Privileged Access Discovery Application
- Uncover privileged accounts and credentials
- Identify account misconfigurations: overprivileged accounts, unused accounts, old passwords, and more
- Get unlimited scans, detailed scan results, and a summary report of all findings
Trusted by Over 20,000 Companies and Counting
Quantify Your Risk of Exposure
Stolen privileged credentials or compromised remote access tools are used in nearly every data breach. Use the Privileged Access Discovery Application to run unlimited scans—on up to 1,000 network targets at a time. Shine a light on vulnerable accounts and tools living on your network. Then, apply that information to correct privileged access, address poor password hygiene, and mitigate other privilege-related vulnerabilities.
Scope Out Your Risk
View the full scope of your privileged accounts: the number of credentials, password ages, service accounts, and users running with admin rights.
Identify Urgent Threats
Generate a report that displays the most urgent privileged account security risks on your network.
Reveal Remote Access Tools
Discover which remote access tools are being used—and could become a backdoor threat.
How the Privileged Access Discovery Application Works
The Privileged Access Discovery Application identifies account misconfigurations including overprivileged accounts, service accounts using user identities, and unused accounts. By identifying the age of passwords, it points to unused accounts or accounts that have not had their passwords rotated. It also finds remote access tools you might not know are present on your network.
The data and reporting generated by the application is available only to you. Passwords aren't recorded, and no sensitive data is retained by the utility.
Start discovering what’s on your network today, tomorrow, or whenever your environment changes.
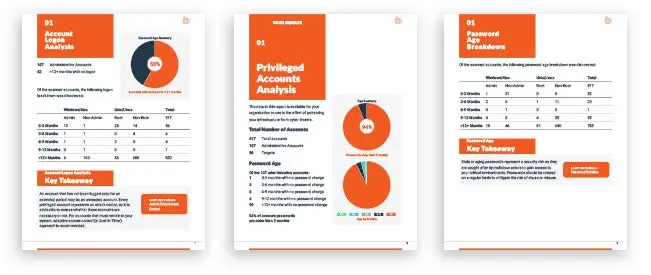
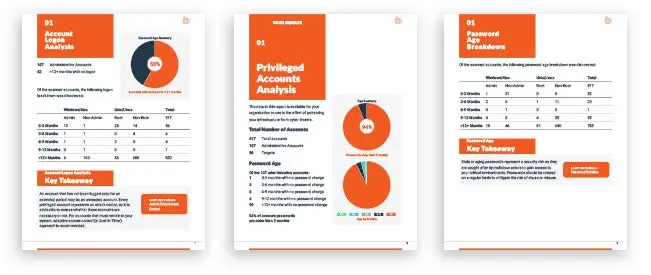
Explore a Sample Report
The Privileged Access Discovery Application produces an overview report of the privileged activity within your organization. Inside, you’ll gain new insight into the systems on your network, including privileged accounts, SSH keys, services, and remote access tools—pinpointing where your biggest security challenges lie.
Illuminate Privileged Access Risk, Then Address It
Understanding your privileged access security challenges is a crucial step for organizations. Objectives including risk management, threat mitigation, zero trust security, and cyber insurance qualification depend on privileged account security.
The Impact of Unidentified Privileges
An increased vulnerability to privilege escalation attacks, lateral movement, insider threats, and more
Without visibility into privileged accounts, security teams cannot accurately assess risks
According to Forrester Research, about 80% of breaches directly or indirectly involve privileged credentials
Identify Remote Access & Support Risks
Overlapping remote support solutions pose substantial risk to your organization, negatively impact productivity and user experience, and may be financially inefficient. The first step to consolidating remote support is identifying which tools are active on your network.
The Risks of Redundant Remote Tools Include:
- Complicated Service Processes
Bouncing between different remote support tools generates unnecessary friction between ticket resolution and user satisfaction.
- Manual Overhead Sink
Poorly integrated tools adds to the amount of hands-on work assigned to your service technicians and distracts from the mission.
- Hidden Security Gaps
Patchwork solutions built from several different tools leaves a lot of attack surface unmanaged — or unmanageable.
- Overpaying for Redundant Tools
Different teams may be using different tools to accomplish the same goal, leaving you paying double.

Ready to Consolidate? Try Remote Support
BeyondTrust Remote Support provides a centralized, all-in-one tool built to supply your service desk with powerful controls and visibility into all remote support access. Integrate with trusted tools like ServiceNow and Microsoft Teams, record and log all sessions automatically, simplify session hand-off, and much more.





