BeyondTrust Appliance B Series Network Infrastructure
DNS: Each BeyondTrust Appliance B Series needs a physical connection to the network and a separate IP address. Additionally, a Domain Name System (DNS) record for each B Series Appliance is recommended, along with the DNS A Record or a Canonical Name (CNAME) record pointing to the B Series Appliance. Since any customers you support using BeyondTrust use the public portal name you give them to request remote support, the simple yet descriptive name is the best approach. For instance, a company named 'Example' might use support.example.com for their DNS record.
Some companies have network standards and guidelines for DNS names that may increase the complexity of the site name. For instance, the 'Example' company might require every DNS name to include the geographical region and department within the name, such as usa.hr.example.com. This name is difficult to use and remember. In this instance, the best practice is to create a CNAME that ultimately points to the B Series Appliance and public site. The CNAME is usa.hr.example.com, as shown below:
support.example.com
|
CNAME
|
usa.hr.example.com
|
usa.hr.example.com
|
A
|
192.0.2.23
|
Here is one more example, using the common foo bar terminology:
foo.example.com
|
CNAME
|
bar.example.com
|
bar.example.com
|
A
|
192.0.2.23
|
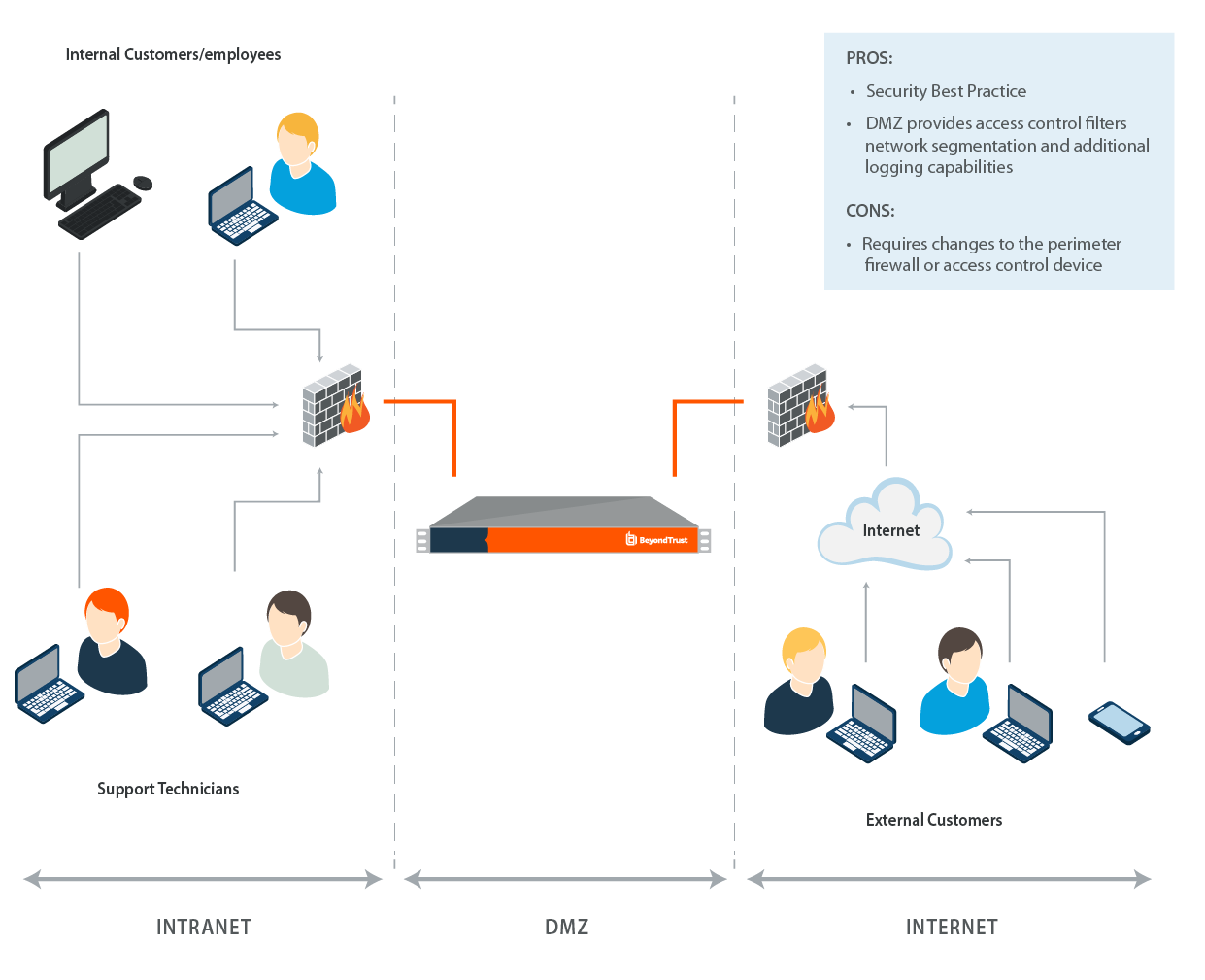
Deployment Options
DMZ Deployment (recommended): Deploying the B Series Appliance into a perimeter-based DMZ segment meets security best practice standards and is BeyondTrust's recommended location for the secure deployment of the device. A DMZ, or de-militarized zone, is a network that is protected by access control mechanisms. Access control may be provided by a firewall device, a router, or a switch that provides port and address filtering capabilities. The purpose of the DMZ is to limit access to systems that are deployed within it. In the case of the B Series Appliance, the DMZ will limit connectivity to the device and allow access only to the appropriate ports.
