Configure Event Subscriptions
The Windows Event Forwarding architecture stores the subscription definition on the event collector to reduce the number of touch-points in case a subscription needs to be created or modified. The following subscription is configured so that event source computers retrieve subscriptions from the event collector host (source-initiated subscriptions).
Subscriptions are defined on the event collector through the new Event Viewer user interface by selecting the Create Subscription action, when the Subscriptions node is selected. The subscription may also be created via the WECUTIL command-line utility.
Configuration Steps:
- On the event collector, open the Event Viewer.
- Navigate to the Subscriptions node.
- From the menu bar, choose Action > Create Subscription...
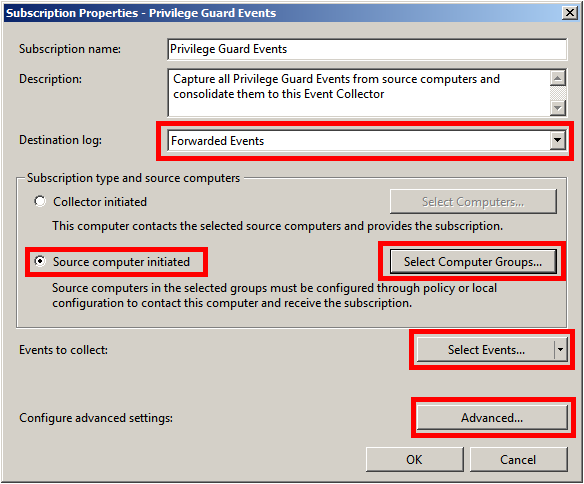
- The Subscriptions Properties dialog box appears.
From here, you can specify a name, description, and the destination log (where the events are collected).
- Select Forwarded Events for the destination log.
- Select Source Computer Initiated (as Group Policy configures the source computer to contact the event collector for subscriptions settings).
The Subscription type can also be configured as Collector initiated. In this case, source computers must be manually added to the subscription either through the subscription configuration or the WECUTIL command-line utility (which can also be scripted using PowerShell). We recommend that Source Computer Initiated be used, as this configuration is the most scalable.
- Click Select Computer Groups.
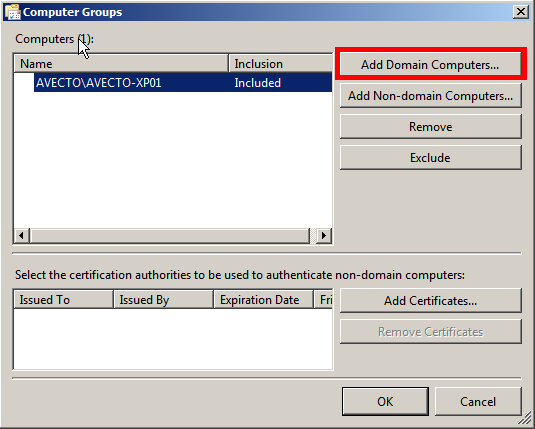
- Click Add Domain Computers and select the source computers.
We recommend adding a computer group that includes the required computer accounts, such as the Domain Computers group.
- Click OK on the Computer Groups dialog box.
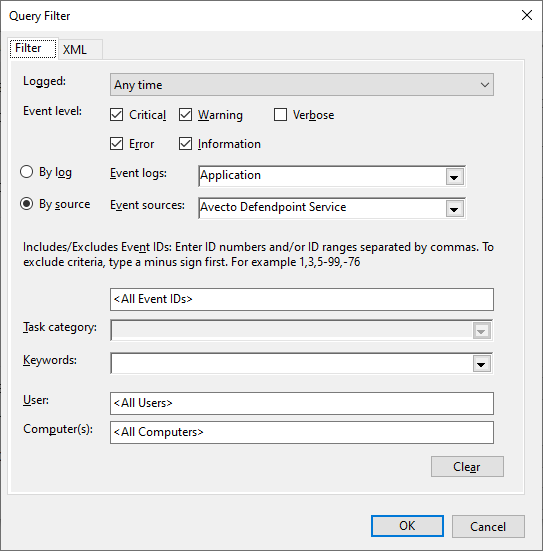
- Click Select Events. The By Source field varies depending on where the logs are saved.
- Configure the following Query Filter:
- Event Level = Critical, Warning, Error, Information.
- By Source = Avecto Defendpoint Service (when using the default log location Windows Logs\Application).
- By Source = BeyondTrust Endpoint Privilege Management (when using the log location Application and Services Logs\BeyondTrust Privilege Management).
In a production environment, it may be advantageous to gather all events from the Application and System logs with a level of Critical, Error, or Warning. This event scope can be expanded to gather all events from these logs or even add additional logs (like the Security log).
If the Endpoint Privilege Management Agent is not installed on the event collector, you cannot select BeyondTrust Endpoint Privilege Management Service as the event source. We recommend the Endpoint Privilege Management Agent be installed and the BeyondTrust Endpoint Privilege Management Service set to disabled to deactivate the agent, if desired. If it is not possible to install the agent, the subscription can be configured to collect events from the Application event log and filtered on event IDs 100 to 501. See the Endpoint Privilege Management Administration Guide to verify the minimum and maximum event IDs created by the Endpoint Privilege Management Service, as these are subject to change.
- Click OK on the Query Filter dialog box.
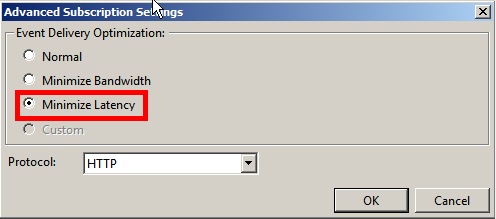
- Click Advanced on the Subscriptions Properties dialog box.
- Select Minimize Latency.
- Normal: This option ensures reliable delivery of events and does not attempt to conserve bandwidth. It is the appropriate choice unless you need tighter control over bandwidth usage or need forwarded events delivered as quickly as possible. It uses pull delivery mode, batches 5 items at a time, and sets a batch timeout of 15 minutes.
- Minimize Bandwidth: This option ensures network bandwidth is strictly controlled for event delivery. It is an appropriate choice if you want to limit the frequency of network connections made to deliver events. It uses push delivery mode and sets a batch timeout of 6 hours. In addition, it uses a heartbeat interval of 6 hours.
- Minimize Latency: This option ensures events are delivered with minimal delay. It is an appropriate choice if you are collecting alerts or critical events. It uses push delivery mode and sets a batch timeout of 30 seconds.
- Protocol: HTTPS can be used to secure the communication channel. However, this requires additional configuration steps and requires the Event Collector to use a certificate.
- Click OK on the Advanced Subscription dialog box.
- Click OK on the Subscription Properties dialog box.
For more information, see Additional Resources.