Provision and Set up Single Sign-On
There are three parts to configuring single sign-on between Password Safe and Microsoft Entra ID (formerly Microsoft Azure AD):
- Create an Enterprise Application for Password Safe
- Configure Authentication and Authorization
- Configure Single Sign-On using Entra ID SAML Identity Provider
Create an Enterprise Application for Password Safe
You can use this document as an alternative to this section: https://www.beyondtrust.com/docs/beyondinsight-password-safe/bi/authentication/groups/entra-id.htm
To create an application in Entra ID:
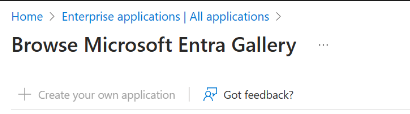
- From Enterprise applications, create an application, and then select Create your own application.
- Provide a name for the application, and select the Non-gallery option.
-
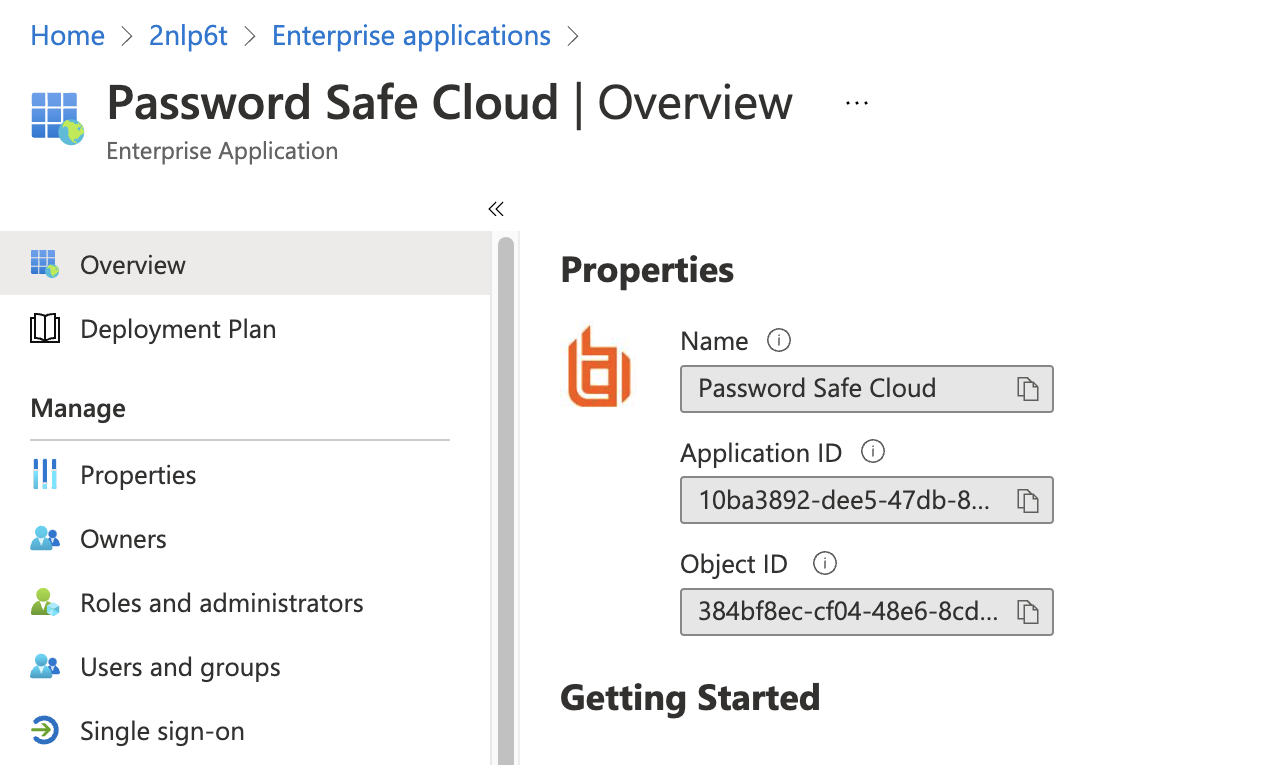
Once the application is created, on the Properties page, assign a logo.
Configure Authentication and Authorization
To configure authentication and authorization:
- Configure a service account for the Entra ID instance.
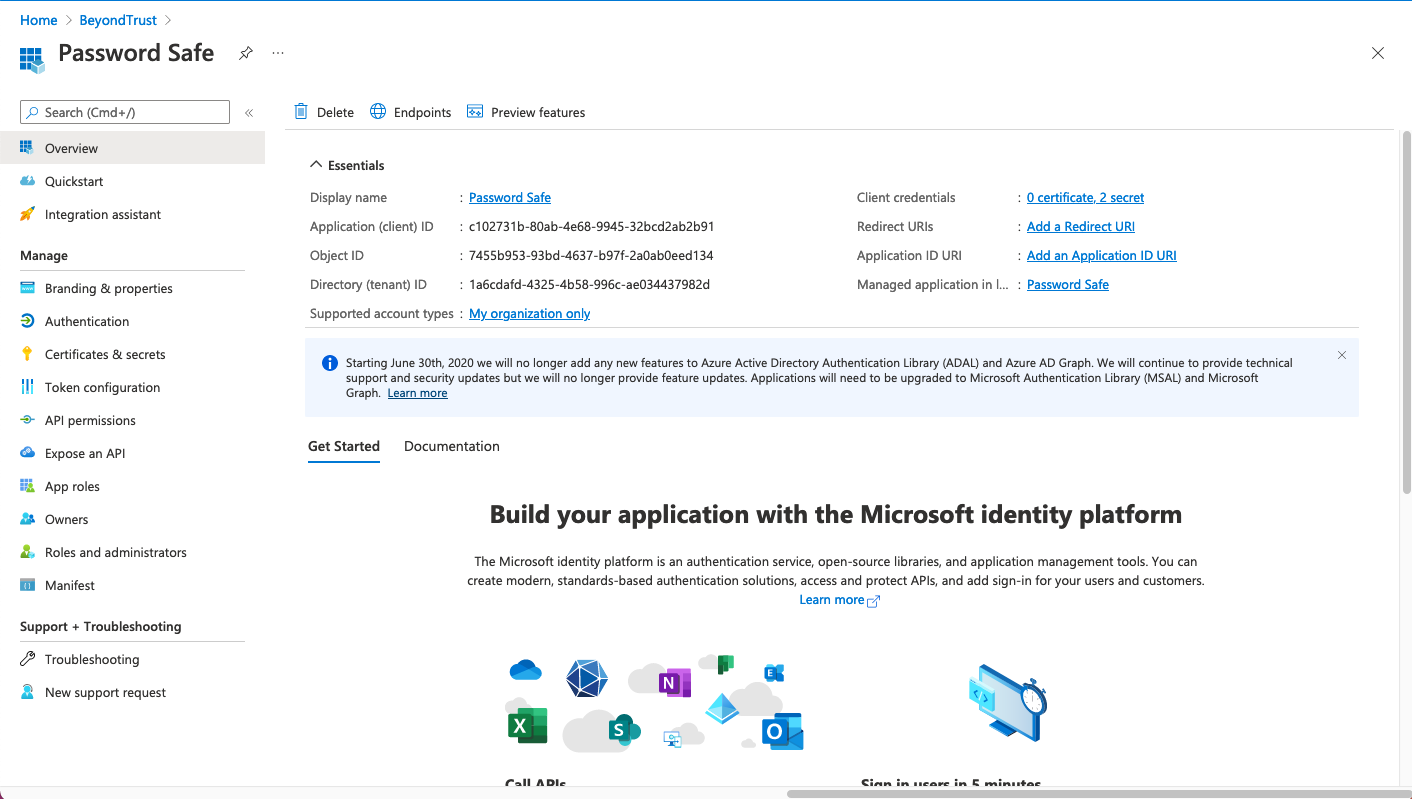
- Create an app registration for your application.
