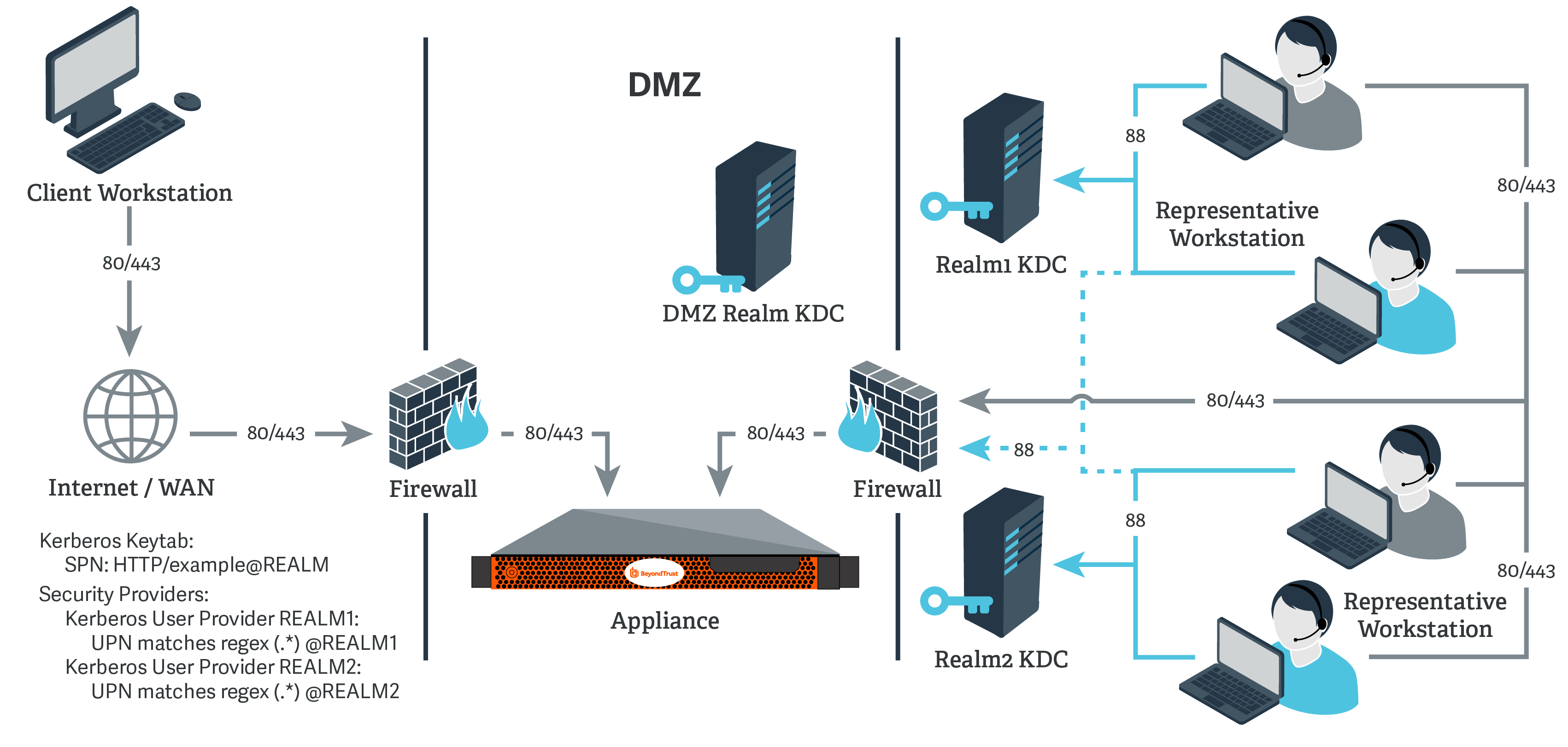
Network Setup: Kerberos KDC in Multiple Realms
Overview
For this example:
- The B Series Appliance may or may not be located behind a corporate firewall.
- Representatives may or may not be on the same network as the B Series Appliance.
- Representatives may belong as members of multiple Kerberos realms existing in the corporate infrastructure (traditionally, a multi-domain hierarchy in Windows).
