BeyondInsight Analytics & Reporting
BeyondInsight contains a data warehouse solution with business intelligence and analytics. This module extracts data from the BeyondInsight database and then processes the data in Microsoft SQL Server Integration and Analysis Services. You can browse these cubes in BeyondInsight, Microsoft SQL Server Management Studio, or using tools such as Microsoft Excel.
Using an on-premises BeyondInsight Analytics & Reporting deployment, you can perform the following:
- Run reports on:
- User accounts
- Asset details
- BeyondInsight user audit activity by user action, username, and IP address
- BeyondInsight, Endpoint Privilege Management, Password Safe, and Workforce Passwords licensing usage
- Password Safe activity, such as:
- Detailed view of all password and session activity
- Password Safe release and update activity
- Scheduled password changes
- Password age for managed accounts
- User and group entitlements
- Smart Rule details
- Assets and managed accounts that are associated with multiple Smart Rules
- Details on whether or not sessions were reviewed, when, and by whom
- Who has admin access to your managed applications
- User and product events and statistics
- Scan job history and metrics
- Secrets Safe entitlements
- Subscribe to reports to generate them on a schedule for automatic delivery to a network file share or through email.
- Save report views to easily reuse a report with predefined parameters.
- Download reports as the following file types: Word, Excel, PowerPoint, PDF, TIFF, MHTML (web archive), CSV (comma delimited), XML, data feed.
- Create report snapshots to save static views of report data.
- Interactively explore data and create and save custom reports with a pivot grid.
Using BeyondInsight Analytics & Reporting Cloud, you can perform the following:
- Run reports on:
- Scanned target details
- Asset details
- Password Safe and Workforce Passwords licensing usage
- BeyondInsight user audit activity by user action, username, and IP address
- Password Safe activity, such as:
- Detailed view of all password and session activity
- Password Safe release and update activity
- Scheduled password changes
- Password age for managed accounts
- User and group entitlements
- Smart Rule details
- Assets and managed accounts that are associated with multiple Smart Rules
- Details on whether or not sessions were reviewed, when, and by whom
- Who has admin access to your applications
- Secrets Safe entitlements
- Download reports as the following file types: Word, Excel, PDF, TIFF, CSV (comma delimited).
- Subscribe to reports to have them generated on a schedule and made available for file download from the subscription on the Analytics & Reporting page in BeyondInsight.
Prerequisites
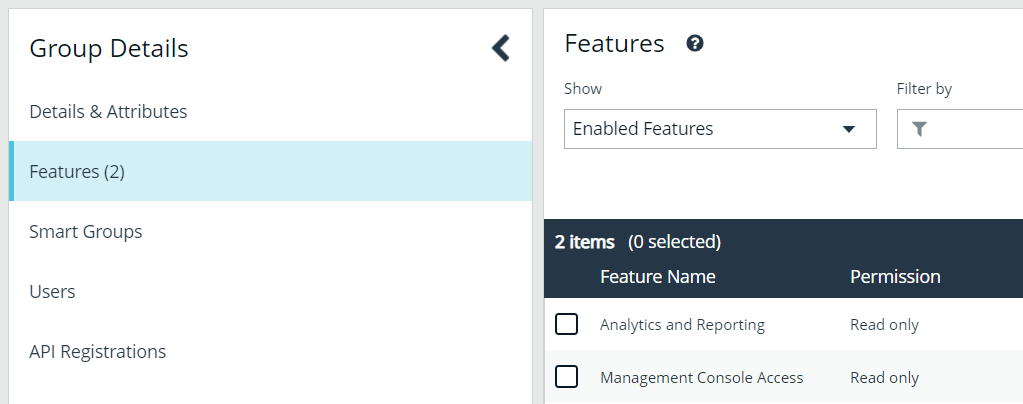
To view reports, users must have read permissions to the Analytics and Reporting and Management Console Access features, which are assigned at the user group level. Administrators can view all reports.
Some report categories are visible only when specific product licenses are detected and if read permissions have been assigned to the user group for specific features, as listed below.
| Report Category | License and Permission Requirement |
|---|---|
| Active Directory Bridge | AD Bridge license |
| Endpoint Privilege Management | Endpoint Privilege Management license and read permissions for the Endpoint Privilege Management feature |
| Licensing | Read permissions for the License Reporting feature |
| Privilege Management UNIX Linux | Privilege Management for Unix & Linux license and read permissions for the Endpoint Privilege Management for Unix & Linux feature. |
| Password Safe | Password Safe license |
| Secrets Safe | Password Safe license |
Report by category in an on-premises BeyondInsight deployment
The below table provides a list of reports, with their descriptions, found in each report folder in an on-premises deployment of BeyondInsight Analytics & Reporting.