- Note the Application (client) ID and Directory (tenant) ID. You will copy these values later in Password Safe during the SAML configuration.
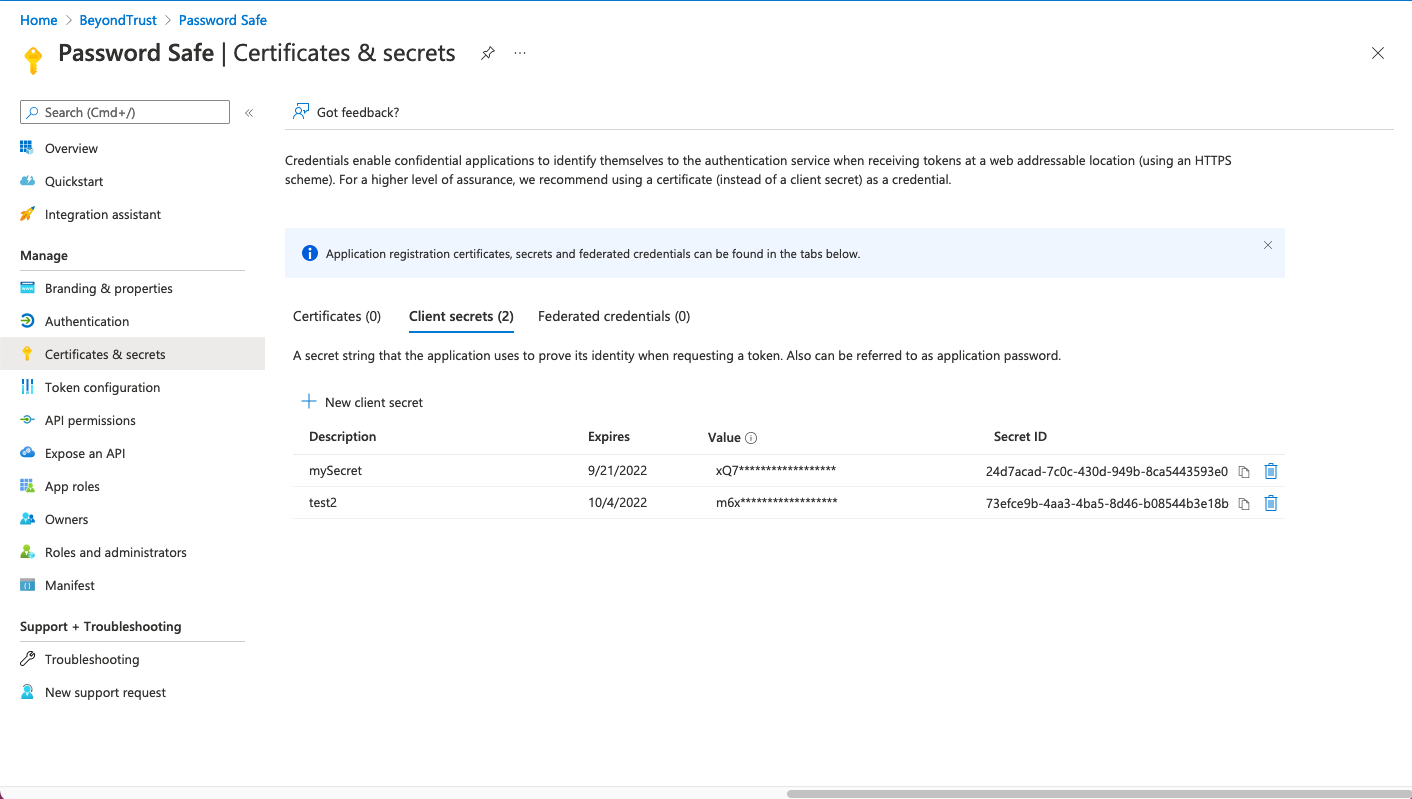
- On the Certificates & secrets page, under the application registration, create a client secret. Take note of the Value (client secret).
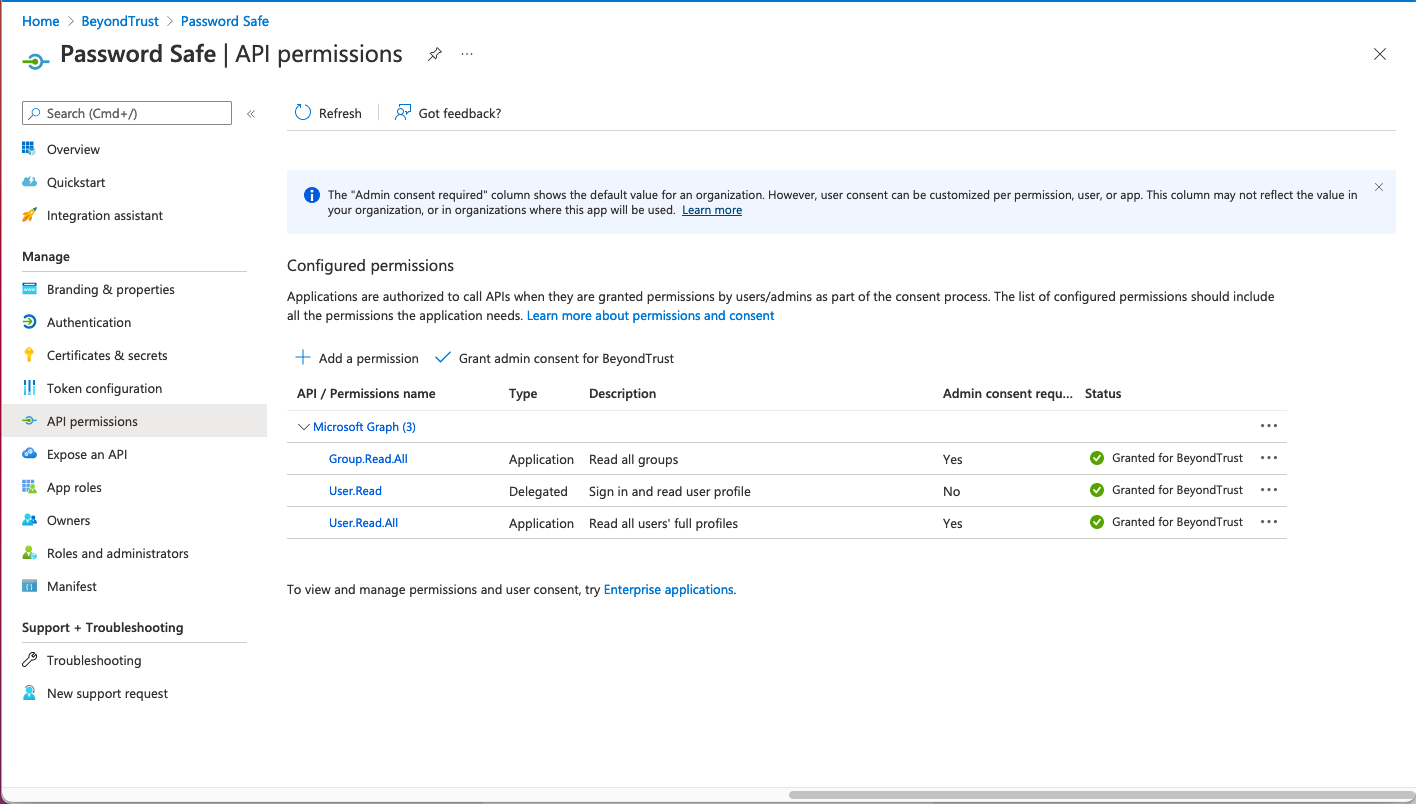
- Add API permissions to application registration.