- If a DMZ realm exists, the representatives' realms may have inbound trusts with that DMZ realm, allowing principals in the trusted realms to obtain tickets for services in the DMZ realm.
Configuration
- Register one or more of the SPNs according to the following rules:
- If a DMZ Kerberos realm is involved, register a unique SPN within the DMZ realm.
- If no DMZ Kerberos realm is involved and no trust exists between the two realms, register a unique SPN in each realm.
- If no DMZ Kerberos realm is involved and trust exists between the two realms, register a unique SPN in a realm of your choosing.
- Export all registered SPNs.
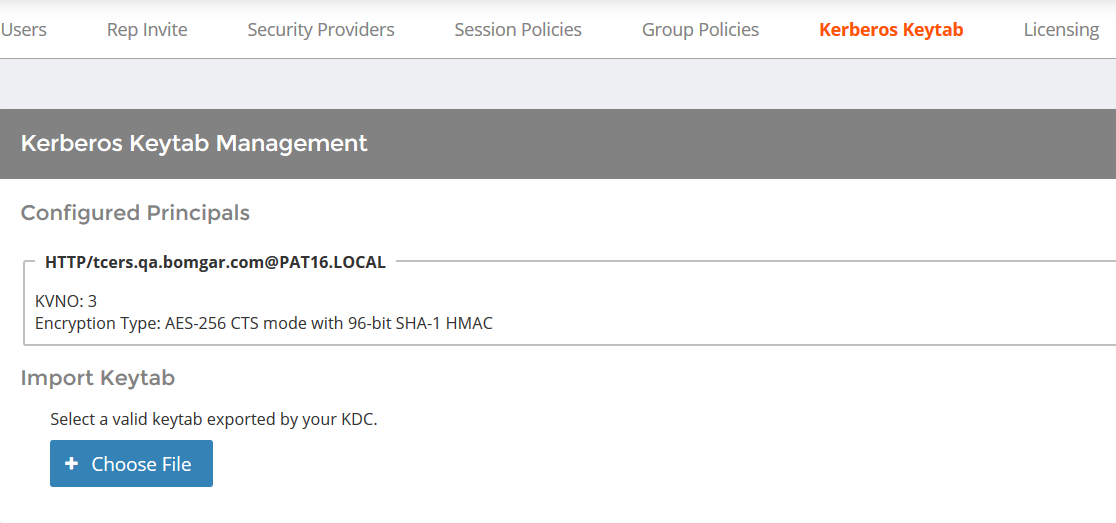
- Log in to your B Series Appliance's /login interface.
- Go to Users & Security > Kerberos Keytab.
- Under Import Keytab, click Choose File, and then select the exported keytab to upload. You should now see this SPN under the list of Configured Principals.
- Repeat the previous step for each exported keytab.
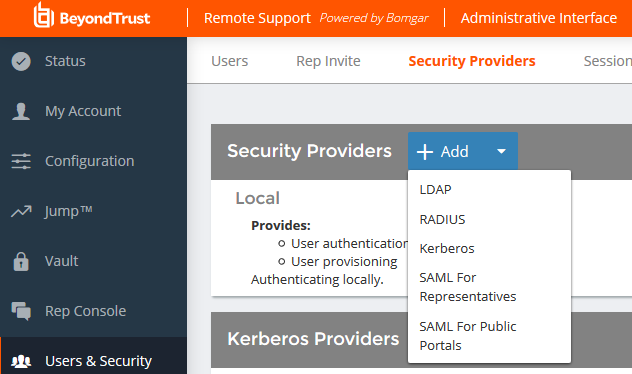
- Go to Users & Security > Security Providers. Click Add. From the dropdown, select Kerberos.
- Create a unique name to help identify this provider.
- Be sure to check the Enabled box.
- Choose if you want to synchronize display names.
- Optionally, select to remove the REALM portion from the User Principal Name when constructing the BeyondTrust username.
- If using a DMZ realm or using the same SPN for multiple realms, you will want to match on user principle name to identify users from the first realm.
- If you registered multiple SPNs, choose the SPN that users from the first realm will use.
- You may also select a default group policy for users who authenticate against this Kerberos server.
- Click Save to save this security provider configuration.
- Repeat steps 7 through 15 for each realm from which users will authenticate, substituting the UPN or SPN rule for each realm as appropriate.