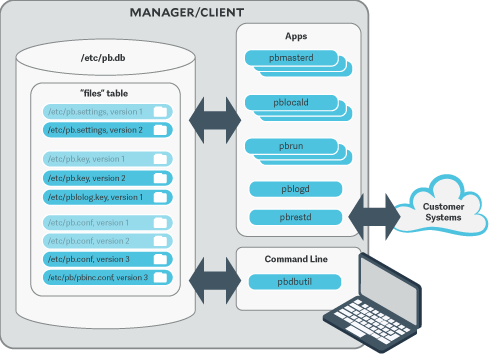
Configuration and Settings Database
The latest version of
To use the
# pbdbutil --cfg -i /etc/pb.settings /opt/pbul/policies/pb.conf /etc/pb.key
{"fname":"/etc/pb.settings","version":1}# pbdbutil --cfg -i /etc/pb.settings /etc/pb.rest.key
{"fname":"/etc/pb.settings","version":1}
{"fname":"/etc/pb.rest.key","version":1}
As soon as the files are imported they are versioned and every EPM-UL binary uses the current database copy in preference to the existing files. The existing file is renamed and a comment inserted at the top of the file as an aide-memoire.
Because the database now stores the imported files, we recommend the original files are moved as a backup. The backup will also serve as a reminder that these files no longer represent the current version.
To make changes to the files, export them, make the changes, and re-import the files:
# pbdbutil --cfg -e /etc/pb.settings
{"fname":"/etc/pb.settings","version":"#"}
# vi /etc/pb.settings
# pbdbutil --cfg -i /etc/pb.settings
{"fname":"/etc/pb.settings","version":2}
The version is incremented, and the current version stored.
Once the administrator is happy with a set of configuration files, these files may all be tagged together at their current version. This allows an administrator to retrieve all the tagged files at their respective versions at a later date. To tag a group of files, use pbdbutil --cfg -t:
# pbdbutil --cfg -l
{"version":1,"pathname":"/opt/pbul/policies/pb.conf","deleted":0,"created":"2018-05-21 14:26:51"}
{"version":2,"pathname":"/etc/pb.settings","deleted":0,"created":"2018-05-21 14:26:48"}
# pbdbutil --cfg -t "working" /etc/pb.settings /opt/pbul/policies/pb.conf
{"fname":"/etc/pb.settings","tag":"working","version":"#"}
{"fname":"/opt/pbul/policies/pb.conf","tag":"working","version":"#"}
The administrator can then export the files as a group:
# pbdbutil --cfg -l
{"version":1,"pathname":"/opt/pbul/policies/pb.conf","deleted":0,"created":"2018-05-21 14:26:51"}
{"version":2,"pathname":"/etc/pb.settings","deleted":0,"created":"2018-05-21 14:26:48"}
# pbdbutil --cfg -l /etc/pb.settings
{"pathname":"/etc/pb.settings","version":1,"tag":null,"deleted":0,"created ":"2018-05-21 14:26:46"}
{"pathname":"/etc/pb.settings","version":2,"tag":"working","deleted":0,"created":"2018-05-21 14:26:48"}
# pbdbutil --cfg -e -V working
{"fname":"/etc/pb.conf","version":"#"}
{"fname":"/etc/pb.settings","version":"#"}
For more information on other options to import, export, tag and diff database configuration files, see
Database Settings
databasedir
- Version 9.3.0 and earlier: databasedir setting not available.
- Version 9.4.0 and later: databasedir setting available.
The databasedir setting is used to specify the default path to databases used within the product, that are specified with a relative path.
databasedir /opt/pbul/dbs servicedb pbsvc.db
The example above configures the service database to be /opt/pbul/dbs/pbsvc.db. However,
databasedir /opt/pbul/dbs servicedb /etc/pbsvc.db
does not affect servicedb
Default
databasedir /opt/<prefix>pbul<suffix>/dbs
Used On
All hosts
databaselocktimeouts
- Version 10.0.1 and earlier: databaselocktimeouts setting not available.
- Version 10.1.0 and later: databaselocktimeouts setting available.
The databaselocktimeouts setting is used to specify the database timeout values for all the various services with EPM-UL. Busy systems can sometimes produce delays in processing data because of contention for database resources. Usually a service will timeout on the specific database and return an error. However, this may not always be the best course of action.
The current list of services include:
- license
- rns
- dbsync
- akapolicy
- iologidx
- restkey
- fim
- event
- logcache
- rbp
- sudo
- sched
- polpvar
- logarchive
- intprod
- clientreg
- pbpolicy
There is also a default service that is applied when a more specific setting has not been configured.
Values take the format of service=<delay>,<retries>, where delay is in microseconds.
databaselocktimeouts default=1000,30 fim=2000,60 rbp=500,10
Default
No default value
Used On
All hosts
lockfileexpiry
Configuration and settings files are centrally managed by EPM-UL using a database. Administrators are allowed to lock the file(s) contained in databases to manage concurrency. The lockfileexpiry setting specifies the length of time (in seconds) before that file lock expires.
lockfileexpiry 45
Default
0
Client Registration
The Client Registration feature facilitates the installation and configuration of new EPM-UL clients into the enterprise. It consists of a centralized Registration Profile service, normally found on the primary server. This service is configured with customized profiles that match the settings required for the installation of hosts that provide differing roles in the organization. When new EPM-UL clients are installed these profiles are retrieved, providing the configuration required to complete the installation.
clntregdb
- Version 9.3.0 and earlier: clntregdb setting not available.
- Version 9.4.0 and later: clntregdb setting available.
The clntergdb option specifies the path to the Client Registration database. This file is created in databasedir by default, unless the file name starts with /.
clntregdb /etc/pbclntreg.db
Default
clntregdb /opt/<prefix>pbul<suffix>/dbs/pbregclnt.db
Used On
Primary servers
Example Client Registration Procedure
- Install the primary license server, making sure that the REST services are installed. Make a note of the port number of the REST service. Also make sure that if the host has any firewalls installed, that this TCP port is unblocked.
- After main installation is complete check that the REST service is running (ps -ef | grep pbconfigd), and if it isn't, follow normal procedures to start the service.
- Create a REST application ID and key.
pbdbutil --rest -g appid
{"appkey":"934bbab5-503e-4c40-8486-90c748142431"}
- Ensure the pb.settings file has all the necessary configuration, including encryption and encryption keys defined.
- Now we are ready for a client install. Run the normal pbinstall on the client and when asked whether to use Client Registration, answer yes, and provide responses to the Client Registration configuration questions.
Do you wish to utilize Client Registration? [yes] Enter the Application ID generated on the Primary License Server: appid Enter the Application Key generated on the Primary License Server: 934bbab5-503e-4c40-8486-90c748142431 Enter the Primary License Server address/domain name for registering clients: pbmasterhost.mydomain.com Enter the Primary License Server REST TCP/IP port [24351]: 24351 Enter the Registration Client Profile name [default]: default
- pbinstall then defaults all the configuration of the install to the retrieved pb.settings and transfers all the necessary keyfiles automatically.