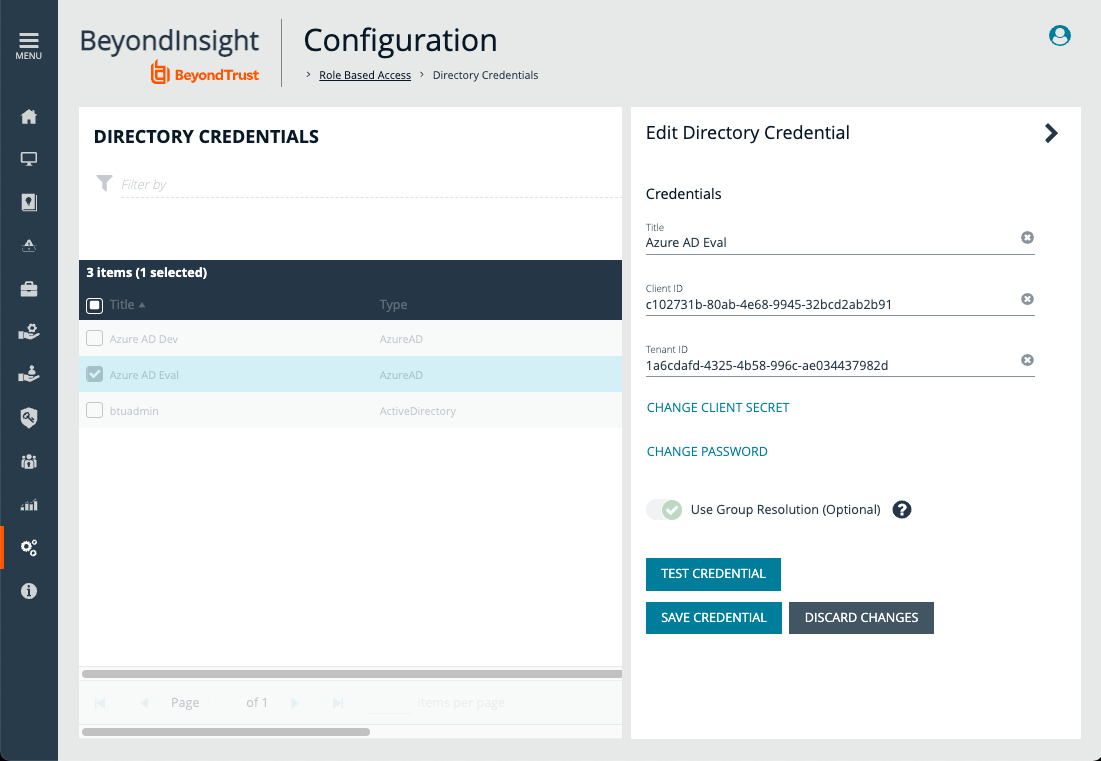
- After a service account is created, store the credentials in a Directory Credential object in Password Safe. Use the client and tenant IDs, and the client secret.
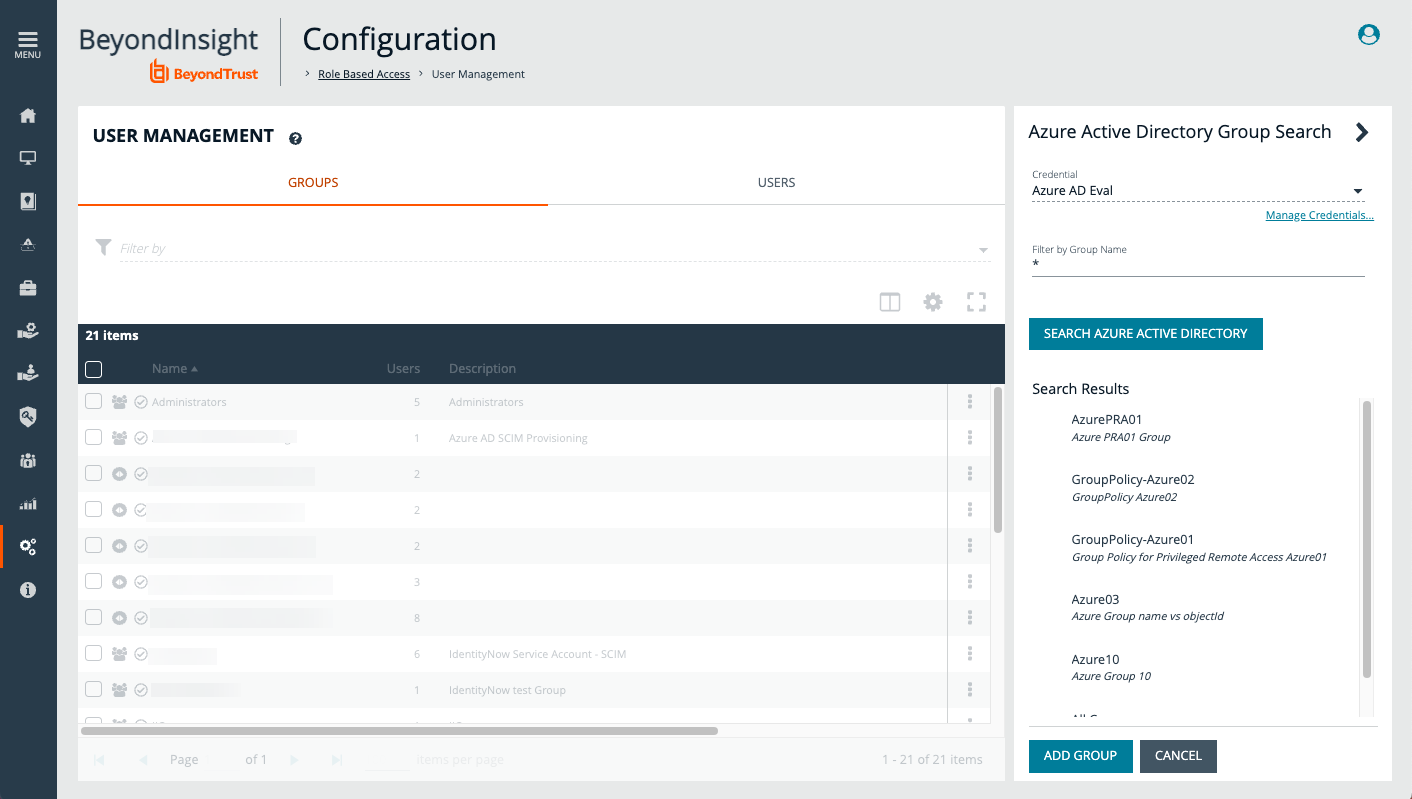
- At this point, test the credential. Under User Management, create an Entra ID group.
- With the previously created directory credential, browse and import Entra ID groups.
