Networking
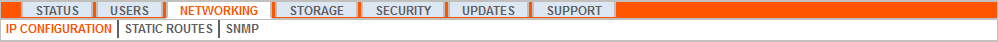
IP Configuration: Configure IP Address and Network Settings
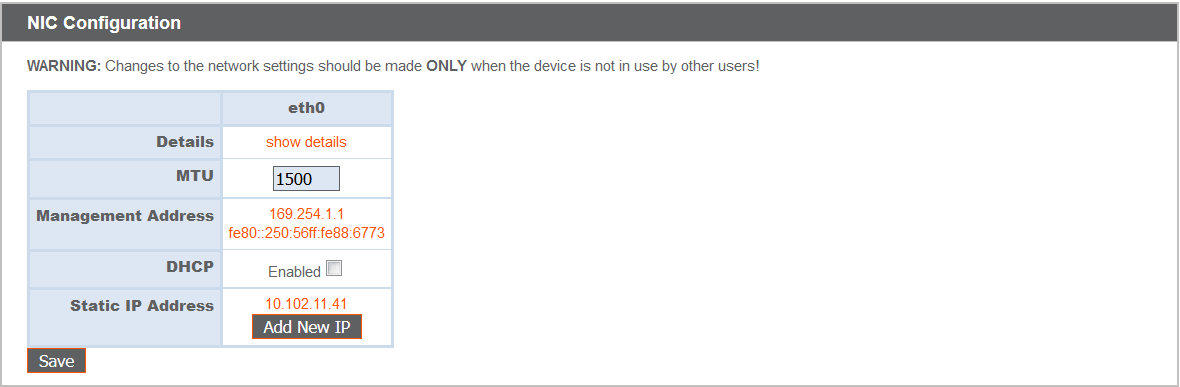
Companies with advanced network configurations can configure multiple IP addresses on the B Series Appliance’s ethernet ports. Using multiple ports can enhance security or enable connections over non-standard networks. For example, if employees are restricted from accessing the internet but need to provide off-network support, using one port for your internal private network and another for the public internet allows users worldwide to access systems without breaching your network security policies.
NIC teaming combines your system's physical network interface controllers (NICs) into a single logical interface. NIC teaming operates in "Active-Backup" mode. One of the NICs is used to carry all network traffic. If the link on that NIC is lost for any reason, the other NIC becomes active. Before activating NIC teaming, please ensure that both NICs are connected to the same network segment (subnet) and that you have IP addresses configured on only one of the existing NICs.
If you are using a Virtual or Cloud Appliance environment, the Enable NIC Teaming option is not available.
Although multiple IP addresses can be assigned to each NIC, do not configure either NIC such that it has an IP address that is in the same subnet as an IP address on the other NIC. In this scenario, packet loss occurs with packets originating from the IP on the NIC that does not have the default gateway. Consider the following example configuration:
- eth0 is configured with the default gateway of 192.168.1.1
- eth0 is assigned with 192.168.1.5
- eth1 is assigned with 192.168.1.10
- Both eth0 and eth1 are connected to the same subnet switch
Given this configuration, traffic from both NICs are sent to the default gateway (192.168.1.1) regardless of which NIC received traffic. Switches configured with dynamic ARP send packets randomly to either eth0 (192.168.1.5) or eth1 (192.168.1.10), not both. When eth0 receives these packets from the switch destined for eth1, eth0 drops the packets. Some switches are configured with static ARP. These switches drop all packets received from eth1 since this NIC does not have the default gateway and is not present in the static ARP table of the gateway. If you wish to configure redundant NICs on the same subnet, us e NIC teaming.
By default, Dynamic Host Configuration Protocol (DHCP) is enabled for your B Series Appliance. DHCP is a network protocol that uses a DHCP server to control the distribution of network parameters, such as IP addresses, allowing systems to automatically request these parameters. This reduces the need to manually configure settings. In this case, when checked, an IP address is obtained from the DHCP server and is removed from the pool of available IP addresses.
To learn more about DHCP, please see Dynamic Host Configuration Protocol (DHCP).
Click Show Details to view and verify transmission and reception statistics for each ethernet port on the B Series Appliance.