| Report Folder | Report Name | Report Description |
|---|---|---|
| Account | Account Delta by Day | Shows the daily delta change for user accounts (added, removed, ending counts). |
| Account Delta by Month | Shows the monthly delta change for user accounts (added, removed, ending counts). | |
| Account Delta by Week | Shows the weekly delta change for user accounts (added, removed, ending counts). | |
| Account Last Login | Provides a list of user accounts with their last login date and time. | |
| Account Password Age by Last Scan | Provides a list of asset user accounts grouped by the latest password change date of each, as reported by the last successful scan. | |
| Database User List | Provides a list of database users with their details. | |
| User Account List | Provides a list of asset user accounts with their details, filtered by location, status, group membership and more. | |
| Active Directory Bridge | Access by Server | Shows users with logon access rights by server. |
| Access by User | Shows servers to which this user has been granted logon rights. | |
| Asset | Asset Delta | Shows asset change rate based on combined software, service, ports, and user accounts. |
| Asset Delta Details | Shows added and removed software, service, ports, and user accounts. | |
| Asset Item State | Shows assets missing one or more selected items. | |
| Asset Software Delta Trend | Shows the delta trend (added, removed, current) for software installed on assets. | |
| Asset Software Details by OS | Shows software installed by operating system. | |
| Assets Discovered | Lists discovered assets, grouped by operating system. | |
| Hardening Security Dashboard | Displays an asset hardening compliance dashboard. | |
| Operating System Discovered | Lists discovered operating systems with the count of assets. | |
| Smart Group Software Details | Provides a list of software installed on assets, grouped by Smart Group. | |
| Clarity | Event Review - Endpoint Privilege Management | Provides a breakdown of alert triggers for Endpoint Privilege Management events by threat level. |
| Event Review - Password Safe Release Events | Provides a breakdown of alert triggers for Password Safe Release events by threat level. | |
| Event Review - Privilege Management for Unix & Linux | Provides a breakdown of alert triggers for Privilege Management for Unix & Linux events by threat level. | |
| Top 10 Assets by Total Threat Level | Shows top 10 assets by overall threat level. | |
| Top 10 Users by Threat Level | Shows top 10 users by overall threat level. | |
| Configuration | Active Users | Provides a list of application users that have logged in to the console in X number of days. This is helpful in determining the active user count for licensing purposes, as well as for general housekeeping to disable accounts not being used. It also provides a total for the number of groups a user belongs to, which has a drillthrough option to see the group names. |
| BeyondInsight Entitlement by Group | Provides a detailed real-time view of group membership and permissions. | |
| Smart Rule Details | Provides a list of Smart Rules and details by type and category. | |
| User Audits | Shows the activity of BeyondInsight users by action, user name, IP address, and more, including ability to drill down into each row to view specific details. | |
| Console Reports > Asset | Port Delta | Shows the delta for ports between two date ranges grouped by assets. |
| Service Delta | Shows the delta for services between two date ranges grouped by assets. | |
| Software Delta | Shows the delta for software between two date ranges grouped by assets. | |
| User Account Delta | Shows the delta for user accounts between two date ranges grouped by assets. | |
| Assets | Shows the asset details for the selected host machines. | |
| Operating System | Shows the operating systems for the selected host machines. | |
| Port | Shows the ports for the selected host machines. | |
| Service | Shows the services for the selected host machines. | |
| Software | Shows the software for the selected host machines. | |
| User Account | Shows the user accounts for the selected host machines. | |
| Windows Events | Shows collected Windows events. | |
| Console Reports > Endpoint Privilege Management | Applications ActiveX Details | Provides a summary of Endpoint Privilege Management ActiveX details. |
| Applications By Computer | Provides a summary ofEndpoint Privilege Management applications by computer. | |
| Applications By Hash | Provides a summary ofEndpoint Privilege Management applications by hash details. | |
| Applications By Path | Provides a summary ofEndpoint Privilege Management applications by path details. | |
| Dashboard Report | Displays an Endpoint Privilege Management dashboard. | |
| File Integrity By Asset | Provides a summary of Endpoint Privilege Management file integrity by asset. | |
| File Integrity By Rule | Provides a summary of Endpoint Privilege Management file integrity by rule. | |
| Rule Justification | Provides a summary of Endpoint Privilege Management file integrity by rule justification. | |
| Shell Rule Executions | Provides a summary of Endpoint Privilege Management shell rule executions. | |
| Console Reports > Licensing | Password Safe User Licensing | Shows Password Safe logins by month, week, or day for a specified time period. |
| Console Reports > Scan | Discovery | Provides details for the list of targets scanned. |
| Network Discovery | Provides details for the list of targets scanned across multiple scans. | |