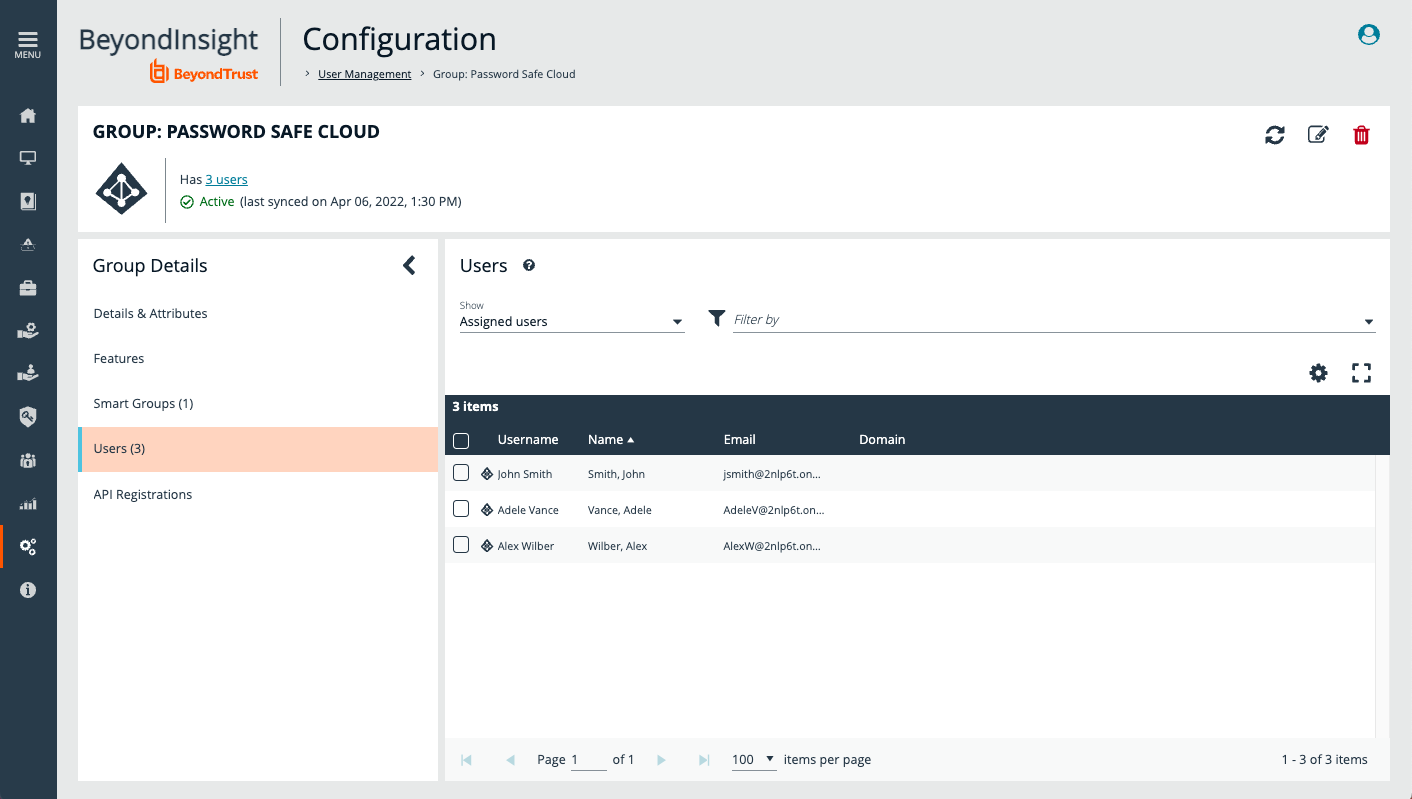
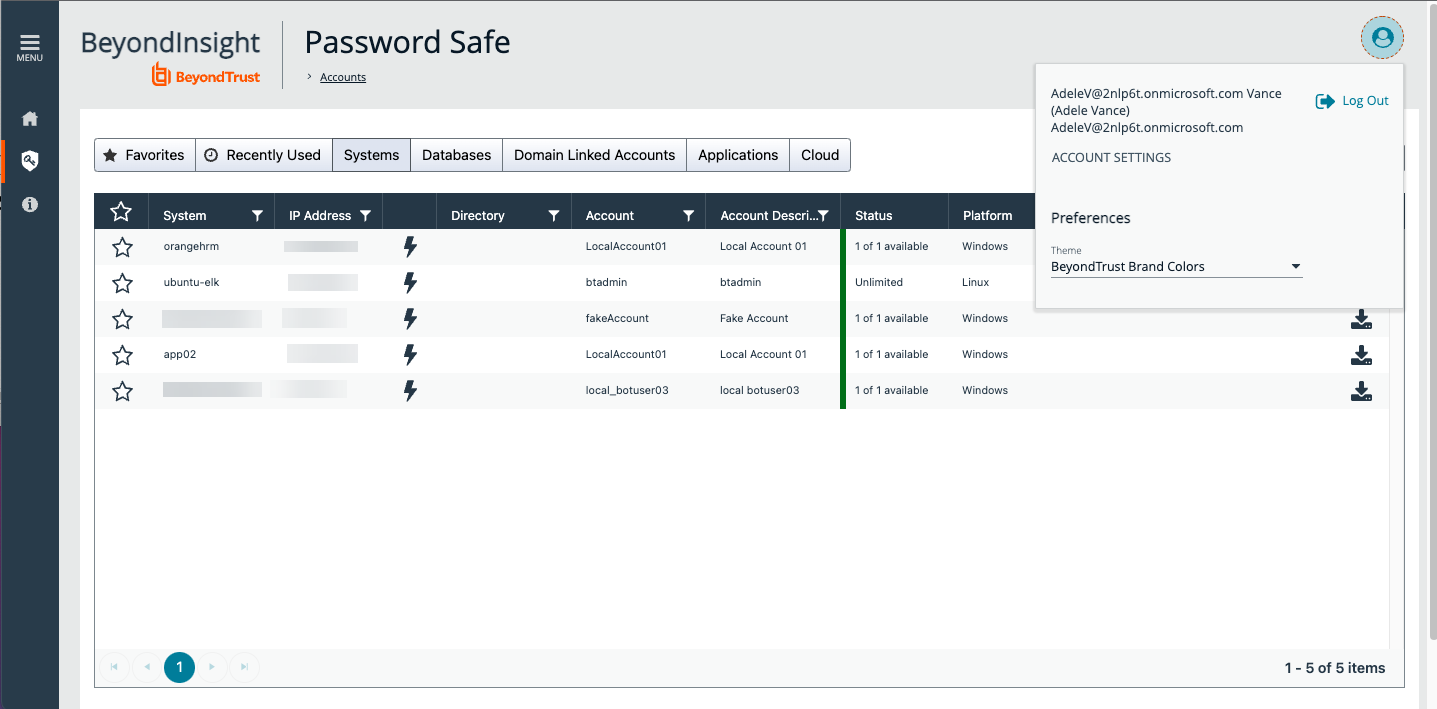
- Members in Entra ID and Password Safe are synchronized. Adding a new member to the group in Entra ID creates a new account in Password Safe with the permissions associated to the provisioning group.
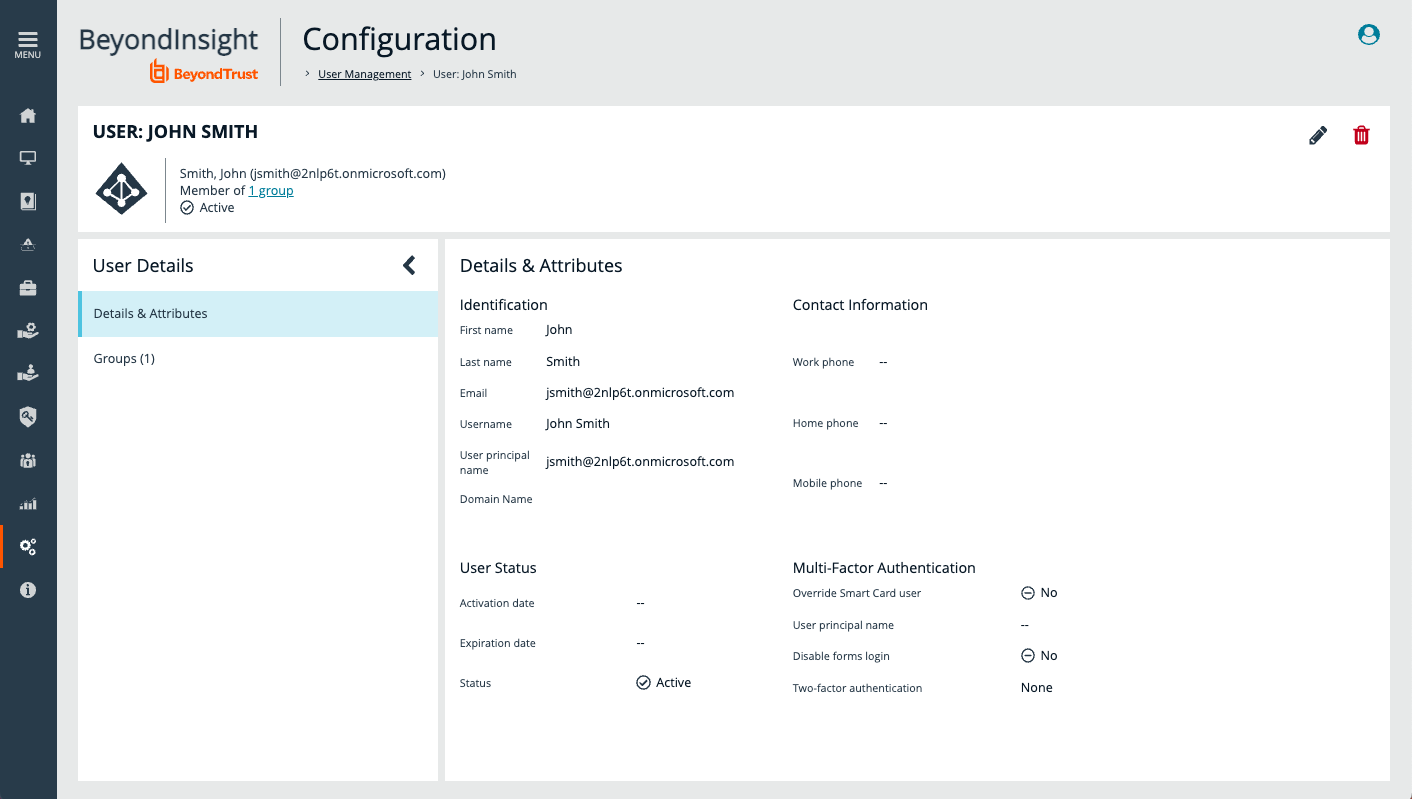
- The screen capture shows a new account provisioned in Password Safe when an Entra ID user is added to Entra ID group after the group is imported.