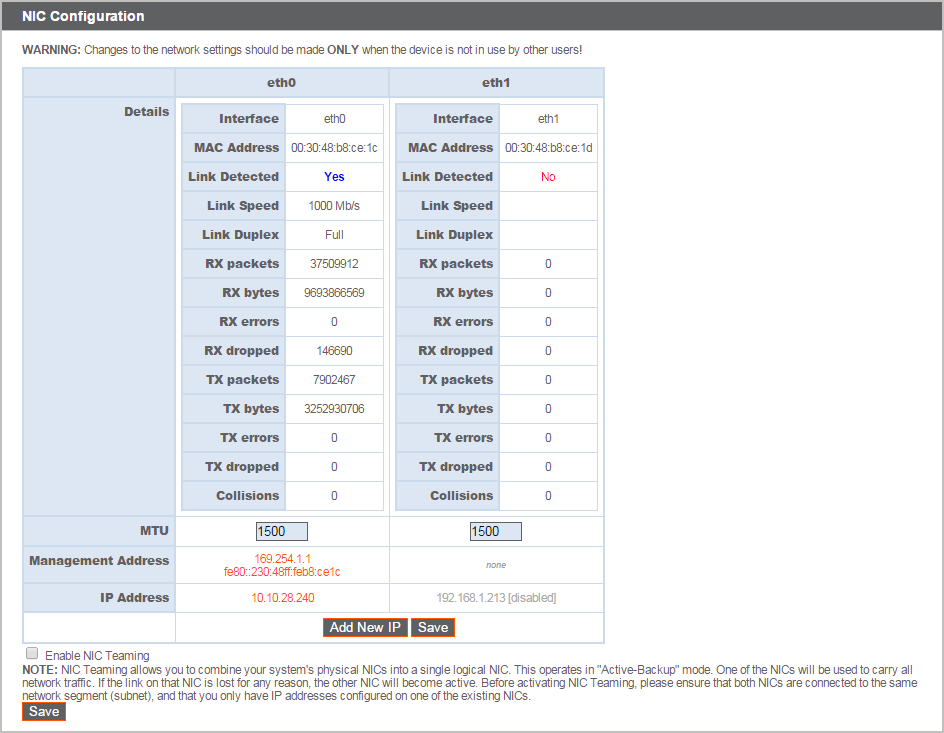
Under the Global Network Configuration section, configure the hostname for your BeyondTrust Appliance B Series.
The Hostname field does not need to meet any technical requirements. It does not affect what hostname client software or remote users connect to. (To make these changes, see /login > Status > Information > Client Software Is Built to Attempt. If the hostname attempted by the client software needs to change, notify BeyondTrust Technical Support of the needed changes so that Support can build a software update.) The Hostname field exists primarily to help you distinguish between multiple B Series Appliances. It is also used as the local server identifier when making SMTP connections to send email alerts. This is useful if the SMTP Relay Server specified at /appliance > Security > Email Configuration is locked down. In this case, the configured hostname might have to match the reverse-DNS lookup of the B Series Appliance's IP address.
Assign a default gateway, selecting which ethernet port to use. Enter an IP address for one or more DNS servers.
Allow your B Series Appliance to respond to pings if you wish to be able to test if the host is functioning. Set the hostname or IP address for a Network Time Protocol (NTP) server with which you wish your B Series Appliance to synchronize.
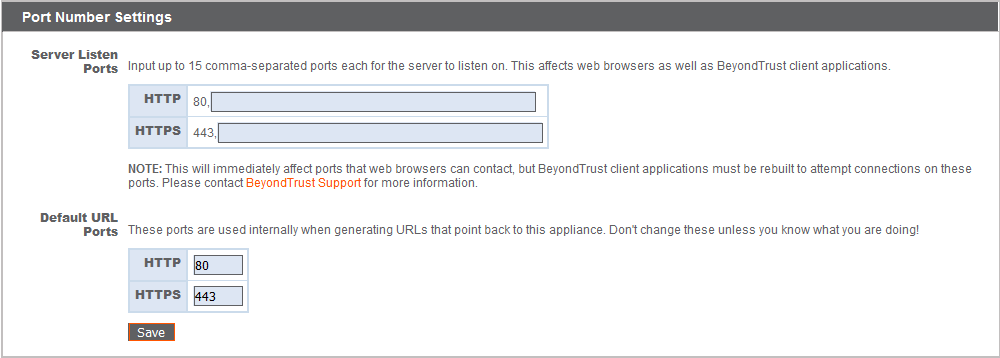
Two settings are available in the Port Number Settings area: Server Listen Ports and Default URL Ports. When configuring these, keep in mind that connections made to valid ports may be rejected by network restrictions set in /appliance > Security > Appliance Administration and in /login > Management > Security. The opposite is also true: connections made to invalid ports are rejected even if such connections satisfy network restrictions.
The Server Listen Ports section allows you to configure ports for the B Series Appliance to listen on. You may specify up to 15 comma-separated ports for HTTP and 15 comma-separated ports for HTTPS. Each port may appear only once in any field, and it may appear in only one field, not both. The B Series Appliance responds to HTTP connections made to any of the ports listed in the HTTP field, and the B Series Appliance responds to HTTPS connections made to any of the ports in the HTTPS field. You cannot change the built-in listen ports (80 and 443).