| Endpoint Privilege Management | Privileged Rule Impact Dashboard | Displays a dashboard that breaks down theEndpoint Privilege Management shell rule and custom rule applied events. |
| Requested Elevation Impact Dashboard | Displays a dashboard that breaks down theEndpoint Privilege Management application requested elevation and ActiveX events. | |
| UAC Impact Dashboard | Displays a dashboard that breaks down the Endpoint Privilege Management UAC prompt events. | |
| Agent Heartbeat Check Report | Provides a list of Endpoint Privilege Management agents that have not updated. | |
| Event Details Report | Provides a list of Endpoint Privilege Management event data listed by occurrence, filterable, and available for export in common for export in common formats. | |
| Event Rollup Report | Provides a list of Endpoint Privilege Management events grouped by occurrence, with user sort and custom filtering options. | |
| Events by Hour | Provides a weekly break down of Endpoint Privilege Management events by hour of the day. | |
| Events by Month | Shows Endpoint Privilege Management events trending by month. | |
| Events by User and Rule | Shows Endpoint Privilege Management events by user and rule. | |
| File Integrity Monitoring by Rule | Provides detailed reporting by asset and rule to determine file system changes. | |
| Lateral Movement and Suspicious Activity by User | Displays Endpoint Privilege Management activities, by user, common in lateral movement attacks. | |
| Shell Rule Usage | Shows shell rule events frequency and count by user. | |
| Licensing | BeyondInsight Product Usage Details by Organization | Provides a list of assets by organization for BeyondInsight license usage details. |
| Endpoint Privilege Management License Usage Report by User | Provides user event driven Endpoint Privilege Management license usage summary by month. | |
| Endpoint Privilege Management Product Usage Details by Organization | Provides a list of assets by organization for Endpoint Privilege Management license usage details. | |
| Password Safe Product Usage Details by Organization | Provides a list of assets and cloud accounts by organization for Password Safe license usage details. | |
| Usage Summary by Product and Organization | Shows the asset count by product and organization for license usage summary. | |
| Workforce Passwords Usage Summary | Provides a list of users with the ability to access the Workforce Passwords feature. | |
| Password Safe | Account Password Age by Last Scan | Provides a list of users along with the accounts they have access to. |
| Smart Rule Details | Provides a list of Smart Rules and details by type and category. | |
| Activity | Contains a detailed history of all Password Safe changes made to the appliance by any user. | |
| Admin Session Activity | Provides a detailed view of Password Safe admin session activities. | |
| Application Audit | Provides a list of who has administrative access to managed applications, by application name, Smart Group, user group, Password Safe role, username, and managed account. | |
| Application Inventory | Provides a list of application inventory details. | |
| Entitlement by Group | Provides a detailed view of Password Safe group membership and permissions. | |
| Entitlement by User | Provides a list of users along with the accounts they have access to. | |
| Inactive Managed Accounts | Provides a list of accounts that are inactive or not accessed by a requester in a specified number of days. The default number of days is 30. This can be modified. | |
| Managed Account Password Age | Lists all accounts managed by Password Safe along with the password age details. | |
| Managed vs Unmanaged Account Details | Provides a list of asset user accounts and their details, and indicates which are under Password Safe management. | |
| Password and Session Activity | Provides a detailed transactional view limited to top 50,000 Password Safe password and session activities. | |
| Password Release Activity | Provides a list of Password Safe password release activity details. | |
| Password Reset-on-Release Reconciliation | Provides auditable evidence that managed account passwords have been reset appropriately at session end, for any account configured with the Change Password after any release option. | |
| Password Update Activity | Lists details of Password Safe password update activity, showing which user initiated a manual password change by either UI or API. | |
| Password Update Schedule V2 | Lists details of upcoming scheduled password updates. | |
| Remote Session Activity | Provides a detailed view of Password Safe remote session activities. | |
| Reviewed Sessions | Provides details on when and who reviewed sessions, and provides a filter to show sessions that have not been reviewed. | |
| Scheduled Password Change Configuration | Provides details of Password Safe upcoming scheduled password changes. | |
| Service Account Usage | Provides a detailed list of what systems are using a Password Safe service account to start one or more services. | |
| Smart Rule Overlap | Shows assets or managed accounts that are selected for management in Password Safe by multiple Smart Rules. Overlapping Smart Rules cause an increase in database updates for account settings, which degrades system performance. | |
| Synchronized Accounts | Provides a list synchronized accounts. | |