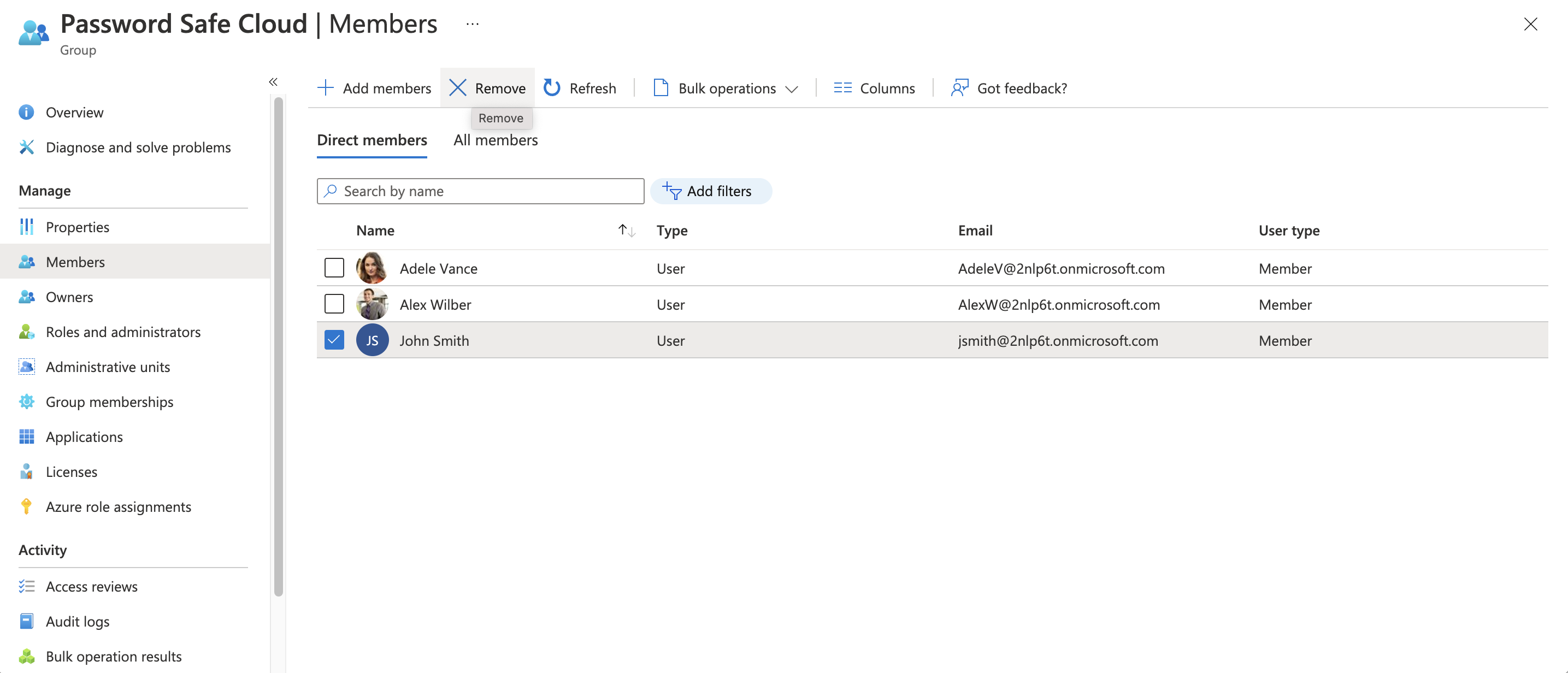
- Adding and removing members in Entra ID results in provisioning or deprovisioning of access in Password Safe.
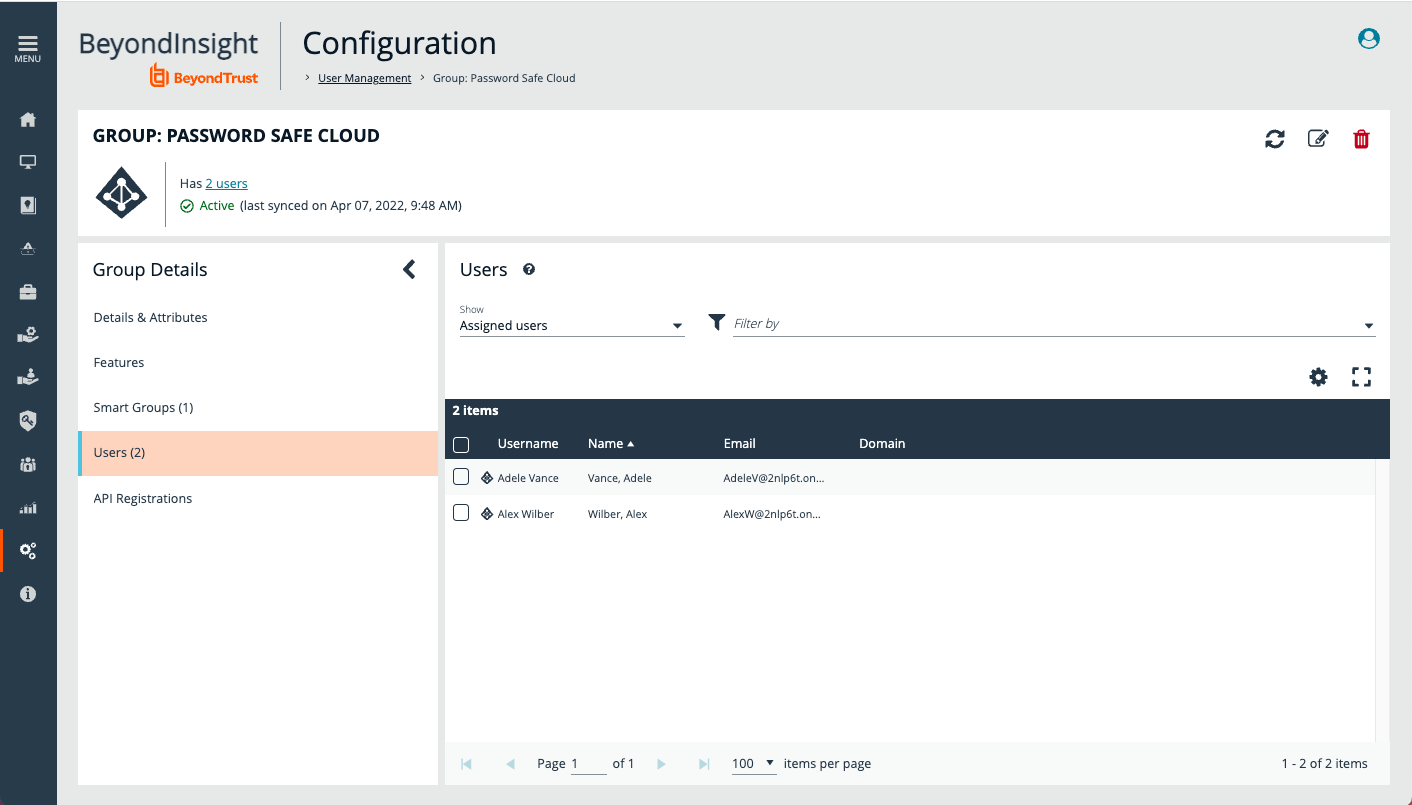
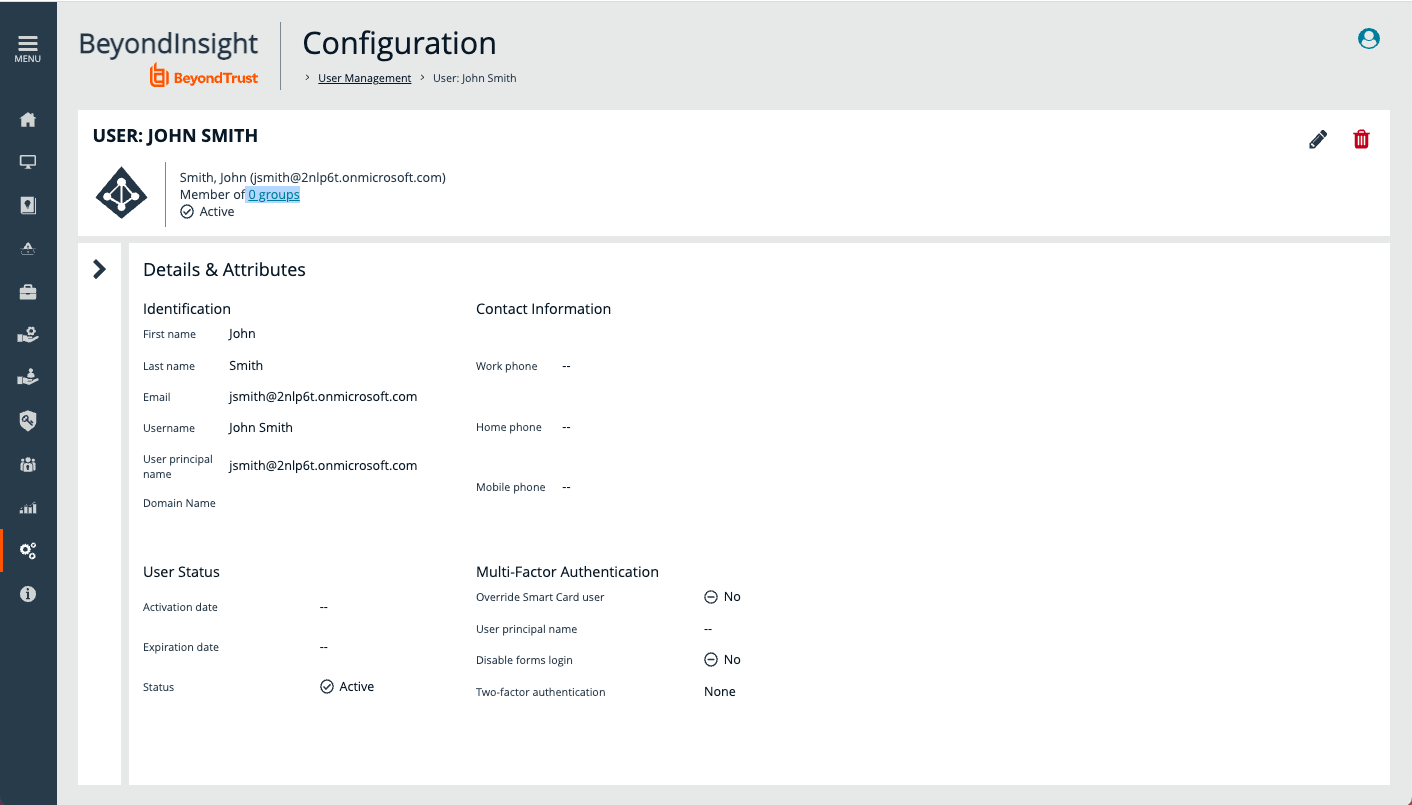
- After scheduled or manual synchronization, the removed member is removed from the group.
-
The account remains in Password Safe, but the removed user cannot access their account and cannot start a Password Safe session.
Entra ID group memberships for a user are synchronized every time the user logs in. For