Create or Modify a PMUL Servers Rule
Before Privilege Management for Unix & Linux Servers rules can be deployed, a Privilege Management for Unix & Linux Servers configuration file must be defined.
For more information, see Privilege Management for Unix & Linux Servers Configuration.
To create a Privilege Management for Unix & Linux Servers rule or to modify an existing Privilege Management for Unix & Linux Servers rule, do the following:
- In the Create Policy Rules Properties dialog box:
- To create a new Privilege Management for Unix & Linux Servers rule, click Add.
- To modify an existing Privilege Management for Unix & Linux Servers rule, select the rule and then click Edit.
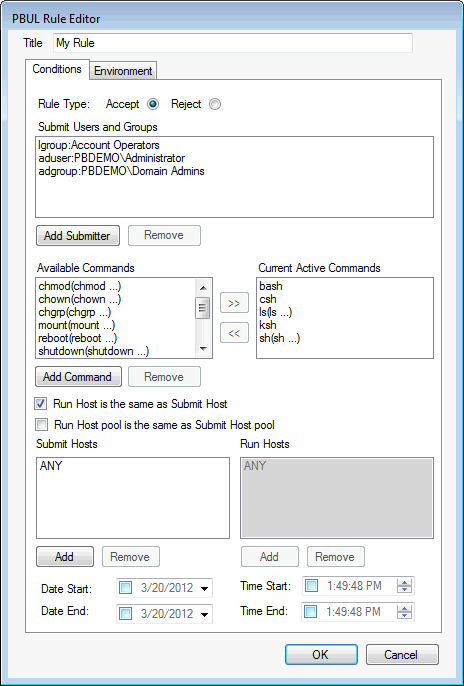
- Enter a name for the rule.
- On the Conditions tab, select the rule type radio button. Choose from Accept or Reject.
- To add a user or group to be managed by the rule, click Add Submitter.
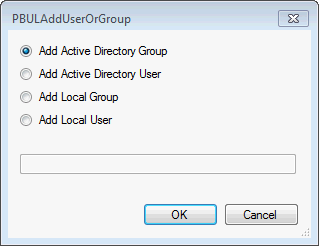
- Select a type of user or group to add. If adding an Active Directory user or group, click OK, enter the name of the user or group, and then click OK.
- If adding a local user or group, type the name in the box and click OK.
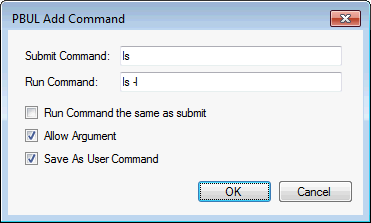
- Click Add Command and select from the following:
- Submit Command: Enter the command as a submitter would type it. You can include arguments. If you want to allow the user to include additional arguments with the command at runtime, check the Allow Argument box.
- Run Command: Enter the command that runs when a submitter types the Submit Command. You can include arguments.
- Run Command the same as submit: Check the box when you want the command the same as Submit Command.
- Run Command the same as Submit: If this is not selected, you can effectively create an alias for a command for submitters.
- Save As User Command: Check the box to use the command with other PBUL rules.
- Click OK to add the command.
You can remove commands that you add, but you cannot remove the default commands provided with AD Bridge.
- Select the commands that you want to run when the rule is activated.
- Click >> to move the command to the Current Active Commands list.
- To remove the command from the Current Active Commands list, click <<.
- Select the computers that will be Submit Hosts (commands in the rule are run by submitters) and Run Hosts (commands entered by submitters are run).
- Run Host is the same as Submit Host: (Optional). The computer used as the Run Host must be the same computer used as the Submit Host; check the box.
- Run Host pool is the same as Submit Host pool: (Optional). The selected computers are used as both Submit Hosts and Run Hosts; check the box.
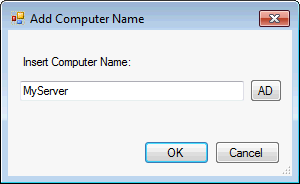
- Submit Hosts and Run Hosts: In the Submit Hosts or Run Hosts areas, click Add. Type a computer name or click ADD to search Active Directory for a computer. You can enter multiple computer names separated by commas.
- (Optional). You can limit when the rule is active to between specified dates or times of day, delay when a rule will become active, or specify an expiration for a rule. For example, to make the rule active only between 8:00AM and 7:00PM, check the Time Start box and enter 8:00:00 AM. Then check the Time End box and enter 7:00:00 PM.
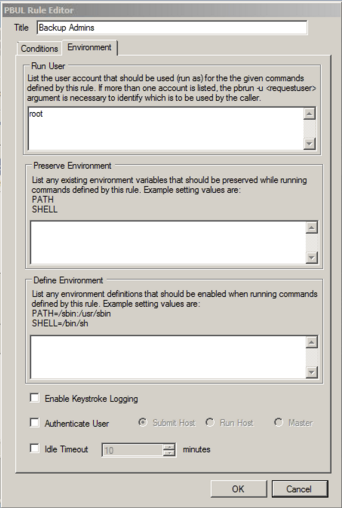
- Optional. Click the Environment tab, and then enter information for the following:
- Run User: Enter the user account to use to run the commands in this rule on the Run Host. The default account is root. If you change the account, ensure that the account has the permissions necessary to run the commands in the rule and that the account exists on the Run Hosts.
- Preserve Environment : (Optional). List any Unix or Linux environment variables that you want to remain unchanged by the effect of this rule when commands are run. Environment variables can alter which libraries are loaded for the session.
- Define Environment: (Optional). Enter the names and values of any Unix or Linux environment variables that you want to explicitly define when this rule is used to run commands.
- Enable Keystroke Logging: (Optional). To enable keystroke logging, check this box. If selected, by default, keystrokes are logged to a separate log file for each command instance. Advanced administrators can change the path and file name format of these log files by changing the pb.conf file. If the default pb.conf file is used, keystroke log files are saved to file names beginning with /var/adm/pb.iolog.
- Authenticate User: (Optional). To display a password prompt to the user and authenticate the user before a command is run, check this box. Select where authentication occurs: Submit Host, Run Host, or the Master Server. This setting can provide additional protection against unauthorized users if an authorized user neglects to lock their computer before stepping away from it.
- Idle Timeout: (Optional). To force a timeout so that a long-running command cannot continue indefinitely, check this box and enter the maximum number of minutes. For example, if you are configuring rules that allow users to create a shell session using pbsh or pbksh, you can use this setting to ensure that this elevated access eventually expires if idle.
- Click OK.