Use Smart Card Authentication
If multi-factor authentication (MFA) using smart cards is implemented in your environment, you can configure Endpoint Privilege Management for Mac to work with your MFA implementation.
Endpoint Privilege Management for Mac supports smart card and Yubikey.
Predeployment Setup
To use Endpoint Privilege Management for Mac with a policy that enforces using smart cards on a local machine, you must configure the endpoints to allow unmapped users to authenticate using passwords only.
Failure to configure endpoints to allow users to authenticate using passwords only will prevent Endpoint Privilege Management for Mac from authorizing controlled rights on behalf of the user.
Run the following command on the endpoint. You can run the command manually or run a script distributed by an MDM solution.
If running the command manually, prepend sudo to the line.
defaults write /Library/Preferences/com.apple.security.smartcard allowUnmappedUsers -int 1
Configure Endpoint Privilege Management for Mac Messaging
After your estate is set up to use MFA, and Endpoint Privilege Management for Mac is successfully deployed, you can require users to enter their smart card PIN for any action which can be controlled by Endpoint Privilege Management for Mac.
MFA with smart card supports the following authorization types:
- User Must Authorize: The user must authenticate before proceeding.
- Designated user must authorize: A designated user must authenticate an action. The designated user authorization type cannot be used with sudo rules.
For more information, see Authentication and Authorization Settings.
For example, to enforce low flexibility users to authenticate using their smart card PIN if they want to install a downloaded application to /Applications. You can create a message in the Policy Editor and assign a name such as Authorize Application Install (PIN required).
To configure messaging on a policy for MFA:
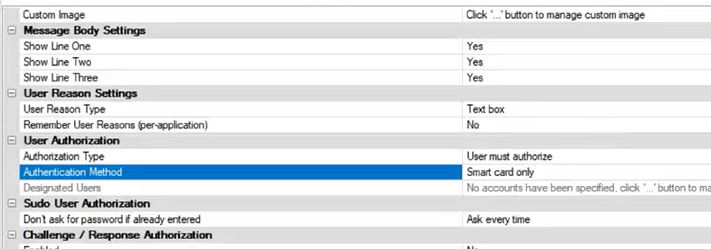
- Go to the Message Designer.
- Set the Authorization Type setting to one of the following: User Must Authorize or Designated user must authorize.
- Set the Authentication Method setting to Any or Smart card only to enable smart card messages.
- After you create the message, find your existing application assignment in your Workstyle which prompts the user for installing application bundles in to /Applications.
- Select your message from the End User Message setting.
MFA Support in Endpoint Privilege Management for Mac sudo Rules
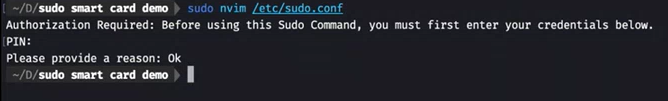
Smart card support can also be implemented in a command line scenario. You can configure an Endpoint Privilege Management for Mac Workstyle with a sudo command Application Rule. When there is a match on the rule, the user must correctly enter their smart card PIN before they can proceed.
The high-level overview to set up smart card authentication with a sudo rule:
- Create your Application Group. Add the application you want to run using sudo.
- Customize your message in the Message Designer. Be sure to set the following:
- Authentication type: User must authorize
- Authentication Method: Smart card only
-
Create the Application Rule in Workstyles. Set up the Application Rule and select the message you created.
The following screen capture shows an example where nvim is configured to run with sudo and smart card authentication. Access is only permitted after the user correctly enters the smart card PIN.