example, a user that has been removed from all Groups can no longer log in to Password Safe.
Configure Single Sign-On Using Entra ID SAML Identity Provider
Now go to the application created for Password Safe in Entra ID, under Enterprise applications. You must configure SAML in Password Safe, and the corresponding single sign-on configuration in the Entra ID application.
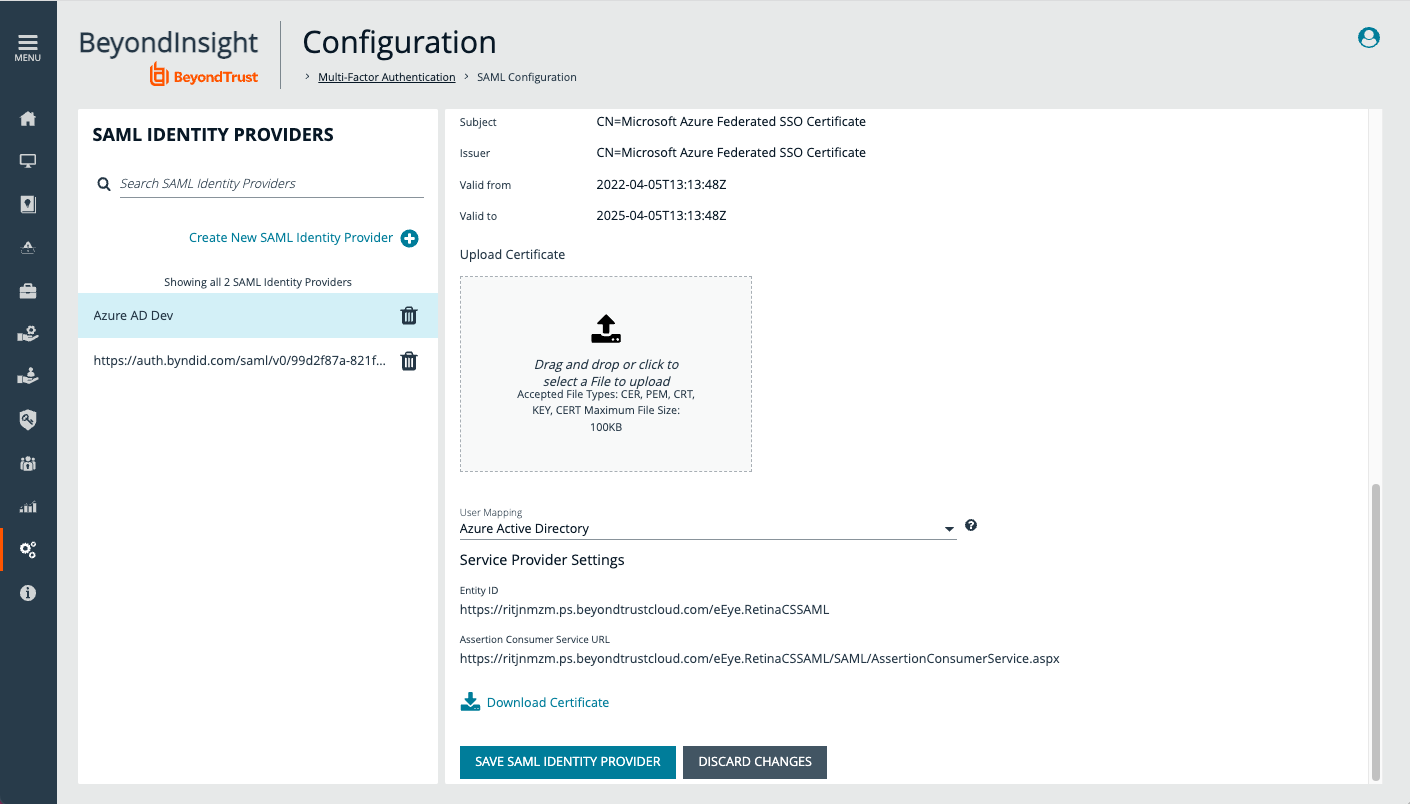
- The screen capture shows SAML configuration in Password Safe (BeyondInsight). Take note of Entity ID and Assertion Consumer Service URL.