For more information, please see Example Firewall Rules Based on B Series Appliance Location.
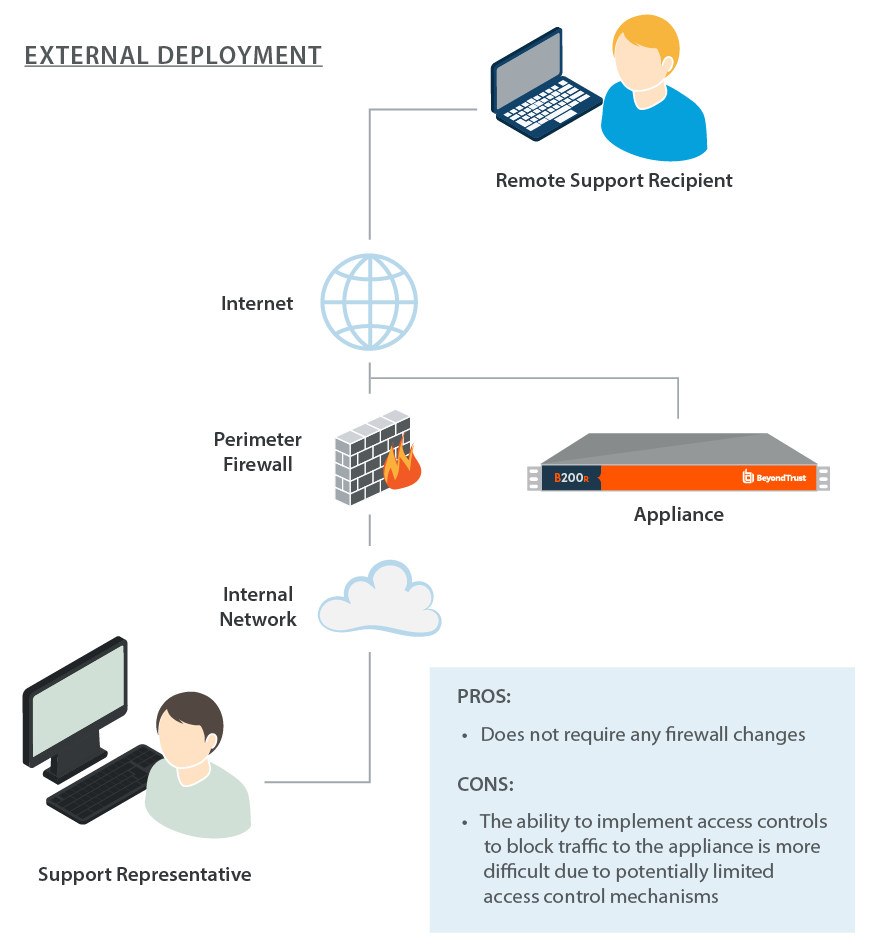
External Deployment: In situations where a DMZ does not exist and is not possible due to technical or business constraints, the B Series Appliance may be deployed external to the perimeter firewall. The B Series Appliance consists of a hardened operating system and applications that are designed to be directly accessible.
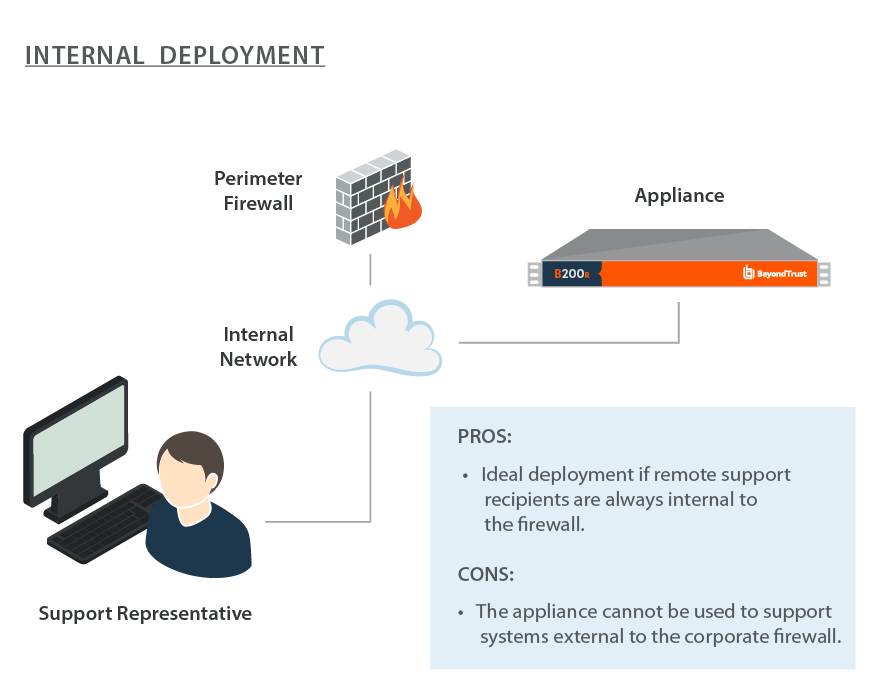
Internal Deployment: Deploying the B Series Appliance on an internal network segment is ideal when the client base is completely internal or accessible through a VPN. No firewall changes are required because the device and all of the supported clients are internal to the firewall. In environments where the supported users or systems are external to the firewall, BeyondTrust recommends this deployment location only in the event that a DMZ does not exist or when the B Series Appliance cannot be deployed externally. An internal deployment of the B Series Appliance requires numerous changes to the environment and a solid understanding of perimeter firewall controls and Network Address Translation.