To access the B Series Appliance on a given port using a browser requires that you enter the port in the URL of the browser (e.g., support.example.com:8200). Clients downloaded from the B Series Appliance attempt connections to the ports listed on the /login > Status > Information page under Client Software Is Built to Attempt. These ports are not configurable from /login or /appliance. To change them, you must contact BeyondTrust Support and have a new update built for your B Series Appliance. Once installed, the update sets the Attempt ports as specified by BeyondTrust Support in the parameters of the update.
Default URL Ports are used when generating URLs that point back to the B Series Appliance, such as session keys generated from the representative console. When the default ports are blocked on the network (or can be expected to fail for any other reason), you can change the default URL ports to have generated URLs spawn with the ports that you specify. Whatever ports you enter should also be listed in the Server Listen Ports; otherwise, the default ports are not connected. For example, if you enter 8080 in the Default URL Port field, make sure 8080 is also in the HTTP or HTTPS Listen Port field. Unlike the listen port fields, you cannot enter more than one port in either of the URL port fields. You cannot enter the same port in both fields.
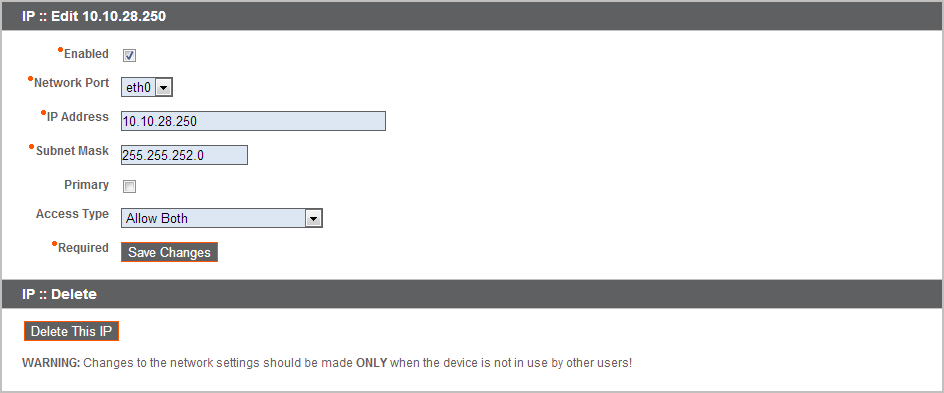
When adding or editing an IP address, choose whether that IP should be enabled or disabled. Select the network port on which you would like this IP to function. The IP Address field sets an address to which your B Series Appliance can respond, while Subnet Mask enables BeyondTrust to communicate with other devices.
When editing an IP address that is on the same subnet as another IP address for this B Series Appliance, choose if this IP address should be Primary. When this box is checked, the B Series Appliance designates this IP address to be the primary or originating IP address for the subnet. This helps, for example, to ensure that any network traffic originating from the B Series Appliance on that subnet matches and complies with defined firewall rules.
From Access Type, you can restrict access over this IP to the public site or all clients (including mobile and web consoles) outside of the normal web traffic. Use Allow Both (web and session traffic) to allow access for both the public site and all clients.
It is possible to separate the web and session traffic by changing the configuration of the network. The exact process depends on the existing configuration of the network. For more information, contact Support.
To restrict access to the /login interface, set network restrictions under /login > Management > Security. To restrict access to the /appliance interface, set network restrictions under /appliance > Security > Appliance Administration.
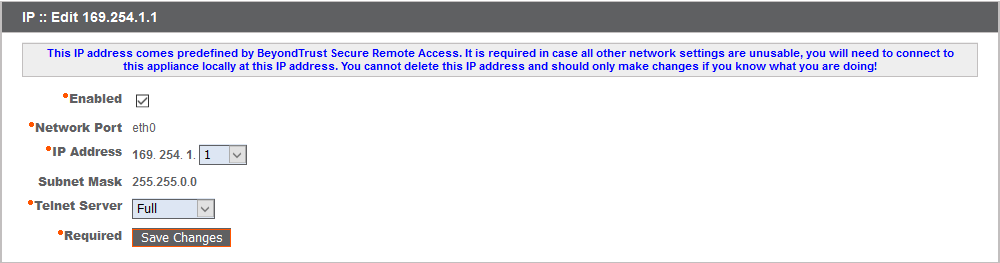
When viewing the management IP address1, the Telnet Server dropdown provides three settings: Full, Simplified and Disabled, as detailed below. These settings change the menu options of the telnet server that is available only on this private IP and that can be used in emergency recovery situations. Since the telnet feature is specifically tied to the built-in private IP, it does not appear under any other configured IP addresses.
| Setting | Function |
|---|---|
| Full | Enables the telnet server with full functionality |
| Simplified | Allows four options: View FIPS Error, Reset to Factory Defaults, Shutdown, and Reboot |
| Disabled | Completely disables the telnet server |