Use Smart Rule Filters and Smart Groups
There are many built-in filters available that you can use when creating Smart Rules. You can also create address groups or Active Directory queries from the Configuration page to use as Smart Rule filters.
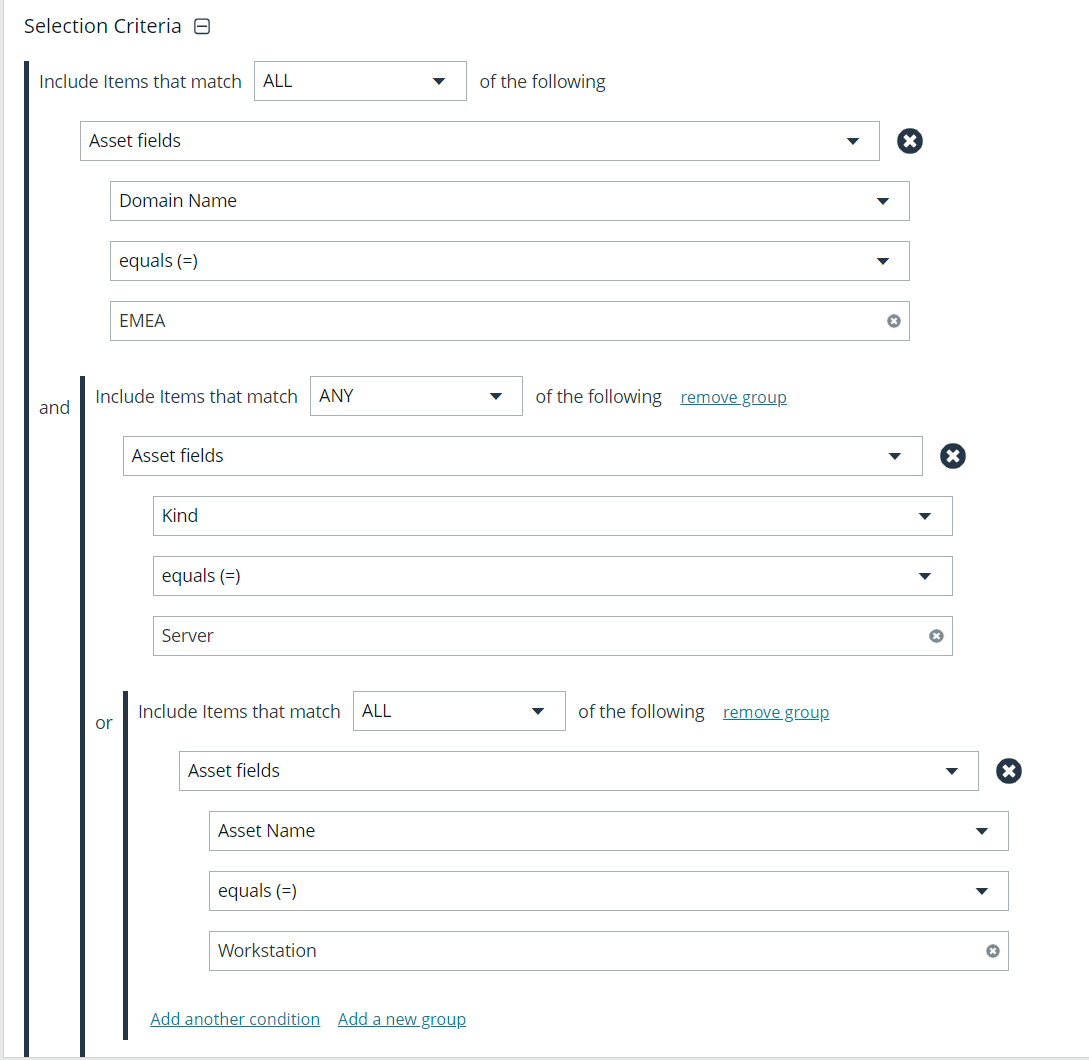
You can use more than one filter to refine or extend the scope of assets in a Smart Rule. Filters can be joined with and (match ALL criteria) or or (match ANY criteria) conditions. If you select to match ALL, every indented filter must be set to True for an asset to be included. If you select to match ANY, only one of the indented filter items must be set to True for an asset to be included. The screen capture shows a filter example that includes all assets in the EMEA domain that are either servers or workstations.
Smart Rule Filters
Asset Smart Rule Filters
|
Address Group |
Create a group of IP addresses. |
|
Asset Fields |
Group the Smart Rule by asset fields, such as, Asset Name, Domain or DNS, Risk, and Kind. You can include more than one asset field filter in the Smart Rule to refine the results. |
|
Assigned Attributes |
Create a filter based on an attribute. If the attribute is unassigned on a particular asset, you can choose to include or exclude the asset from the rule. |
|
Child Smart Rule |
You can reuse a Smart Rule to save time when creating new Smart Rules. This is especially useful if the Smart Rule is a complicated set of filters. Reusing a Smart Rule further refines the assets that will be a part of the Smart Rule. |
|
Cloud Assets |
Filter assets on the cloud connector. |
| Directory Query |
Create an Active Directory or an LDAP query to include or exclude assets in the selected domain. |
|
Installed Software |
Filter on any combination of installed software. |
|
Operating System |
Filter on any combination of OS. Operating systems included in the list are those detected in your network. Assets with no OS detected, can be included or excluded from the rule. |
|
Processes |
Filter on any combination of processes. |
|
Services |
Filter by any combination of services. |
| Software Version | Filter by software version. The software that you can filter on is determined by the software that is discovered during the scan. |
| User Account Attribute |
Filters user accounts by SID or privilege. You can filter on both. If either value is not selected then it will be ignored. Using this filter you can determine if any users have administrator privileges that might no longer be required. You can create a Smart Rule using this filter and set the email alert action to notify you when a user account with admin privileges is detected. |
|
Windows Events |
Filter by Windows events that are available in the Windows Event Viewer. For example, Application, Security, or System. |
|
Workgroup |
Filter by workgroup. |
For more information, please see the following:
Predefined Smart Group Categories
|
Agents and Scanners |
Detects assets where BeyondInsight scanners are deployed. |
|
Assets and Devices |
Includes default Smart Groups for all assets and all assets labeled as workstations. |
|
Intelligent Alerts |
Includes Smart Groups that detect assets added since the previous day, and mobile assets with critical vulnerabilities. Intelligent Alerts are inactive by default. |
|
Servers |
Includes Smart Groups that detect mail server, web server, database server, domain controller, and SCADA assets. Only the Web Servers Smart Group is marked as active. |
|
Virtualized Devices |
Includes Smart Groups for virtual environments, including Microsoft Hyper-V and Parallels. Assets detected as virtual environments belong to these Smart Groups. This default category also includes two Smart Groups: Virtual Servers and Virtual Workstations. Assets that are servers or workstations might not be detected, and as a result, not be included in the Smart Group. For example, the asset might be a router or unknown, resulting in exclusion from the Smart Group. |
- Microsoft Hyper-V
- Parallels
- Recent Virtual Servers not in Password Safe
- Virtual Servers
- Virtual Workstations
- VMware vSphere
- Xen