Policy Administration
You can import prebuilt Endpoint Privilege Management for Windows policies.
For more information on template policies, see Import Template.
Advanced Agent Settings
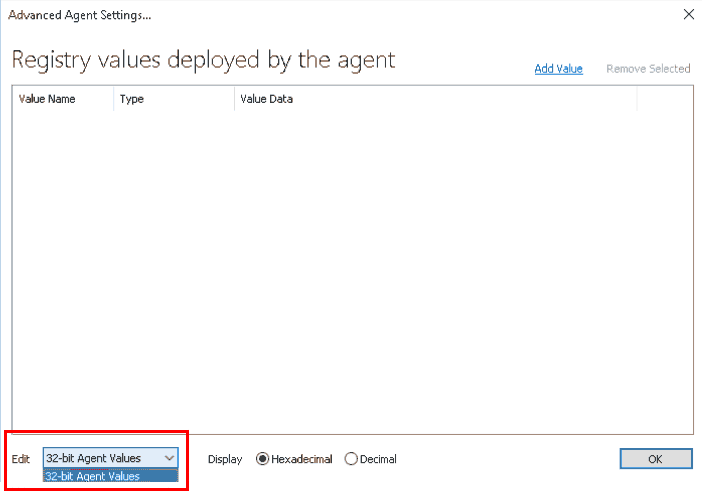
The Advanced Agent Settings section allows you to configure and deploy additional registry based settings to Endpoint Privilege Management for Windows.
- Right-click the top level Endpoint Privilege Management Settings node and click Advanced Agent Settings.
- Select either 32-bit Agent Values if you want to configure a 32-bit registry setting, or 64-bit Agent Values for a 64-bit registry setting.
- Click Add Value. A new line is added to the advanced agent settings list.
- Double-click the Value Name for the new setting, and enter the value name.
- Choose the correct Type, either DWORD, String, or Multi-String.
- Double-click the Value Data for the new setting, and enter the value data. For DWORD values, you can toggle the display type between Hexadecimal and Decimal.
- Click OK to save your changes.
Each advanced agent setting adheres to Group Policy precedence rules. If advanced agent settings are configured in multiple Group Policies, then the Group Policy with the highest precedence is applied (except for multi-string settings, which is merged and consolidated by Endpoint Privilege Management for Windows).
Advanced Agent Settings should only be used when instructed to do so by BeyondTrust Technical Support.
Windows Policy Configuration Precedence
Endpoint Privilege Management for Windows supports a variety of deployment methods, and accepts multiple simultaneous configurations from any combination of the following:
- McAfee ePO Policy: A configuration that is stored in McAfee ePO, configured using the Endpoint Privilege Management ePO Extension in the ePO Policy Catalog.
- Webservice Policy: A configuration that is served from an EPM webservice using HTTPS.
- Webserver Policy: A configuration located on a web server, accessible using HTTP, HTTPS, or FTP.
- Group Policy: Configurations that are stored in Group Policy Objects, configured using Active Directory Group Policy (GPMC) and GPEdit (Local Group Policy). Group Policy based configurations are evaluated according to GPO precedence rules.
- Local Policy: A standalone configuration, which is stored locally and is configured using the Endpoint Privilege Management Policy Editor snap-in for the Microsoft Management Console.
- BeyondInsight: A web-based console where you configure and launch vulnerability assessment scans. As a scan completes, a report is automatically generated. Results can be navigated interactively in the console.
Endpoint Privilege Management for Windows uses the following default precedence to evaluate each configuration for matching rules:
ePO > Webservice > BeyondInsight > Webserver > GPO > Local
Configuration precedence settings can be configured either as part of the client installation, or using the Windows Registry once the client is installed.
To modify the configuration precedence at client installation, use one of the following command lines to install Endpoint Privilege Management for Windows with a specific configuration precedence:
msiexec /i PrivilegeManagementForWindows_xx (XX).msi POLICYPRECEDENCE="EPO,WEBSERVICE,WEBSERVER,GPO,LOCAL"
PrivilegeManagementForWindows_x(XX).exe /s /v" POLICYPRECEDENCE=\"EPO,WEBSERVICE,WEBSERVER,GPO,LOCAL\""
In the command line argument above, (XX) represents 86 or 64 in relation to the 32-bit or 64-bit installation respectively.
To modify your configuration precedence using the Windows Registry, run regedit.exe with elevated privileges and an anti-tamper token disabled.
If agent protection is configured, you must first disable agent protection on the machine before you can change settings in the Registry Editor.
Navigate to the following key and edit the string as required:
HKEY_LOCAL_MACHINE\Software\Avecto\Privilege Guard Client
REG_SZ PolicyPrecedence = "EPO,WEBSERVICE,WEBSERVER,GPO,LOCAL"
Only deployment methods listed in the Endpoint Privilege Management for Windows engineering key PolicyEnabled are applied, irrespective of the order listed in the PolicyPrecedence key. Both keys are located in the same place in the Windows registry.