- Set User Mapping to Entra ID.
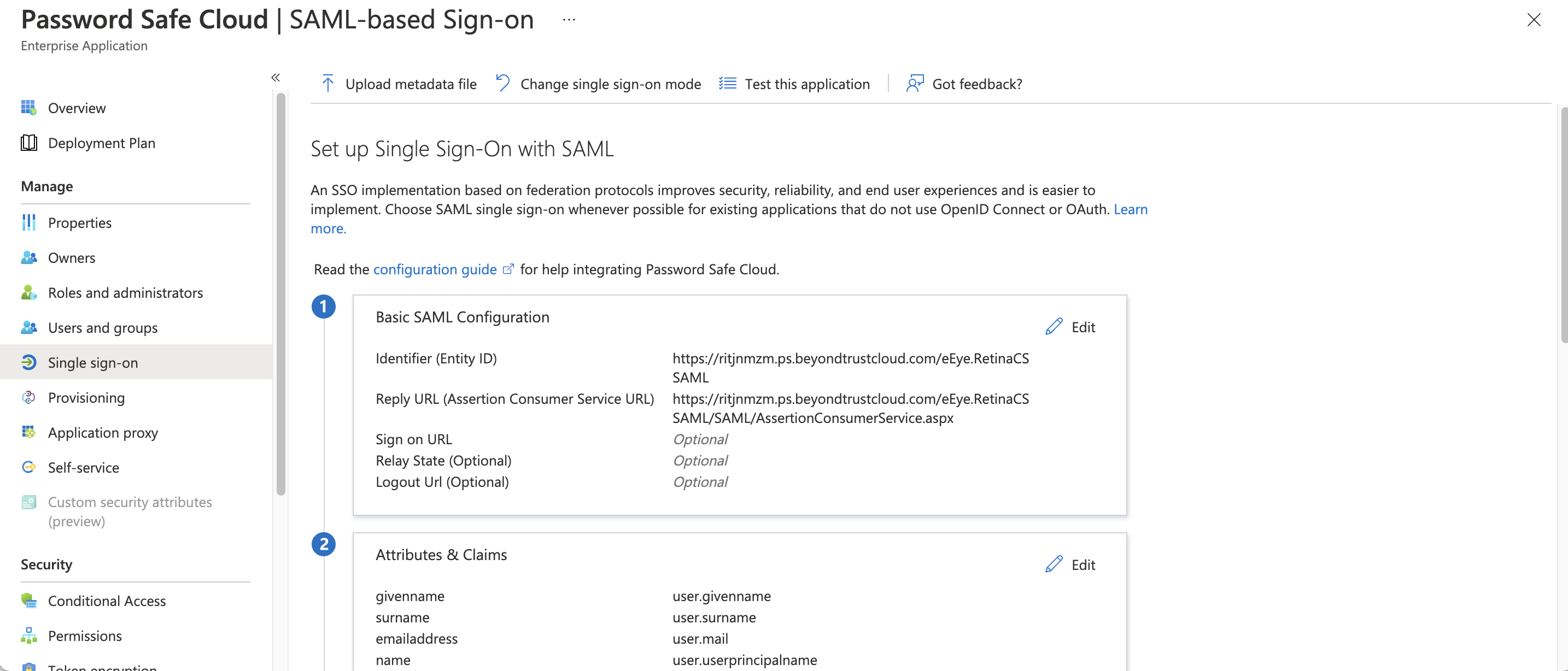
- The screen capture shows single sign-on configuration for Entra ID App. Enter the Password Safe Entity ID and Assertion Consumer Service URL.
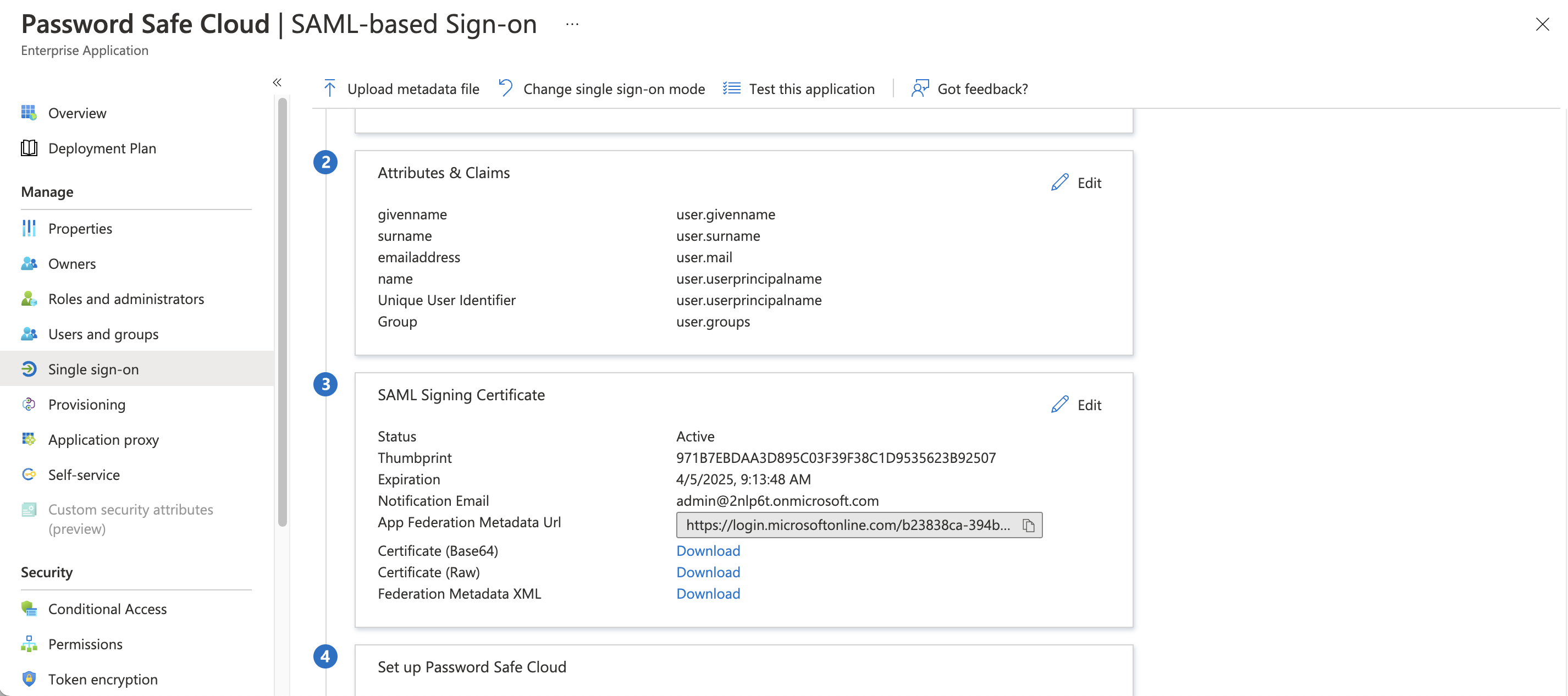
- Add the group (user.groups) to Attributes.