| Privilege Management UNIX Linux | Dashboard Report | Displays a quick graphic and text overview of the most active Privilege Management for Unix & Linux hosts and users. |
| Event List | Shows a user-filtered list of Privilege Management for Unix & Linux events. | |
| Events By Hour | Shows a list of Privilege Management for Unix & Linux events by hour. | |
| Events by Status and Timeframe | Shows Privilege Management for Unix & Linux events trending report by month. | |
| Usage Statistics | Shows Privilege Management for Unix & Linux event statistics in graph form: top 10 hosts, commands, users, and accept and reject breakdown. | |
| Scan | Authentication Summary Alert | Provides a summary of authentication alerts for selected Smart Groups. |
| Authentication Alerts by Smart Group | Shows assets listed for each authentication alert for a selected Smart Group. | |
| Scan Job History by Day | Shows job execution history grouped by day. | |
| Scan Job History by Month | Shows job execution history grouped by month. | |
| Scan Job Metrics | Shows job execution metrics by scan agent. | |
| Secrets Safe | Secrets Safe Entitlement Report | Provides a list of user groups and the secrets they are entitled to. |
| Sudo Manager | Dashboard Report | Displays a Sudo events dashboard showing a quick graphic and text overview of the most active hosts and users. |
| Event List | Provides a Sudo event list showing a user-filtered list of events. | |
| Events by Hour | Shows Sudo events by hour. | |
| Events by Status and Timeframe | Provides a Sudo events trending report by month. | |
| Usage Statistics | Shows Sudo event statistics in graph form: top 10 hosts, commands, users, accept and reject breakdown. |
Report by category in BeyondInsight cloud
The table below provides a list of reports, with their descriptions, found in each report folder in BeyondInsight Analytics & Reporting Cloud.
| Report Folder | Report Name | Report Description |
|---|---|---|
| Scan | Discovery | Provides details for the list of targets scanned. |
| Network Discovery | Provides details for the list of targets scanned across multiple scans. | |
| Asset | Assets | Shows the asset details for the selected host machines. |
| Service | Shows the services for the selected host machines. | |
| Software | Shows the software for the selected host machines. | |
| User Account | Shows the user accounts for the selected host machines. | |
| Operating System | Shows the operating systems for the selected host machines. | |
| Port | Shows the ports for the selected host machines. | |
| Windows Events | Shows collected Windows events. | |
| Licensing | Password Safe User Licensing | Shows Password Safe logins by month, week, or day for a specified time period. |
| Workforce Passwords Usage Summary | Provides a list of users with the ability to access the Workforce Passwords feature. | |
| Configuration | User Audits | Shows the activity of BeyondInsight users by action, user name, IP address, and more, including ability to drill down into each row to view specific details. |
| Password Safe | Activity | Contains a detailed history of all Password Safe changes made to the appliance by any user. |
| Password Release Activity | Provides a list of Password Safe password release activity details. | |
| Password Update Activity | Lists details of Password Safe password update activity. | |
| Password Update Schedule | Lists details of upcoming scheduled password updates. | |
| Managed Account Password Age | Lists all accounts managed by Password Safe along with the password age details. | |
| Account Password Age by Last Scan | Provides a list of users along with the accounts they have access to. | |
| Service Account Usage | Provides a detailed list of what systems are using a Password Safe service account to start one or more services. | |
| Scheduled Password Change Configuration | Provides details of Password Safe upcoming scheduled password changes. | |
| Password and Session Activity | Provides a detailed transactional view limited to top 50,000 Password Safe password and session activities. | |
| Admin Session Activity | Provides a detailed view of Password Safe admin session activities. | |
| Entitlement by User | Provides a list of users along with the accounts they have access to. | |
| Entitlement by Group | Provides a detailed view of Password Safe group membership and permissions. | |
| Inactive Managed Accounts | Provides a list of accounts that are inactive or not accessed by a requester in a specified number of days. The default number of days is 30. This can be modified. | |
| Application Inventory | Provides a list of application inventory details. | |
| Smart Rule Details | Provides a list of Smart Rules and details by type and category. | |
| Remote Session Activity | Provides a detailed view of Password Safe remote session activities. | |
| Smart Rule Overlap | Shows assets or managed accounts that are selected for management in Password Safe by multiple Smart Rules. Overlapping Smart Rules cause an increase in database updates for account settings, which degrades system performance. | |
| Reviewed Sessions | Provides details on when and who reviewed sessions, and provides a filter to show sessions that have not been reviewed. | |
| Application Audit | Provides a list of who has administrative access to managed applications, by application name, Smart Group, user group, Password Safe role, username, and managed account. | |
| Secrets Safe | Secrets Safe Entitlement Report | Provides a list of user groups and the secrets they are entitled to. |