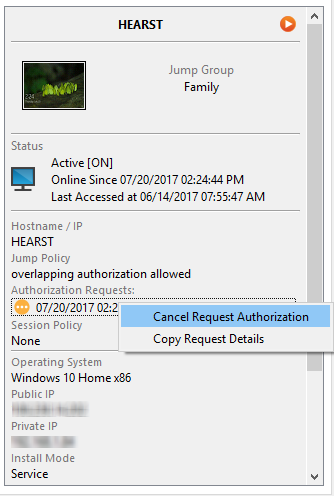
However, if the Jump Policy is set to Anyone Permitted to Request, and an Access Request is presently approved for User A, User B is allowed to start a new session with the Jump Item if they attempt to Jump to it. In addition, anyone with permission to access the Jump Item is allowed to cancel / revoke the request.