- Download Certificate (Base64) to import in Password Safe SAML configuration.
- Take note of the Login URL, Entra ID Identifier, and Logout URL.
-
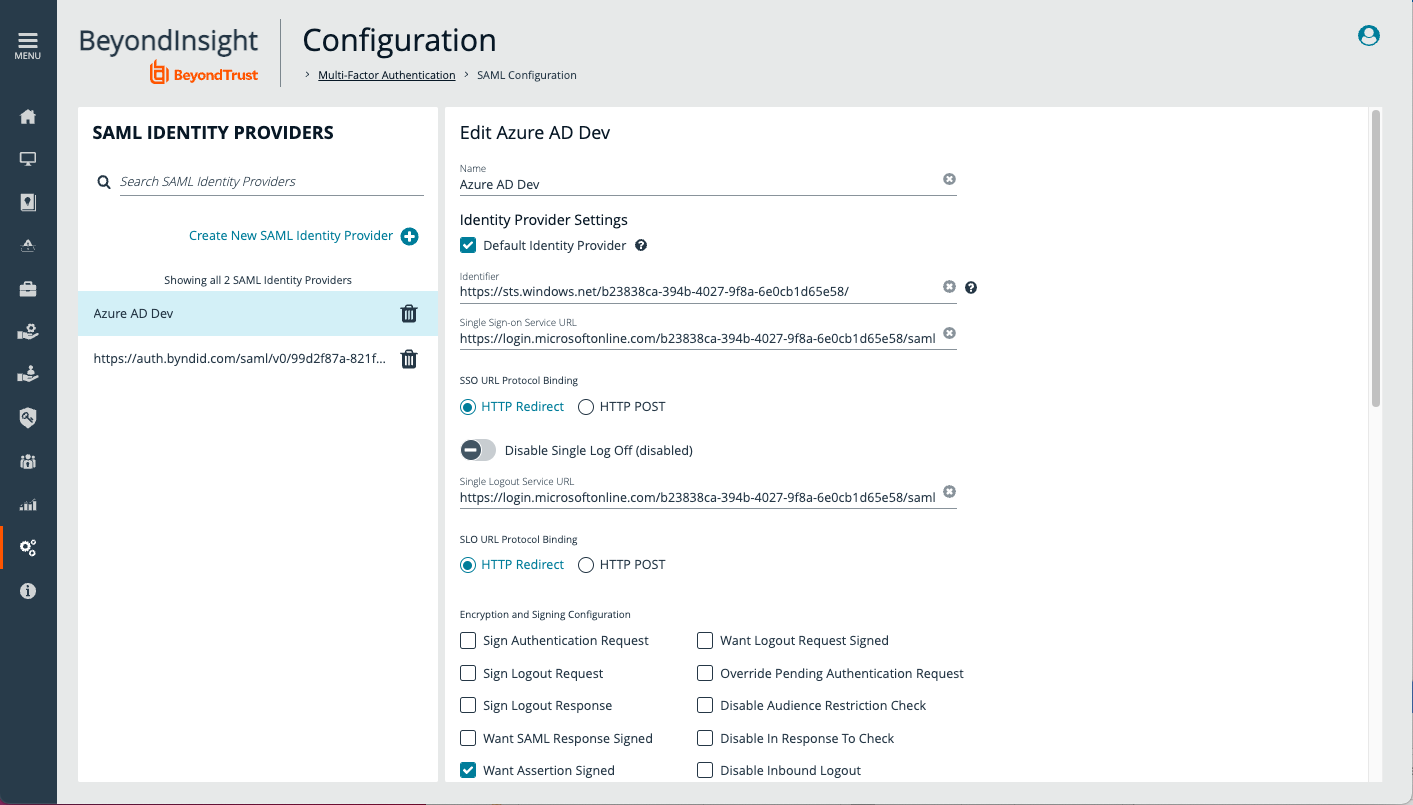
Complete the configuration in Password Safe by entering the Identifier (Entra ID Identifier), Single Sign-On Service URL(login URL) and Single Logout Service URL (logout URL).
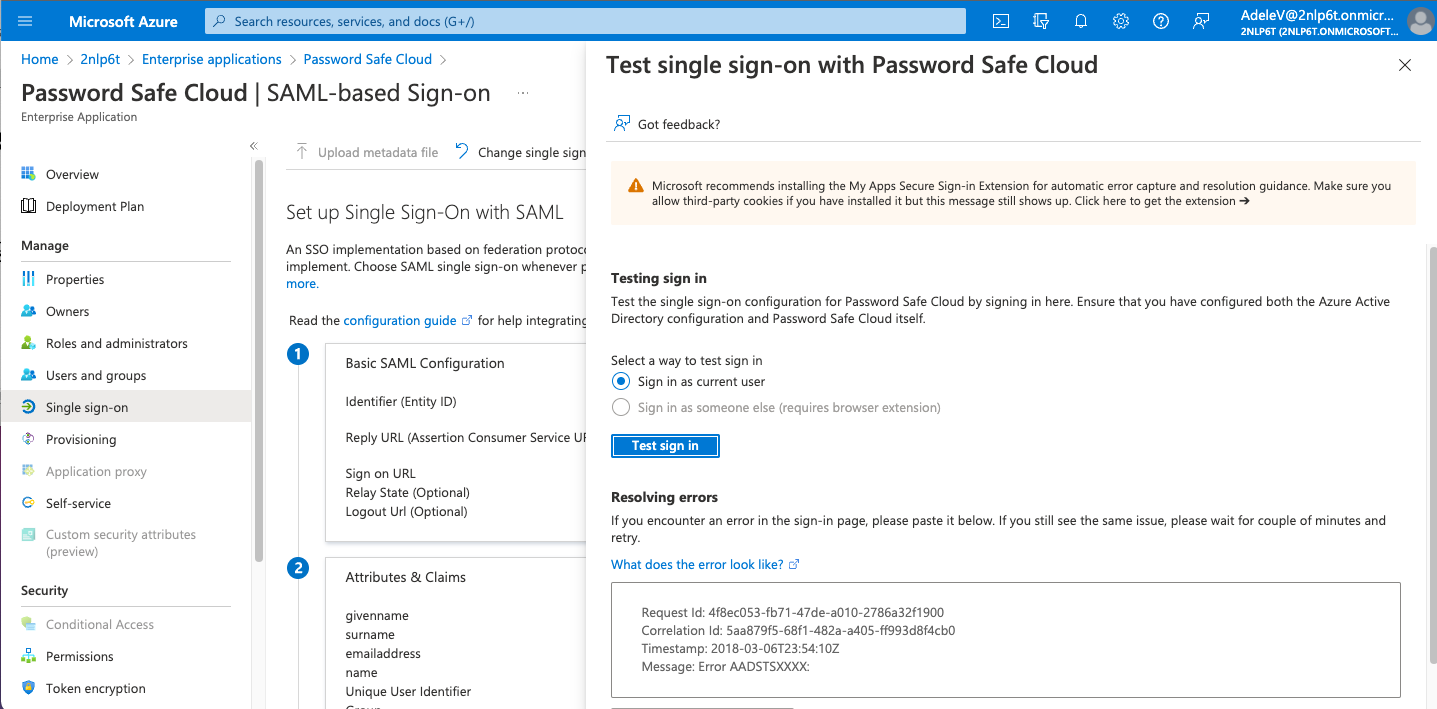
Test SSO
To test SSO with a test user:
- Log in as a test user and access the Enterprise applications.
- Click Test sign in to open a new browser tab for Password Safe. SAML assertion is sent to authenticate the user.
- The test user is authenticated (SSO) in Password Safe.
This completes the configuration of provisioning and SSO between Entra ID and BeyondTrust Password Safe and Password Safe Cloud.
For more information or to send comments, please send to integrations@beyondtrust.com