AD Bridge Password Safe Integration
You can add AD Bridge agent machines as managed systems to AD Bridge Password Safe.
The following instructions assume that Password Safe is successfully installed.
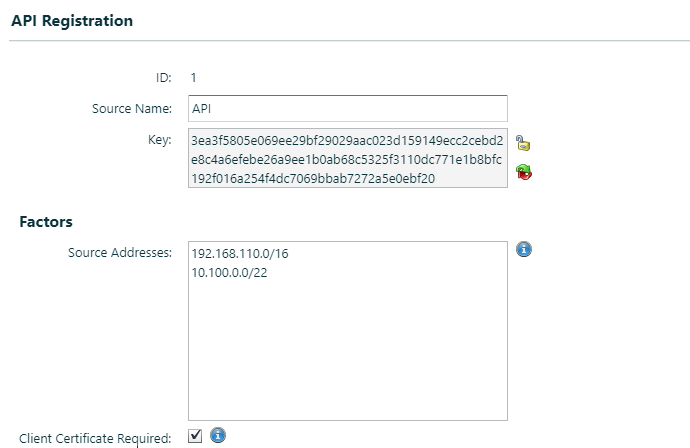
Configure the API
To configure the API:
- In the BeyondInsight management console, go to the API Registration configuration page.
- Add a source name, generate a key, and add IP addresses.
- Check the Client Certificate Required box.
Create an API User
You must create a user account in Password Safe that can use the Password Safe API.
For more information about configuration, refer to the Password Safe Administration Guide.
To create the user account:
- In the BeyondInsight management console, go to the Users & Groups configuration page.
- Create a group.
- Set permissions and select at least one Smart Rule.
- Check the Enable Application API box, and then check the box for the application (created in Configure the API).
- After the group is created, create a user account. Create a user name that will easily identify the user (for example, apiuser).
Create a Managed Account
Keep the following in mind when creating the managed account:
- The managed account must be the same as the account in Active Directory.
- The account will be used for the domain join. This user must have permissions to complete a domain join on a Linux/Unix agent.
- On the Managed Account Settings page, the user needs the Enable for API access box checked.
- The domain information needs to be populated for the domain you want to join.
Configure the Agent
There are two ways to configure the agent.
Regardless of the option chosen, the information in the configuration file needs to be defined. The information is from Password Safe and is defined in the sample template below.
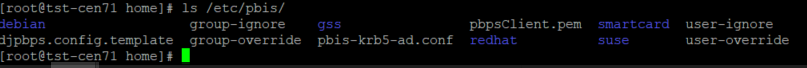
The configuration file is: djpbpbs.config.template and is installed in the /etc/pbis folder.
Option 1
If the API key created does not require the user to have a certificate, then a user name and password combination can be used in the djpbp.config.template. This can be done by defining the API user and password and leaving the Certificate section commented out.
Sample djpbps.config.template:
[Version]
Template = 1 # Do not modify.
[DomainJoin]
# User account to use for domain join. In addition, this account must
# also be a managed account in Password Safe with API access enabled.
DomainJoinUser = ' '
[PasswordSafe]
# Password Safe URL
ServerUrl = 'https://0.0.0.0.' # eg. https://server-name
# From Password Safe web console Configuration->Users & Groups->User Group.
# Check box "Enable Application API"
RunAsUser = ''
# Optional. Needed if Password Safe web console shows "User Password Required"
# is checked in Configuration->API Registration. Uncomment if required.
#RunAsUserPassword = ''
# From Password Safe web console Configuration->API Registration->Key
ApiKey = ' ' #eg.
4b2c430dbe2b6aff66b016cc8e11b0f78b4d7cc426d3fd4c53c92a261226fbe8ce8f0b5f42974789210420196c6539135c492834123c93ed6f7d53023dfa9a4a'
# Minutes PBPS credential is valid until it expires.
# Optional. Valid range is between 1 and 10079 inclusive.
# Default is 1 minute. Uncomment if required.
#DurationMinutes = 1
# Client Certificate.
# Optional. Needed if Password Safe web console shows "Client Certificate
# Required" is checked in Configuration->API Registration.
# If given, the certificate is stored in /etc/pbis/pbpsClient.pem.
# Default is not to use the client certificate.
# Uncomment if required.
ClientCertificate = """
-----BEGIN PRIVATE KEY-----
-----END PRIVATE KEY-----
-----BEGIN CERTIFICATE-----
-----END CERTIFICATE-----
"""
# CA Certificate
# Optional. Specify if PBIS agent should verify PBPS server.
# If given, the certificate is stored in /etc/pbis/pbpsCA.pem.
# Default is not to verify. Uncomment if required.
#CACertificate = """
#-----BEGIN CERTIFICATE-----
# ...
# ...
# ...
#-----END CERTIFICATE-----
#"""
Option 2
Export Password Safe Certificates
Certificates can be exported from the U-Series Appliance appliance Maintenance page.
To export a certificate:
- Log on to the U-Series Appliance appliance Maintenance page URL (for example, PasswordSafe_URL/Maintenance).
- Select Security Settings from the menu.
- Select Export Client Certificate.
Use Password Safe to Join an Agent to a Domain
After the configuration file is completed with the correct information, the agent machine is ready for integration with Password Safe.
To run the domainjoin with the config file, run it as: /opt/pbis/bin/domainjoin-cli verbose join --ou test --configFile /tmp/djpbps.config example.com.
A configuration file only has to be included in the domain leave if the user is using the –deleteAccount option. For example, /opt/pbis/bin/domainjoin-cli leave --configFile /tmp/djpbps.config –deleteAccount.
If the user is not issuing a domain leave with the deleteAccount flag, the configuration file does not need to be specified.